Quick Links
Almost every video conferencing program available has some sort of vulnerability, and Zoom is undoubtedly no exception. However, Zoom users can do a few things to make their next conference call a bit more secure.
Take Proactive Measures
None of us are entirely immune to cybercrime---even to petty offenses like Zoombombing. But being aware of security risks and taking proactive measures to protect yourself can significantly lower your chances of becoming a victim.
While Zoom has recently taken action to make its software more secure by adding new security features and enabling some settings by default, it's still up to you to ensure these features are enabled and that your video conference is as secure as it can possibly be.
All of the following options can be enabled or disabled in your Zoom account's Settings page.
Require a Password to Join the Meeting
Requiring a password to join your conference call is your first layer of defense. Without it, nearly anyone can join---and we mean nearly anyone. If your meeting does get indexed, having it password protected will stop uninvited people from jumping in.
It's also worth mentioning that Zoom provides a feature for embedding a password in the invitation link. We don't recommend this, as anyone with the link can join. If it ends up in the wrong hands, then you may have an unexpected guest appear.
Here are the password settings Zoom offers:
- Require a password when scheduling new meetings
- Require a password for instant meetings
- Require a password for Personal Meeting ID (PMI)
- Embed passwords in meeting link for one-click join (not recommended)
- Require password for participants joining by phone
To access these settings, go to your profile settings page in your web browser and make the changes to your account.
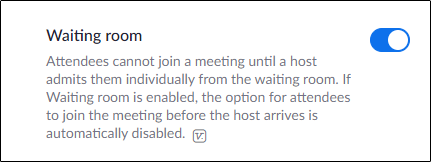
Enable a Waiting Room
Zoom's waiting room is your second layer of defense. If someone happens to get their hands on your conference link, and that conference isn't password-protected, they'll still be placed in a virtual waiting room and need permission to enter.
You can also find the "Waiting Room" setting on your profile settings page.
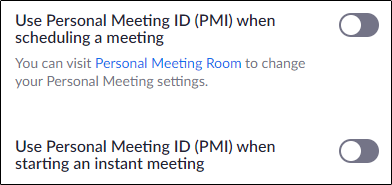
Don't Use Your PMI for Public Meetings
Your Personal Meeting ID is the meeting that is launched by default. This meeting is, in theory, perpetually running. That means if someone gets your PMI, they can join your session whenever they want. You should only use your PMI for private meetings and refrain from sending it out to the public. The fewer people that have it, the better.
Ensure that the settings that use your PMI as the default when scheduling a meeting or starting one instantly are disabled from your settings page.
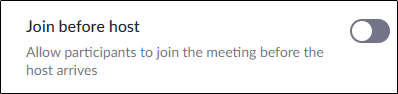
Rule with an Iron Fist
Don't let anyone start the meeting before you, the host, arrives. Period. This keeps uninvited people from having the jump on you. But do keep in mind that if you disable the "Join Before Host" setting, it's always best practice to be prompt. Keep uninvited people out, but don't leave important clients or colleagues waiting.
Know Who's Joining
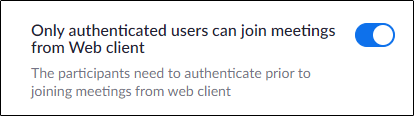
Zoom has a setting you can enable that prevents unauthenticated users from joining a meeting via the web client. This means that users will need to register their name and email to be able to participate, allowing you to know precisely who joins the meeting.
Lock Your Meeting
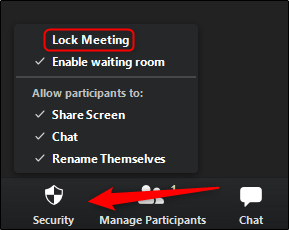
If all expected attendees have made it to the meeting room, go ahead and lock the meeting so nobody else can enter. During the meeting, you'll see a "Security" button at the bottom of the screen. Select the button and then click the "Lock Room" option from the pop-up menu.
Kick Someone From Your Meeting
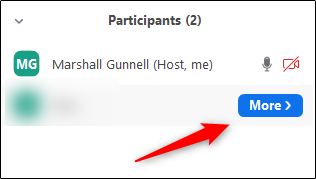
If someone happens to make it to your conference room, you can remove them by hovering over their name in the right-hand pane and then selecting the "More" button.
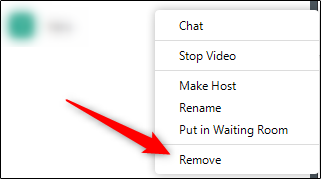
From the menu that appears, select the "Remove" option.
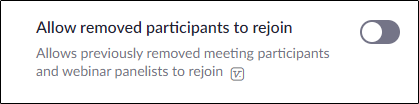
Next, you should disable the setting from your profile Settings page that allows removed participants to rejoin. Once you get rid of the intruder once, you get rid of them for good.
Disable Communication Features
One of the beautiful things about Zoom is that it provides several options for participants to communicate with each other. However, if an uninvited person joins your conference call, they may use these features to harass the participants. If you, the host, will be the only member required to communicate, disable these features:
- Private Chat
- Screen Sharing
- Attendee Speaking (mute everyone's mic)
- Annotations
- File Sharing
- Virtual Backgrounds
All of these features can, again, be found in your profile settings using the web browser.
A determined cybercriminal is hard to deter, but don't just sit idly by while people take advantage of you. Good cybersecurity starts with you—always be prepared.