Chris Hoffman
Contributing since August, 2010
-
2888articles
Page 75
About Chris Hoffman
Chris Hoffman is the former Editor-in-Chief of How-To Geek. Chris has personally written over 2,000 articles that have been read more than one billion times---and that's just here at How-To Geek.
With over a decade of writing experience in the field of technology, Chris has written for a variety of publications including The New York Times, Reader's Digest, IDG's PCWorld, Digital Trends, and MakeUseOf. Beyond the web, his work has appeared in the print edition of The New York Times (September 9, 2019) and in PCWorld's print magazines, specifically in the August 2013 and July 2013 editions, where his story was on the cover. He also wrote the USA's most-saved article of 2021, according to Pocket.
Chris was a PCWorld columnist for two years. He founded PCWorld's "World Beyond Windows" column, which covered the latest developments in open-source operating systems like Linux and Chrome OS. Beyond the column, he wrote about everything from Windows to tech travel tips.
The news he's broken has been covered by outlets like the BBC, The Verge, Slate, Gizmodo, Engadget, TechCrunch, Digital Trends, ZDNet, The Next Web, and Techmeme. Instructional tutorials he's written have been linked to by organizations like The New York Times, Wirecutter, Lifehacker, the BBC, CNET, Ars Technica, and John Gruber's Daring Fireball. His roundups of new features in Windows 10 updates have been called "the most detailed, useful Windows version previews of anyone on the web" and covered by prominent Windows journalists like Paul Thurrott and Mary Jo Foley on TWiT's Windows Weekly. His work has even appeared on the front page of Reddit.
