Quick Links
Your iPhone isn't as susceptible to viruses as a PC or Mac, but iOS malware does exist. Here's what protects your iPhone from viruses, and how you can avoid other types of malware and threats on your iPhone or iPad.
What Protects iPhones and iPads From Viruses?
The iPhone and iPad are protected from viruses by design. This is because you simply cannot install software from just anywhere on your iPhone (unless you jailbreak it). There are a few ways you can install software on your iPhone, but most people only ever encounter one of them: The App Store.
The App Store is Apple's curated storefront. Developers must submit their apps to be tested, checked for potential malware, and effectively given a clean bill of health from Apple before they're made available. Therefore, you should be able to trust any app that's available in the App Store on your device.
Developers and businesses have ways you can bypass the App Store and install their custom apps, but most people with iPhones and iPads get their software from the App Store.
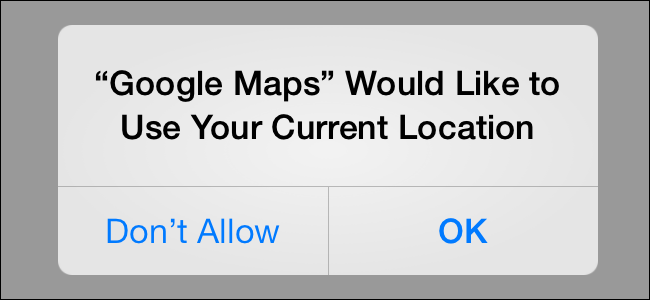
On iOS, all apps are "sandboxed" by design. This term means the apps are only given access to the resources they require for normal operation. This prevents apps from changing settings, accessing parts of the file system that contain sensitive data, and other devious behavior.
A robust permissions system also provides granular control over exactly which services and information your apps can access. Apps have to ask before they can access your location, contacts, files, photos, camera, or other resources.
Restricted multitasking is another way iOS hinders potentially harmful applications from wreaking havoc. Most apps don't run in the background on iOS, but when one is, you see a bar (usually red or blue) at the top of the screen. This means any running apps can't fly under the radar on iOS. Unless they're the currently active app, they can do very little in the background.
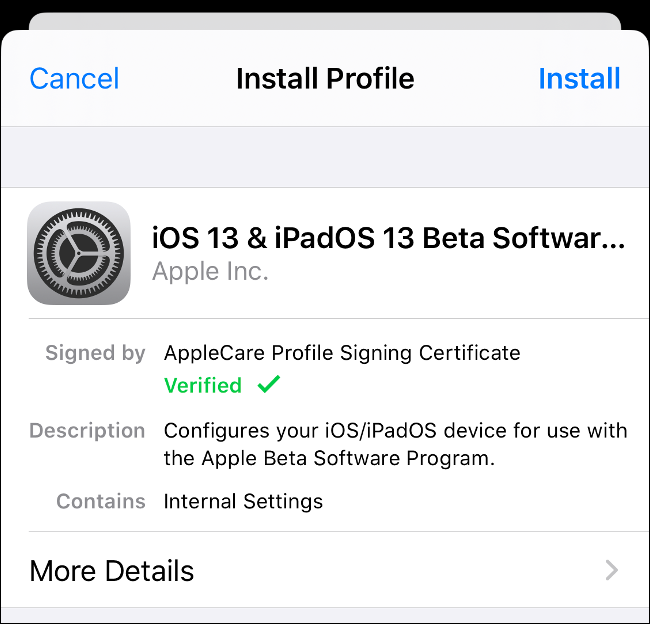
Curious about the other ways you can install software on an iPhone? People who need custom apps (like the point-of-sale software used at every Apple Store) can install pre-signed versions. These require a valid developer license, provided the correct configuration profile is installed on your iPhone.
If you know how to do it, you can also compile your own apps and push them to your device with Xcode for testing. Apps you install this way expire because this feature is intended for developers who are testing apps.
What About Malware on the App Store?
In October 2019, Apple removed 18 apps from the App Store because they were driving up advertising revenue by clicking adverts in the background. This wasn't the first time apps were removed from the App Store due to malware.
While Trojans and worms relate to specific types of malware, the term "malware" is also a catch-all term for rogue apps. In the case of the rogue advertisement clicker, the app in question would have likely reduced your battery life and possibly consumed more mobile data than you would've liked.
Apart from that, the apps were fairly benign. This is a good example of why iOS is regarded as the most secure smartphone platform. Apple can also delete any apps from your device remotely that it detects as malware. This might seem overbearing, but the intention is good.
Do You Need an iPhone Antivirus?
You don't need an antivirus app for your iPhone, iPad, or iPod Touch. Despite many attempts to market security suites for the iPhone, it would be largely pointless. This is because Apple simply doesn't allow Windows-like viruses to run rampant on its platform.
