Quick Links
Who, when, and from where? Good security practices say you should know who's been accessing your Linux computer. We show you how.
The wtmp File
Linux and other Unix-like operating systems such as MacOS are very good at logging. Somewhere in the bowels of the system, there is a log for just about everything you can think of. The log file we're interested in is called wtmp. The "w" might stand for "when" or "who"---no one seems to agree. The "tmp" part probably stands for "temporary," but it might also stand for "timestamp."
What we do know is that wtmp is a log that captures and records every login and logout event. Reviewing the data in the wtmp log is a basic step in taking a security-minded approach to your system admin duties. For a typical family computer, it might not be so critical from a security perspective, but it is interesting to be able to review your combined use of the computer.
Unlike many of the text-based log files in Linux, wtmp is a binary file. To access the data within it, we need to use a tool designed for that task.
That tool is the last command.
The last Command
The last command reads data from the wtmp log and displays it in a terminal window.
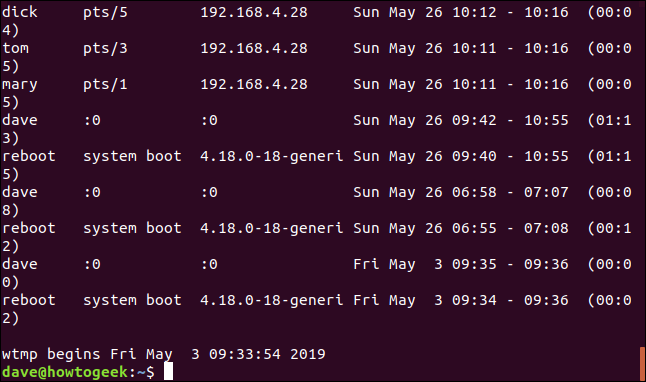
If you type last and press Enter it will display all of the records from the log file.
last
Each record from wtmp is displayed in the terminal window.
From left to right, each line contains:
- The username of the person who logged in.
-
The terminal they were logged into. A terminal entry of
:0means they were logged in on the Linux computer itself. - The IP address of the machine they were logged into.
- The login time and date stamp.
- The duration of the session.
The last line tells us the date and time of the earliest recorded session in the log.
A login entry for the fictitious user 'reboot' is entered into the log each time the computer is booted up. The terminal field is replaced with the kernel version. The duration of the logged in session for these entries represents the up-time for the computer.
Showing a Specific Number of Lines
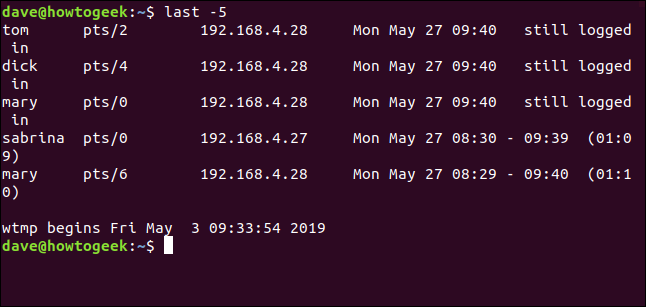
Using the last command on its own produces a dump of the entire log with most of it whizzing past the terminal window. The portion that remains visible is the earliest data in the log. This is probably not what you wanted to see.
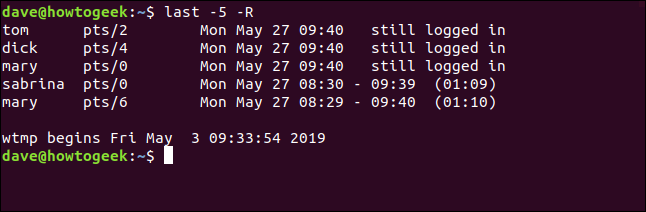
You can tell last to give you a specific number of lines of output. Do this by providing the number of lines you'd like on the command line. Note the hyphen. To see five lines, you need to type -5 and not 5:
last -5
This gives the first five lines from the log, which is the most recent data.
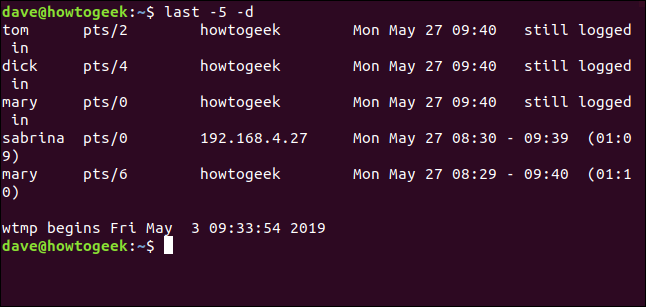
Showing Network Names for Remote Users
The -d (Domain Name System) option tells last to try to resolve remote users' IP addresses into a machine or network name.
last -d
It isn't always possible for last to convert the IP address to a network name, but the command will do so when it can.