Articles he's written have been used as a source for everything from books like Team Human by Douglas Rushkoff, media theory professor at the City University of New York's Queens College and CNN contributor, to university textbooks and even late-night TV shows like Comedy Central's @midnight with Chris Hardwick.
Starting in 2015, Chris attended the Computer Electronics Show (CES) in Las Vegas for five years running. At CES 2018, he broke the news about Kodak's "KashMiner" Bitcoin mining scheme with a viral tweet. A wave of negative publicity ensued, with coverage on BuzzFeed News, CNBC, the BBC, and TechCrunch. The company's project was later reportedly shut down by the U.S. Securities and Exchange Commission.
In addition to his extensive writing experience, Chris has been interviewed as a technology expert on TV news and radio shows. He gave advice on dark web scans on Miami's NBC 6, discussed Windows XP's demise on WGN-TV's Midday News in Chicago, and shared his CES experiences on WJR-AM's Guy Gordon Show in Detroit.
Chris also ran MakeUseOf's email newsletter for two years. Nearly 400,000 subscribers received the newsletter complete with a handwritten tip every day.
Latest Articles
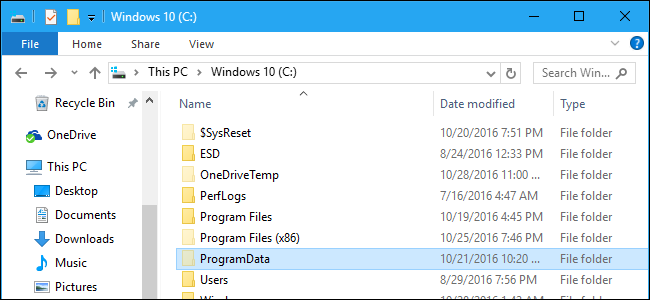
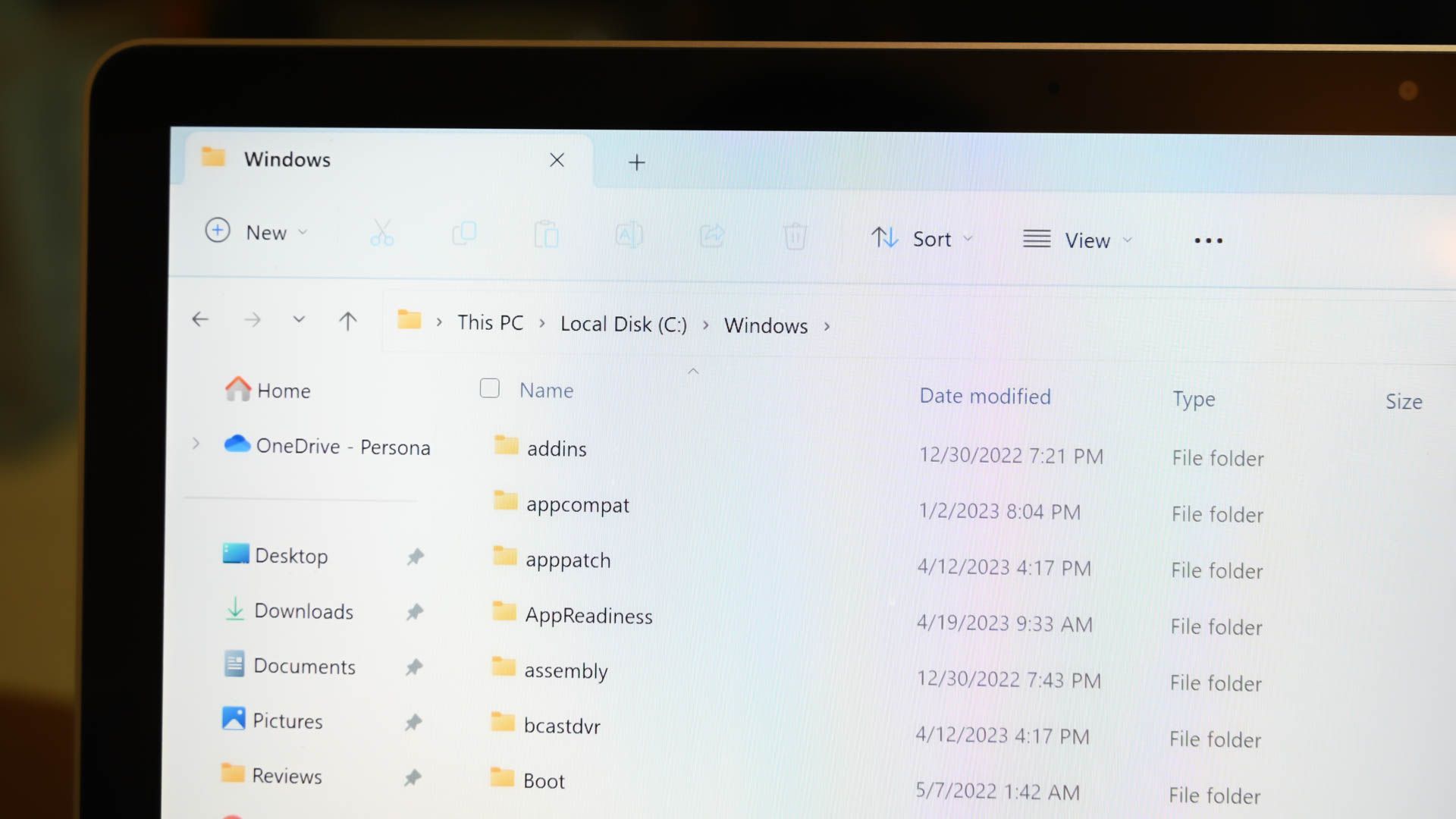
What Is the ProgramData Folder in Windows?
On modern versions of Windows, you'll see a "ProgramData" folder on your system drive---usually the C: drive.

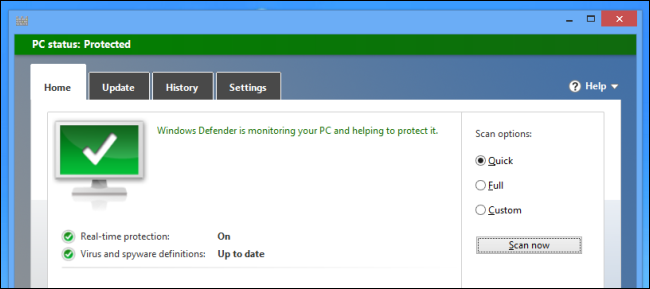
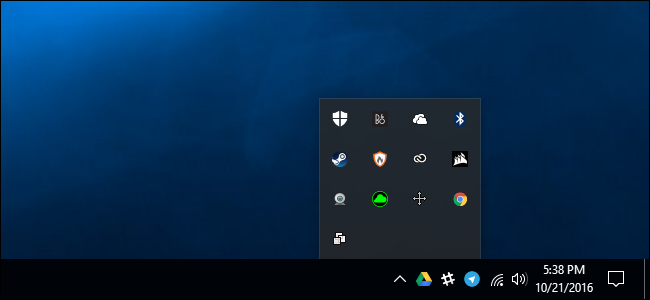
How to Build Your Own Internet Security Suite For Free
You don't really need a full Internet security suite.
