Quick Links
Have you ever been the victim of identity theft? Ever been hacked? Here’s the first in a series of critical information to help you arm yourself against the surprisingly frightening world of hackers, phishers, and cybercriminals.
Some of our geekier readers will already be familiar with a lot of this material—but maybe you have a grandfather or other relative that could benefit from having this passed on. And if you have your own methods for protecting yourself from hackers and phishers, feel free to share them with other readers in the comments. Otherwise, keep reading—and stay safe.
Why Would Anyone Want to Target Me?
This is a common attitude; it just doesn’t occur to most people that a hacker or cybercriminal would think to target them. Because of this, most ordinary users don’t even think of security. It sounds strange and fanciful…like something in a movie! The reality is quite terrifying—most criminals want to target you because they can, and they can probably get away with it. You don’t have to have millions (or even thousands) of dollars to be a target. Some cybercriminals will target you because you’re vulnerable, and the ones that want your money don’t particularly need a lot of it (although some will take every cent if they can manage).
Who Are these Bad Guys?
Before we take a look at specifics, it’s important to understand who it is that’s looking to take advantage of you. Some of the online threats can come from “script kiddies;” hackers with have no real skill, writing viruses using directions found from Google searches, or using downloadable hacker tools for rudimentary results. They’re more often than not teens or college kids, writing malicious code for kicks. While these people can take advantage of you, they’re not the biggest threat online. There are career criminals out there looking to rob you—and these are the ones you really have to be aware of.
It may sound like hyperbole, but you can quite accurately think of cybercriminals as an internet version of Mafia crime families. Many make their entire living preying on stealing information, credit card numbers, and money from unsuspecting victims. Many are experts, not only at stealing this information, but also from getting caught taking it. Some operations could be small—one or two guys and a few cheap machines for sending phishing emails or spreading keylogging software. Others can be surprisingly large businesses based around black market sales of illegally obtained credit card numbers.
What Is A Hacker?
If you were skeptical before, hopefully now you’re convinced that it’s worth your while to protect yourself from the myriad of people hoping to steal from you online. But that brings us to our next question—just what is a hacker? If you’ve seen any movie since the popularization of the internet… well, you might think you know, but, if you’re like most people, you’re more wrong than you know.
The original meaning of “hacker” applied to the clever computer users, and may have been first coined by MIT engineers like Richard Stallman. These hackers were known for their curiosity and programming skills, testing the limits of the systems of their day. “Hacker” has gradually developed a darker meaning, generally associated with the so-called “Black Hat” hackers known for cracking security for profit or stealing sensitive information. “White hat” hackers could crack the same systems, and steal the same data, although their aims are what make them different. These “white hats” can be thought of as security experts, searching for flaws in security software in order to attempt to improve it, or to simply point out the flaws.
As most people use the word today, “hackers” are thieves and criminals. It may not be worth your time to read up on the intricacies of cyberwarfare or the ins and outs of security cracking. Most hackers pose a threat to the everyman by stealing sensitive accounts like email, or those that contain information like credit card or bank account numbers. And almost all of that particular kind of account theft comes from cracking or guessing passwords.
Password Strength and Security Cracking: Why You Should Be Afraid
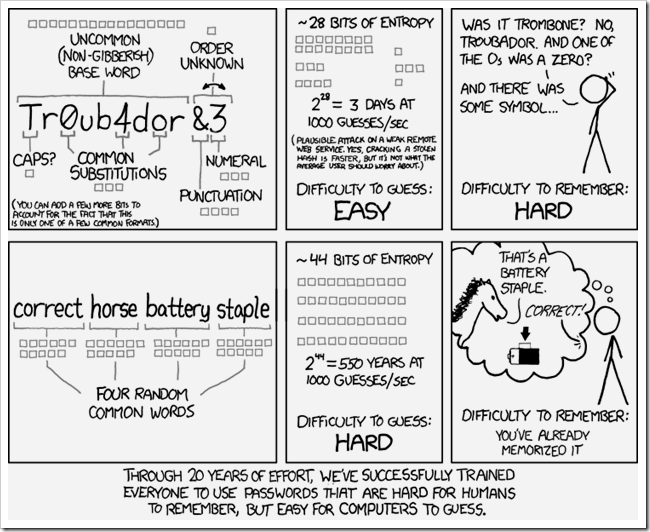
At some point, you should do a search for the most common account passwords (link contains NSFW language), or read the amazing security article “How I’d Hack Your Weak Passwords” by John Pozadzides. If you look at cracking passwords from the hacker perspective, the unwashed masses are basically a sea of vulnerability and ignorance, ripe for the thievery of information. Weak passwords account for the majority of problems ordinary computer users encounter, simply because hackers are going to look for the weakness and attack there—no sense wasting time cracking secure passwords when there are so many that use insecure passwords.
Although there is considerable debate on best practices for passwords, pass phrases, etc, there are some general principals on how to keep yourself safe with secure passwords. Hackers use “brute force” programs to crack passwords. These programs simply try one potential password after another until they get the correct one—although there is a catch that makes them more likely to succeed. These programs try common passwords first, and also use dictionary words or names, which are much more common to be included in passwords than random strings of characters. And once any one password is cracked, the first thing hackers do is check and see if you used the same password on any other services.
If you want to stay safe, the current best practice is to use secure passwords, create unique passwords for all your accounts, and use a password safe like KeePass or LastPass. Both are encrypted, password protected safes for complex passwords, and will generate random strings of alphanumeric text nearly impossible to crack by brute force methods.
