Quick Links
Key Takeaways
Advertisers use a smorgasbord of tricks to follow you across the web including tracking your IP, using cookies, identifying you from your browser fingerprint, and even headers injected at a network level by your ISP. It's near-impossible to avoid it completely, but using a VPN and secure browser will regain some privacy.
Online privacy is a myth. Whether you know it or not, on the internet you're daily served tracking cookies, device fingerprinting scripts, internet service provider super cookies, and more tricks designed to get you to hand over as much data as possible. Here's how these tools and schemes work.
Common Methods Used to Track You
There is a multitude of ways that advertisers can track you across the web. Advertisers cast a wide net and use many different techniques at once to gather information about you, even when you're browsing incognito or using another device like a smartphone or tablet.
Your IP address identifies you across the web, like when logging in to your email account or visiting a shopping website. It's the numerical address associated with your current connection, whether that's your home internet or a mobile device connecting via cellular. IP addresses can be and are used to track you, both as a security precaution (for example, in Gmail to list recent device logins) and to identify patterns that can help identify you as an individual.
Perhaps the most commonly understood tracking technique is the tracking cookie. These are small files that live on your device and identify you across different websites, allowing advertisers to identify you even if you've never visited a particular website before.
URL trackers are used to gather information about how you arrived at a destination. If you click on a link in an email like a newsletter or promotion, URL trackers can be used to tell whether the email campaign was successful and build a larger picture of how visitors are landing on the site.
Tracking pixels are commonly associated with email clients, but they can just as easily be deployed on the web for similar purposes. A unique pixel can be served to each visitor, which is used to gather your IP address. Though you can block cookies and adverts with browser settings or extensions, blocking tracking pixels is much harder since your browser can't tell them apart from standard content.
More Advanced Tracking Techniques
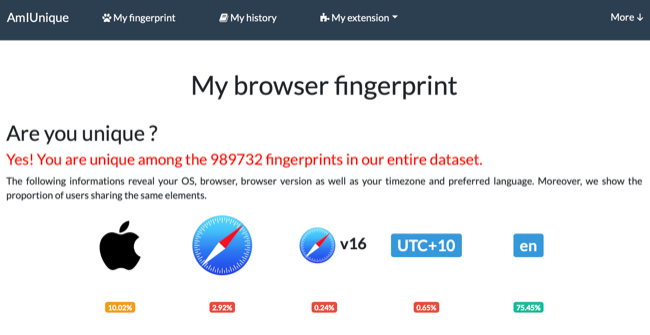
A more advanced technique known as device or browser fingerprinting uses the unique impression or "fingerprint" created by your device to single you out in the crowd. This includes your operating system, browser and version, screen resolution, which extensions you are using, your timezone, preferred language, or even technical specifications like your computer hardware or driver versions.
This is also how canvas fingerprinting (and WebGL fingerprinting) works. A script that runs in the background on a web page instructs your browser to draw an invisible image. Since every device draws the image in a unique way (depending on the variables used to gather your fingerprint) the image can be used to link your data across websites, without the need to store anything on your device.
If you're skeptical that your personal device isn't unique enough for an advertiser to single you out in a crowd, visit AmIUnique to see for yourself. The sheer volume of data left behind when visiting a website can work against you to single you out as a unique user.
Lastly, there are so-called "super cookies" that don't use local storage but are instead injected at a network level by your internet service provider (ISP) as a Unique Identifier Header (UIDH). This information can be used by your ISP to track browsing data but also accessed by third parties to identify you across the web.
You can't delete super cookies since they exist at a network level. Super cookies can be used to restore cookies you have already deleted by providing another point of identification for advertisers to use. Advertising blockers or privacy-conscious browsers can't stop them either, but you may be able to opt out at an ISP level. In the US, Verizon customers can opt out by logging in and selecting "No, I don't want to participate in Relevant Mobile Advertising" under privacy settings.
How Your Data Is Used
First-party trackers commonly gather information that relates to their own services. These could be preferences that determine what you see when you use their website like your location, language, and so on. This type of data makes your experience more convenient.
Third parties like advertisers track you across the web to gather as much data about your browsing habits as possible. Data is the new gold, and there is a lot of money to be made from understanding a user's browsing habits from a marketer's perspective.
This information is ultimately compiled into a database to understand how you behave, what your interests are, where you live, and so on. This may include intrusive information like political beliefs, health conditions, or anything else you wouldn't be comfortable with an advertiser knowing about you.