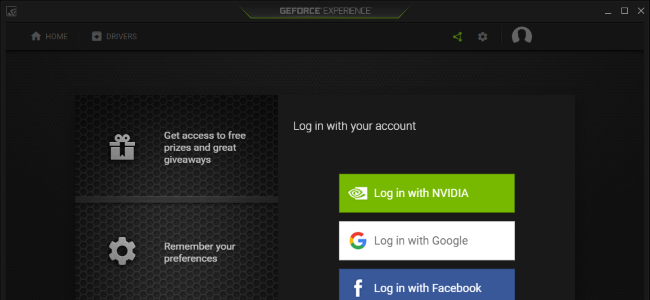
Relax, NVIDIA's Telemetry Didn't Just Start Spying on You
Gamers are accusing NVIDIA's new drivers of spying on you, collecting more data with new telemetry services.
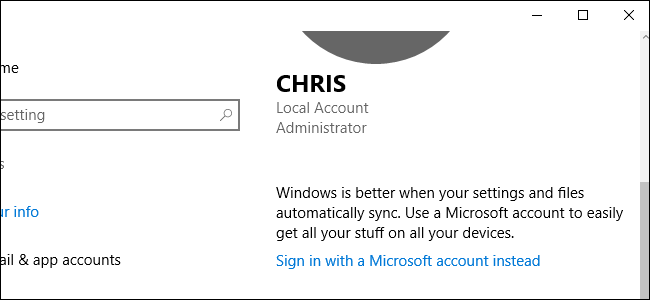
All the Features That Require a Microsoft Account in Windows 10
Windows 10, like Windows 8 before it, is integrated with Microsoft's online services.
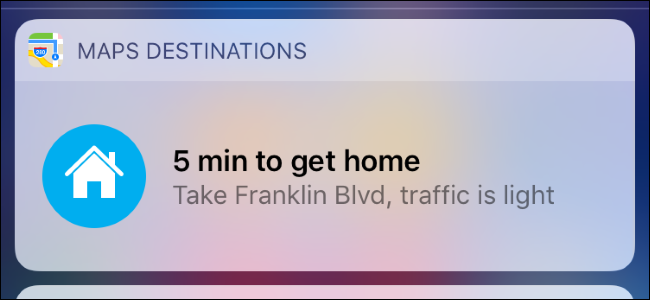
How to Change Your Home Address in Apple Maps
Apple Maps doesn't automatically detect your Home address.
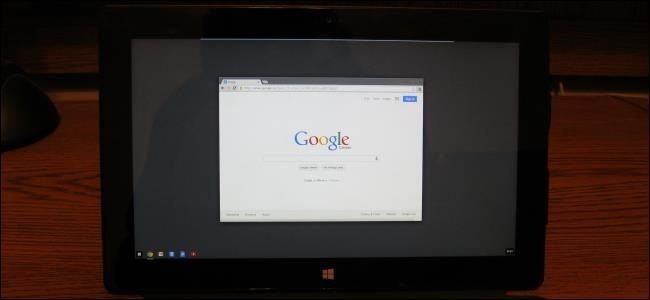
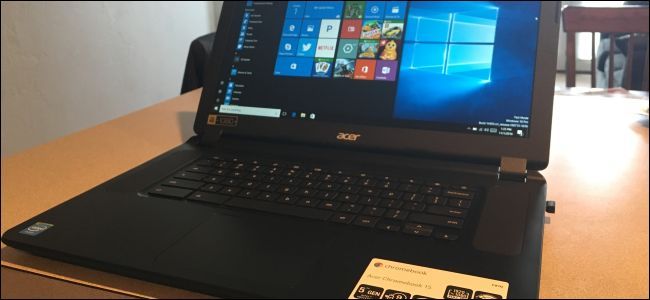
How to Turn a Windows 8 PC Into a Chromebook
Do you prefer Google Chrome to Microsoft's Windows 8 apps? Well, you're in luck, even if you have a Windows 8 PC.