What’s the bottom line here? Don’t use passwords like “password1234” or “letmein” or “screen” or “monkey.” Your passwords should look more like “stUWajex62ev” in order to keep hackers out of your accounts. Generate your own secure passwords using this website, or by downloading LastPass or KeePass.
- Download LastPass
- Download KeePass
- List of most common (weak) passwords (NSFW language)
Should I Be Afraid of Hackers In the News?
There’s been a lot of hullabaloo about hackers in the news this past year, and by and large, these groups are not interested in you or yours. While their accomplishments might seem sort of scary, many of the high profile hacking cases of 2011 were done to damage the reputation of large companies that the hackers were irritated with. These hackers make a lot of noise, and have done damage to companies and governments careless enough not to properly protect themselves—and it’s just because they’re so high-profile that you have little to fear from them. The quiet, clever criminal hackers are always the ones to keep an eye out for—while the world might closely watch LulzSec or Anonymous, lots of cybercriminals quietly make off with armloads of cash.
What is Phishing?
One of the most potent tools available to these worldwide cybercriminals, “Phishing” is a kind of social engineering, and can be thought of as a kind of con or grift. It doesn’t take elaborate software, viruses, or hacking to get information if users can easily be tricked in to giving it away. Many use a tool readily available to nearly everyone with an internet connection—email. It’s surprisingly easy to get a few hundred email accounts and trick people into giving away money or information.
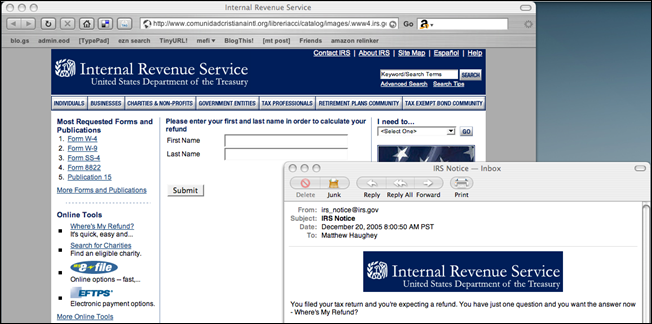
Phishers usually pretend to be someone they’re not, and often prey on older people. Many pretend they’re a bank or website like Facebook or PayPal, and ask for you to input passwords or other info to solve a potential problem. Others may pretend to be people you know (sometimes through hijacked email addresses) or try and prey on your family using information about you publicly viewable on social networks, like LinkedIn, Facebook, or Google+.
There’s no software cure for phishing. You simply have to stay sharp, and carefully read emails before clicking links or giving out information. Here’s a few brief tips to keep yourself safe from phishers.
- Don’t open emails from suspicious addresses or people you don’t know. Email isn’t really a safe place to meet new people!
- You may have friends that have email addresses that are compromised, and you may get phishing emails from them. If they send you anything weird, or aren’t acting like themselves, you may want to ask them (in person) if they’ve been hacked.
- Don’t click links in emails if you’re suspicious. Ever.
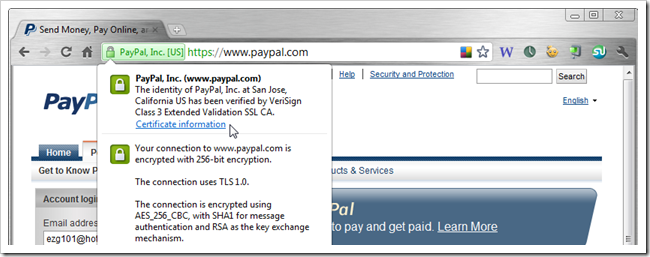
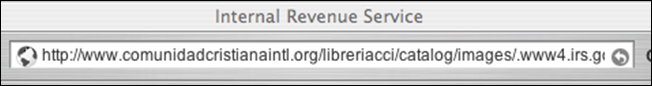
- If you end up on a website, you can generally tell who it is by checking the certificate or looking at the URL. (Paypal, above, is genuine. The IRS, at the lead of this section, is fraudulent.)
- Look at this URL. It seems unlikely that the IRS would be parking a website on an URL like this.
- An authentic website may provide a security certificate, like PayPal.com does. The IRS does not, but US government websites almost always have a .GOV top level domain instead of .COM or .ORG. It's very unlikely that phishers will be able to buy a .GOV domain.
- If you think your bank or other secure service may need information from you, or you need to update your account, do not click the links in your emails. Instead, type in the URL and visit the site in question normally. This guarantees you wont be redirected to a dangerous, fraudulent website, and you can check to see if you have the same notice when you log in.
- Never, ever give out personal information like credit card or debit card numbers, email addresses, phone numbers, names, addresses or social security numbers unless you’re absolutely sure you trust that person enough to share that information.
This is, of course, only the beginning. We’ll cover much more Online Safety, security, and tips to stay safe, in this series in the future. Leave us your thoughts in the comments, or talk about your experience in dealing with hackers or phishers, hijacked accounts, or stolen identities.
Image Credits: Broken Locks by Bc. Jan Kaláb, available under Creative Commons. Scary Norma by Norma Desmond, available under Creative Commons. Untitled by DavidR, available under Creative Commons. Phishing the IRS by Matt Haughey, available under Creative Commons. A Password Key? by Dev.Arka, available under Creative Commons. RMS at pitt by Victor Powell, available under Creative Commons. XKCD strip used without persmission, assumed fair use. Sopranos image copyright HBO, assumed fair use. “Hackers” image copyright United Artists, assumed fair use.