The most common use for this sort of third-party data is to serve advertisements. The more an advertiser knows about you, the more likely they'll succeed at surfacing an ad that appeals to you. Rather than showing an ad for a product that has no relevance to you, advertisers can surface an appealing product that's relevant to your region at a convenient time of day to entice you to click.
These preferences make up an important part of the core product used to sell advertising. The more data points an advertiser has, the more they have to offer potential clients. This lets clients limit advertisements to select cohorts, which should yield a better click rate, and repeat custom for the advertising company.
Is Gathered Data Really Anonymous?
There are potentially more nefarious uses for this data. Advertisers often relay that gathered data is anonymous or anonymized, but this isn't strictly true. Common practice dictates that gathered data is stored against a pseudonym (like a random string of letters and numbers) rather than a real-world identifier. The potential for this data to be linked to your identity, email address, or phone number isn't beyond the realm of possibility.
Consider what could happen if an insurance company could see your advertising profile or search history. Your premiums could go up if you were at a perceived higher risk merely because you researched a symptom or condition on the web (even if that condition doesn't relate to your own health). This is a nightmare scenario for sure, but as long as a summary of your online activity exists within a private company's database then the threat is present.
Dynamic pricing could also be impacted if a company understands more about you. In the same way that using a VPN to access a travel website from a different country could be used to save money on flights, a travel website understanding circumstances like your financial situation, homeowner status, or travel habits could be used against you to increase prices.
What You Can Do About It
Advertisers don't rely on a single technique to track and identify you, which means you need to take a multi-pronged approach to avoid tracking as much as possible. The easiest thing you can do is to enable Do Not Track in your browser preferences. This relies on third parties honoring your request, but it's a start.
Better still, switch to a browser that provides more control over your privacy. Safari and Firefox block third-party cookies by default, and Safari will even tell you how many trackers were blocked using its Privacy Report function. You can instruct just about every browser to block third-party cookies with a little bit of work.
You can use a tool like Ghostery (available as a standalone browser or web extension) to block trackers and anonymize your browsing experience as much as possible. Go a step further and use Tor at the cost of browsing speed not only defeat trackers but push back against surveillance and censorship too.
DuckDuckGo also has its own browser now, complete with tracking protection and a more private search engine. For search purposes in other browsers, switch to DuckDuckGo instead of Google to stop the world's largest search engine from tracking your queries.
Email is another leaky faucet when it comes to online privacy. DuckDuckGo's @Duck.com email protection removes tracking pixels and offers aliases you can disable at will. Apple Mail already includes robust privacy protection, with iCloud+ users getting access to Hide My Email.
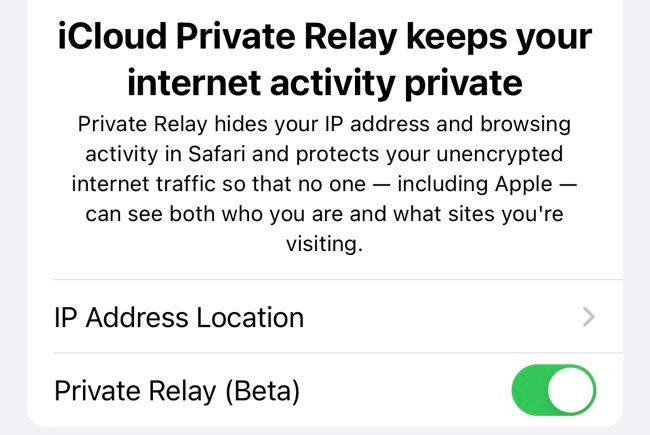
Apple's Private Relay promises to anonymize your web requests in a way that not even Apple knows what you're accessing. Alternatively, use a VPN across the board to encrypt all of your browsing data. Use of a VPN and Private Relay are two different things, so make sure you understand the differences when trying to pick between them.
You can prevent super cookies (UIDH) from working by using exclusively HTTPS websites with valid SSL or TLS certificates. Alternatively, establishing an end-to-end encrypted connection using a VPN will also prevent super cookies from working.
Tracking Is Here to Stay
The privacy implications of online tracking are concerning, to say the least. While you can lock down your browsing experience to a large degree, at some point you have to decide between privacy and convenience.
If you're concerned about privacy we'd recommend using a VPN (like one of our top recommendations), scrutinizing privacy policies, and using a search engine that is more respectful of your privacy.