Quick Links
We use our phones for event tickets, reservations, insurance cards, and even driver's licenses. But what happens when someone takes your unlocked iPhone out of view for a moment---what's the risk? What's the worst thing someone can do?
This is also relevant at international borders, where your unlocked phone might be taken from you---hopefully temporarily.
Financial Details and Passwords Are Secure
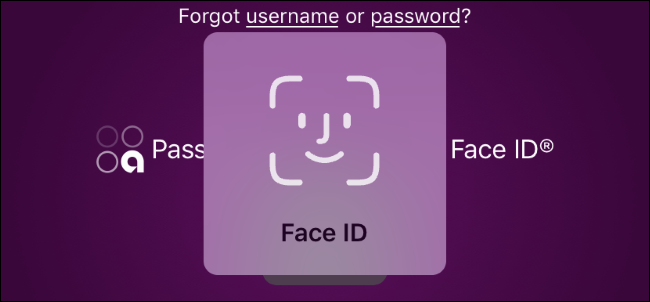
Letting your iPhone out of your sight for a moment isn't as risky as it seems. If you have an online banking or another financial app on your iPhone, the person with your phone probably can't open it. Most of these apps use Face ID, Touch ID, or even a PIN to authenticate you. Someone with access to your unlocked phone can't unlock your banking app---not without pointing it at your face to authenticate with Face ID, at least.
Many other sensitive apps are secured with additional protection like this, too. Someone with your phone can't buy apps on the App Store in password manager apps like LastPass and 1Password.
Your Email, SMS, and Photos Could Be Snooped On
If your phone is out of your view, it's trivial for someone with it to look at your notifications, photos, SMS messages, and anything else you can tap. Anything you can access with your phone unlocked is accessible to them---and that's a lot.
They could even open Messages, Mail, or Facebook and send messages as you. Someone who has it out for you could post an offensive message on social media or email your boss an insulting email. They could access your web browser, look at your browsing history, and use any website you're logged into. All bets are off here.
In fact, someone with access to your phone could even email or send themselves some of your photos or other messages.
In theory, someone with access to your phone could use SMS message verification to gain access to one of your accounts, too. They could reset the password on your account, use email or SMS to get a code, and then try to provide a new password.
They Can't Install Software
Someone with your unlocked iPhone can't install software, even if your iPhone is unlocked. You need to authenticate with Face ID or Touch ID to install a new app.
Configuration profiles, which are intended for organizations and allow someone to force settings like a VPN on the iPhone, also can't be installed without a PIN.
So How Dangerous Is It?
Someone with access to your phone can't install software, open banking apps to perform financial transactions or snoop on the saved passwords in your password manager. That's a relief.
That matters---unlike with a PC, someone can't install software that lays in the background and spies on you.
However, the person can look through your data at that moment, checking your photos, reading your messages, and digging through your emails. They can do whatever they want with your web browser and most apps on your system. That's not great.
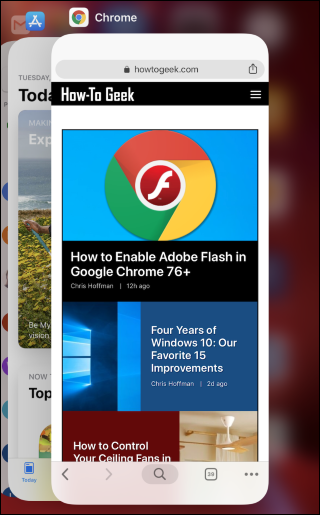
If you're concerned whether someone was messing with your phone, you might want to open the app switcher right after getting your phone back. Just swipe up from the bottom of the screen (on an iPhone X or newer) or double-click the Home button (on an iPhone 8 or older.) You'll see the most recently used apps---unless the person closed the apps after using them, which is unlikely.
How to Lock Someone to a Single App
While leaving your unlocked iPhone with someone else isn't as dangerous as it could be, it's still not a great idea to give someone---whether it's a ticket-taker at an event or a child in your home---access to your entire unlocked phone.
You can make things safer by using "Guided Access," which lets you quickly lock your iPhone to a single app. Set this feature up ahead of time, and you can then quickly put an iPhone into "Guided Access" mode. This restricts it to a single app until you enter your PIN.