Quick Links
Windows 10's October 2018 Update includes a new "Block Suspicious Behaviors" security feature. This protection is off by default, but you can enable it to protect your PC from a variety of threats.
What Does "Block Suspicious Behaviors" Do?
This feature has a pretty vague name. However, Microsoft's documentation clarifies that "Block Suspicious Behaviors" is just a friendly name for the "Windows Defender Exploit Guard attack surface reduction technology." This security feature was introduced in the Fall Creators Update, but was only available in Windows 10 Enterprise. In the October 2018 Update, it's now available to everyone via an option in Windows Security.
When you enable this feature, Windows 10 activates a variety of security rules. These rules disable features normally only used by malware, helping protect your PC from attack.
Here are some of the attack surface reduction rules:
- Block executable content from email client and webmail
- Block Office applications from creating child processes
- Block Office applications from creating executable content
- Block Office applications from injecting code into other processes
- Block JavaScript or VBScript from launching downloaded executable content
- Block execution of potentially obfuscated scripts
- Block Win32 API calls from Office macro
- Block credential stealing from the Windows local security authority subsystem (lsass.exe)
- Block process creations originating from PSExec and WMI commands
- Block untrusted and unsigned processes that run from USB
- Block Office communication applications from creating child processes
These are suspicious actions that might be used by malicious applications. For example, these rules block executable files that arrive by email, prevent Office applications from doing specific things, and stop dangerous macro behaviors. With these rules enabled, Windows protects credentials from theft, stops suspicious looking executables on USB drives from running, and refuses to run scripts that look disguised to get around antivirus software.
You'll find a complete list of the attack surface reduction rules on Microsoft's support site. Organizations can customize which rules are used through group policy, but average consumer PCs get a one-size-fits-all set of rules. It's unclear exactly which rules are used when you enable this option in Windows Security.
This is Part of Windows Defender Exploit Guard
Attack Surface Reduction is part of Windows Defender Exploit Guard, which also includes Exploit Protection, Network Protection, and Controlled Folder Access.
That's important to clarify---"Block Suspicious Behaviors" isn't the same feature as Exploit Protection, which protects your PC against a variety of common exploit techniques. For example, Exploit Protection protects against common memory exploit techniques used by zero-day attacks and terminates any process that uses them. Exploit Protection works like Microsoft's Enhanced Mitigation Experience Toolkit (EMET) software. Attack Surface Reduction disables potentially dangerous features at a higher level.
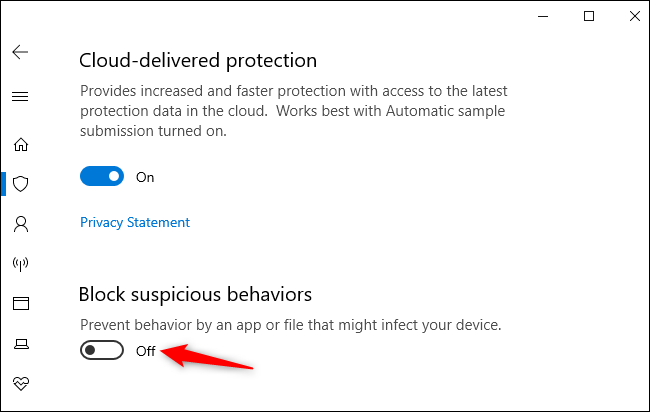
Exploit Protection is enabled by default, and you can tweak it from elsewhere in the Windows Security application. Attack Surface Reduction, or "Block Suspicious Behaviors," isn't enabled by default yet.
How to Enable "Block Suspicious Behaviors"
You can enable this feature from the Windows Security application---formerly named Windows Defender Security Center.
To find it, head to Settings > Update & Security > Windows Security > Open Windows Security or just launch the "Windows Security" shortcut from your Start menu.
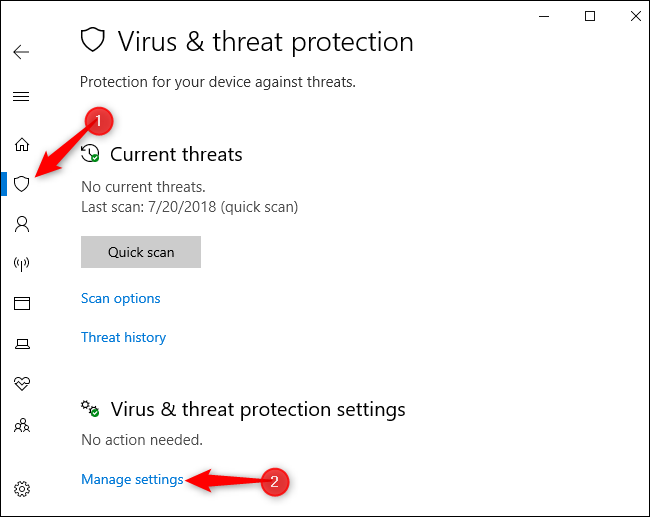
Click the "Virus & Threat Protection" option, and then click the "Manage Settings" link under the "Virus & Threat Protection Settings" section.
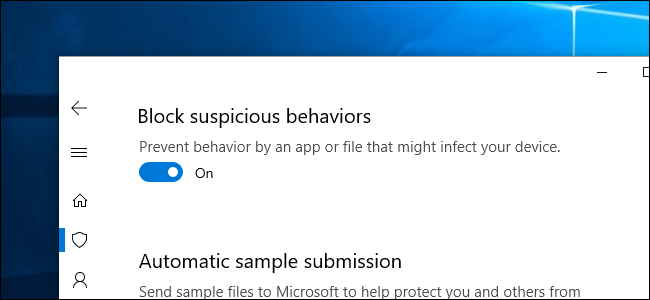
Click the switch under "Block Suspicious Behaviors" to toggle this feature on or off.
If Block Suspicious Behaviors blocks an action you need to regularly perform, you can return here and disable it. However, the blocked behaviors are not common in normal PC usage.