Quick Links
You've probably heard that public Wi-Fi is dangerous. Advice about avoiding it is almost as widespread as public Wi-Fi itself. Some of this advice is outdated, and public Wi-Fi is safer than it used to be. But there are still risks.
Is Public Wi-Fi Safe or Not?
This is a complicated topic. It's true that browsing on public Wi-Fi is much safer and more private than it used to be thanks to the widespread embrace of HTTPS on the web. Other people on the public Wi-Fi network can't just snoop on everything you're doing. Man-in-the-middle attacks aren't as trivially easy as they used to be.
The EFF recently came down on the side of public Wi-Fi being safe, writing that "There are plenty of things in life to worry about. You can cross 'public Wi-Fi' off your list."
That sounds like sensible advice. And it'd be great if public Wi-Fi was completely safe! We've certainly used public Wi-Fi ourselves at places like McDonald's, and we don't worry about it as much as we used to.
But, if you're asking us whether Wi-Fi is entirely safe, we can't say that. David Lindner at Contrast Security wrote a counterpoint to the EFF's argument, pointing out the risks of malicious hotspots. The community over at Hacker News had quite a few thoughts about the dangers of public Wi-Fi, too. We've tried to explain the risks below.
Here's the bottom line: Random people aren't going to snoop on your activities on public Wi-Fi anymore. But it would be possible for a malicious hotspot to do a bunch of bad things. Using a VPN on a public Wi-Fi network or avoiding public Wi-Fi in favor of your cellular data network is safer.
Why Public Wi-Fi Is Safer Than Ever
Widespread HTTPS encryption on the web has fixed the main security problem with public Wi-Fi. Before HTTPS was widespread, most websites used unencrypted HTTP. When you accessed a standard website over HTTP on public Wi-Fi, other people on the network could snoop on your traffic, viewing the exact web page you were viewing and monitoring any messages and other data you sent.
Worse yet, the public Wi-Fi hotspot itself could perform a "man in the middle" attack, modifying the web pages sent to you. The hotspot could change any web page or other content accessed over HTTP. If you downloaded software over HTTP, a malicious public Wi-Fi hotspot could give you malware instead.
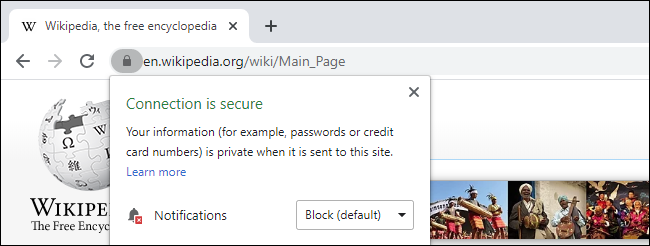
Now, HTTPS has become widespread, and web browsers are branding traditional HTTP sites "not secure." If you connect to a public Wi-Fi network and access websites over HTTPS, other people on the public Wi-Fi network can see the domain name of the site you're connected to (for example, howtogeek.com), but that's it. They can't see the specific web page you're viewing, and they certainly can't tamper with anything on the HTTPS site in transit.
The amount of data people can snoop on has gone way down, and it'd be harder for even a malicious Wi-Fi network to tamper with your traffic.
Some Snooping Is Still Possible
While public Wi-Fi is now much more private, it's still not completely private. For example, if you're browsing the web, you might end up on an HTTP site eventually. A malicious hotspot could have tampered with that web page as it was sent to you, and other people on the public Wi-Fi network would be able to monitor your communications with that site---which web page you're looking at on it, the exact content of the web page you're looking at, and any messages or other data you upload.
Even when using HTTPS, there's still a bit of snooping potential. Encrypted DNS isn't yet widespread, so other devices on the network can see your device's DNS requests. When you connect to a website, your device contacts its configured DNS server over the network and finds the IP address connected to a website. In other words, if you're connected to a public Wi-Fi network and browsing the web, someone else nearby could monitor which websites you visit.
However, snooper wouldn't be able to see the specific web pages you were loading on that HTTPS site. For example, they'd know that you were connected to howtogeek.com but not which article you were reading. They would also be able to see some other information, such as the amount of data being transferred back and forth---but not the contents of the data.
There Are Still Security Risks on Public Wi-Fi
There are other potential security risks involved with public Wi-Fi, too.
A malicious Wi-Fi hotspot could redirect you to malicious websites. If you connect to a malicious Wi-Fi hotspot and try to connect to bankofamerica.com, it could forward you to the address of a phishing site impersonating your real bank. The hotspot could execute a "man in the middle attack," loading the real bankofamerica.com and presenting you a copy of it over HTTP. When you sign in, you'd be sending your login details to the malicious hotspot, which could capture them.
That phishing site wouldn't be an HTTPS site, but would you really notice the HTTP in your browser's address bar? Techniques like HTTP Strict Transport Security (HSTS) allow websites to tell web browsers that they should only connect over HTTPS and never use HTTP, but not every website takes advantage of that.
Apps, in general, could also be a problem---do all the apps on your smartphone correctly validate certificates? Is every application on your computer configured to transfer data over HTTPS in the background, or are there some applications automatically using HTTP instead? In theory, applications should be correctly validating certificates and avoiding HTTP in favor of HTTPS. In practice, it'd be tough to confirm every app is behaving correctly.
Other devices on the network could also be a problem. For example, if you're using a computer or other device with unpatched security holes, your device could be attacked by other devices on the network. That's why Windows PCs come with a firewall enabled by default and why that firewall is more restrictive when you tell Windows you're connected to public Wi-Fi instead of a private Wi-Fi network. If you tell the computer you're connected to a private network, your network shared folders may be made available to other computers on the public Wi-Fi.
How to Protect Yourself Anyway
While public Wi-Fi is safer and more private than it used to be, the security picture is still messier than we'd like.
For maximum protection on public Wi-Fi networks, we still recommend a VPN. When you use a VPN, you connect to a single VPN server, and all of your system's traffic is routed through an encrypted tunnel to the server. The public Wi-Fi network you're connecting to sees a single connection---your VPN connection. No one can even see which websites you're connecting to.
That's a big reason why businesses use VPNs (virtual private networks.) If your organization makes one available to you, you should seriously consider connecting to it when you're on public Wi-Fi networks. However, you can pay for a VPN service and route your traffic through there when you use networks you don't completely trust.
You could also skip public Wi-Fi networks entirely. For example, if you have a cellular data plan with wireless hotspot (tethering) capabilities and a solid cellular connection, you could connect your laptop to your phone's hotspot in public and avoid the potential problems involved in public Wi-Fi.