The Complete Guide to Improving Your PC Gaming Performance
If you're new to the world of PC gaming, it can all seem a bit complicated.

How Secure Boot Works on Windows 10, and What It Means for Linux
Modern PCs ship with a feature called "Secure Boot" enabled.
How to Batch Rename Multiple Files in Windows
Got a bunch of files you want to rename, but don't want to go through them each one by one? Windows provides more ways to do this than you may realize.

The Ultimate Guide to Installing Incompatible Android Apps from Google Play
Android developers can restrict their apps to certain devices, countries, and minimum versions of Android.

How to Install Ubuntu Linux on Your Chromebook with Crouton
Chromebooks aren’t “just a browser”—they’re Linux laptops.
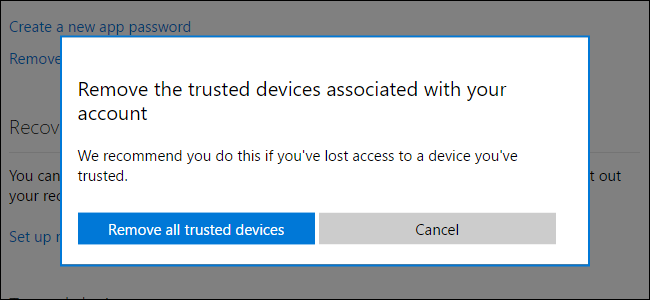
How "Trusted Devices" Work on Windows 10 (and Why You No Longer Need to "Trust This PC")
Windows 8 asked you to "Trust This PC" after you signed in with a Microsoft account.
Debunking Battery Life Myths for Mobile Phones, Tablets, and Laptops
Batteries need to be cared for properly -- they're a critical part of our mobile devices and battery technology hasn't advanced as fast as other technologies.
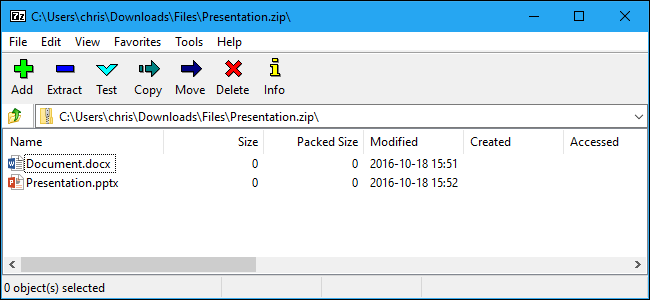
The Best File Archiving Program for Windows
Need to extract an archive or compress some files? Avoid big-name programs like WinZip and WinRAR, which are packed with nags and advertisements.
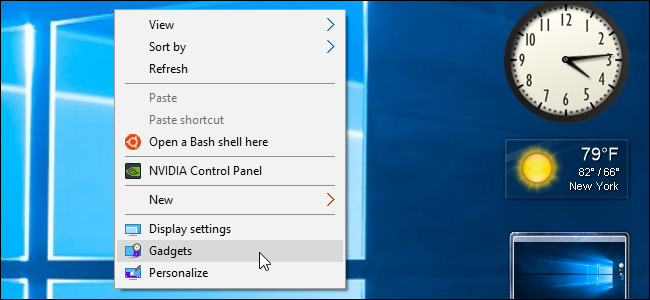
How to Add Gadgets Back to Windows 8 and 10 (and Why You Probably Shouldn't)
Desktop gadgets and the Windows Sidebar were a big hallmark feature in Windows Vista and Windows 7.
How to Easily Put a Windows PC into Kiosk Mode With Assigned Access
Assigned Access allows you to easily lock a Windows PC to a single application of your choice.
How to Pair a Bluetooth Device to Your Computer, Tablet, or Phone
Wireless devices with Bluetooth radios must be "paired" with each other before they can communicate.