Antivirus software has to scan your device to function and app sandboxing prevents this. An antivirus app cannot check running processes, scan system files, or look at other app data. Apps are only given access to their own files and any services or data you have granted permission, like GPS data or camera access.
In short, the permissions necessary for an antivirus to function would render iOS more vulnerable to attack. Android phones and devices also use app sandboxing, but that platform gives apps much more freedom to interact with each other and different parts of the operating system.
If you own an Android phone, you should definitely consider installing a good antivirus.
Safari Might Be iPhone's Weakest Point
In August 2019, researchers from Google's Project Zero revealed iPhone malware was spreading via a handful of compromised websites. In total, 14 vulnerabilities were discovered, with seven of them affecting Safari. Two of them allowed malware to escape the app sandbox and get unhindered access to iOS.
These websites were able to install spyware on affected devices and look for passwords and authentication tokens stored in the iCloud Keychain. Messages from services like iMessage, Skype, and WhatsApp, as well as email in Gmail, Outlook, and Yahoo, were also targeted. Other user information like call history, current GPS location, photos, notes, and voice memos were also of interest to the malware.
This spyware reported information back to the server once per minute. The information was transmitted unencrypted, in plain text format. The exploit affected users from iOS 10 to 12. Apple resolved these exploits with the iOS 12.1.4 patch in early February 2018. It's unknown how many devices were affected.
This was a good old fashioned zero-day exploit. Cybercriminals relied on unchecked security vulnerabilities in iOS to prey on their victims. Apple issued a patch and the vulnerabilities have been closed, but not before potentially thousands of devices were affected. To remove the spyware, you just had to update your device.
Although this was the first exploit of its kind in the wild, this discovery changed what many thought they knew about iPhone security. It's further proof that no device is completely immune from potentially damaging zero-day exploits---even the iPhone.
Beware of Rogue Configuration Profiles
Configuration profiles install a ".mobileconfig" file that allows you to configure a device quickly. Normally, these contain network settings, like wireless access point credentials, proxy settings, and email server login information. IT departments use them to rapidly deploy up-to-date settings to new employees or an entire staff.
These files can be distributed both via email and the web, which means they present a major opportunity for misuse. If you install a profile from someone you don't trust, an attacker could route your web traffic to a rogue VPN or proxy. He could then conduct a man-in-the-middle attack and attempt to snoop through your browsing data, including passwords and usernames.
Configuration profiles can also install certificates like those enterprise users need to enable bespoke app installs---for example, software that doesn't appear on the App Store. A more sinister use for a certificate might be to dupe a target into thinking he's using a trustworthy website (like a financial institution) when he's not.
If you're browsing the web or reading an email and a popup informs you a profile is being installed, reject it unless you specifically requested it.
To manage your installed profiles, head to Settings > General > Profile. If you don't see the "Profile" option, you don't have any installed.
iPhone Malware Exists, But You Can Avoid It
There are a few things you can do to stay safe while you use your iPhone. The first is to always install updates as soon as they're available. The only exception here is for major iOS upgrades (for example, going from iOS 12 to iOS 13). Understandably, you might want to hold off for a week or so on those to see if any stability or performance issues are reported. You can also turn on automatic updates.
The second thing you can do is avoid clicking links from strangers, particularly those on sketchy websites or hidden behind shortened URLs. In general, you shouldn't be afraid to open links on iOS, but rogue actors might target your device if an unpatched exploit appears. This is good advice regardless of the device you use.
"Jailbreaking" is the practice of removing protections on Apple devices, so you can install apps from anywhere. Root access allows you (or third-party software) to modify how the operating system works. You should avoid jailbreaking your device if you want to maintain a high level of security.
Common sense also keeps you safe. If an app doesn't look trustworthy, don't trust it. Many scam apps attempt to trick people into making in-app purchases. Others have been caught prompting people for their Apple ID and login credentials. Never authorize any purchases from sketchy apps and only type your login credentials in the Settings app.
Regardless the device you use, you should always be wary of phishing attacks on the web and in email. For these scams, actors pose as a legitimate service to steal your login info and other personal credentials.
Also, watch out for social engineering techniques scammers use over the phone. It's unlikely your bank will ever call and ask you to confirm information like your date of birth or account number. If they do, ask them for a number you can use to call them back. You can then search that number and make sure it's legit.
iOS Is Still Secure
Despite Safari's vulnerabilities, rogue advertisement clicker apps, and the lack of a functional antivirus for iOS, the platform is still well-regarded from a security standpoint. Apple baked security into iOS at its inception and has gradually improved its permissions system over the years, further demonstrating the company's mission to create a secure, private platform.
No platform is immune from vulnerabilities, but that doesn't mean you should avoid using that platform altogether. Windows and Android are the two most popular operating systems in the world, and, as a result, they experience more security issues than any other. We don't recommend you avoid those platforms; just exercise a sensible level of caution when appropriate.
In the meantime, save your money---you don't need to shell out for an iOS antivirus. You've already got everything you need to stay secure.