Hiding IP Addresses and Network Names
If you're not interested in the IP address or network name, use the -R (no hostname) option to suppress this field.
Because this gives a neater output with no ugly wraparounds, this option has been used in all of the following examples. If you were using last to try to identify unusual or suspicious activity, you would not suppress this field.
Selecting Records by Date
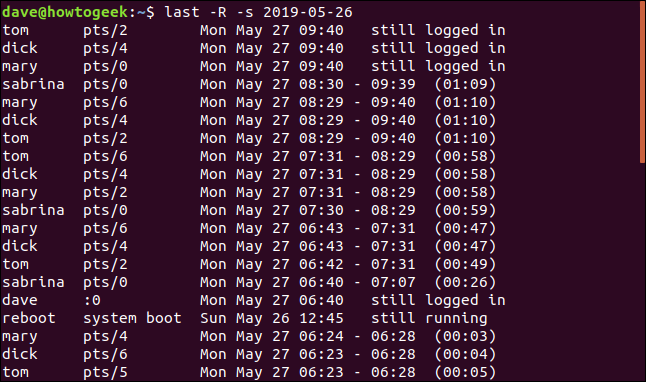
You can use the -s (since) option to restrict the output to only show login events that took place since a specific date.
If you only wanted to see login events that took place from May, 26th 2019, you would use the following command:
last -R -s 2019-05-26
The output shows records with login events that took place from the time 00:00 on the specified day, up to the newest records in the log file.
Searching Until an End Date
You can use the -t (until) to specify an end date. This allows you to select a set of login records that took place between two dates of interest.
This command asks last to retrieve and display the login records from 00:00 (dawn) on the 26th up to the time 00:00 (dawn) on the 27th. This narrows the listing down to login sessions that took place on the 26th only.
Time and Date Formats
You can use times as well as dates with the -s and -t options.
The different time formats that can be used with the last options that use dates and times are (allegedly):
- YYYYMMDDhhmmss
- YYYY-MM-DD hh:mm:ss
- YYYY-MM-DD hh:mm - seconds are set to 00
- YYYY-MM-DD - time is set to 00:00:00
- hh:mm:ss - date is set to today
- hh:mm - date will be set to today, seconds to 00
- now
- yesterday - time is set to 00:00:00
- today - time is set to 00:00:00
- tomorrow - time is set to 00:00:00
- +5min
- -5days
Why 'allegedly'?
The second and third formats in the list did not work during the research for this article. These commands were tested on Ubuntu, Fedora, and Manjaro distributions. These are derivatives of the Debian, RedHat and Arch distributions, respectively. That covers all of the main families of Linux distribution.
last -R -s 2019-05-26 11:00 -t 2019-05-27 13:00
As you can see, the command returned no records at all.
Using the first date and time format from the list with the same date and times as the previous command does return records:
last -R -s 20190526110000 -t 20190527130000
Searching By Relative Units
You also specify time periods that are measured in minutes or days, relative to the current date and time. Here we are asking for records from two days ago up until one day ago.
last -R -s -2days -t -1days
Yesterday, Today and Now
You can use yesterday and tomorrow as shorthand for yesterday's date and today's date.
last -R -s yesterday -t today
Not that this will not include any records for today. That is the expected behavior. The command asks for records from the start date until the end date. It doesn't include records from within the end date.
The now option is shorthand for "today at the current time." To see the login events that have taken place since 00:00 (dawn) until the time when you issue the command use this command:
last -R -s today -t now
This will show all login events right up the present time, including those that are still logged in.
The present Option
The -p (present) option allows you to find out who was logged in at a point in time.
It doesn't matter when they logged in or out, but if they were logged into the computer at the time you specify, they will be included in the listing.
If you specify a time without a date last assumes you mean "today."
last -R -p 09:30
People who are still logged in (obviously) don't have a log out time; they are described as still logged in . If the computer has not been rebooted since the time you specify it will be listed as still running.
If you use the now shorthand with the -p (present) option you can find out who is logged in at the time you issue the command.
last -R -p now
This a somewhat long-winded way to achieve what can be accomplished using the who command.
The lastb Command
The lastb command deserves mention. It reads data from a log called btmp. There is a little more consensus on this log name. The 'b' stands for bad, but the 'tmp' part is still subject to debate.
lastb lists the bad (failed) login attempts. It accepts the same options as last. Because they were failed login attempts, they entries will all have a 00:00 duration.
You must use sudo with lastb.
sudo lastb -R
The Last Word on the Matter
Knowing who has logged into your Linux computer, and when, and from where is useful information. Combining this with the details of failed login attempts arms you with the first steps in investigating suspicious behavior.