If the desktop version of Skype is on your Windows computer, you're vulnerable to a really nasty exploit. A flaw in Skype's update tool could give attackers full control over your system, and Microsoft says there isn't going to be a fix any time soon.
Happily, you can avoid the problem completely by replacing the "desktop" version of Skype with the one available from the Microsoft Store. Still, it's embarrassing for Microsoft's own software to have a weakness this fundamental, and the exploit in question is one Redmond has warned other developers about multiple times.
Here's what this exploit works, and how you can make sure you're using the safe Windows Store version of Skype.
What's Wrong With Skype?
Updating software is supposed to keep you secure, but ironically in Skype's case, updating is the problem. That's because the flaw here isn't with Skype itself, but rather the tool Skype uses to find and install updates. This update tool is vulnerable to DLL hjjacking, as researcher Stefan Kanthak outlines:
This executable is vulnerable to DLL hijacking: it loads at least UXTheme.dll from its application directory %SystemRoot%Temp instead from Windows' system directory. An unprivileged (local) user who is able to place UXTheme.dll or any of the other DLLs loaded by the vulnerable executable in %SystemRoot%Temp gains escalation of privilege to the SYSTEM account.
Basically, Skype runs DLLs from the Temp folder, which users can access without administrator rights. This makes it trivial for bad actors to switch out the DLLs and gain system level control over your computer. It's the kind of vulnerability Microsoft specifically warns developers to avoid, but Microsoft's Skype team seems to have missed that particular memo.
And it gets worse. Microsoft told Kanthak they "were able to reproduce the issue," but there won't be issuing a patch issued to solve the problem. Instead, Microsoft plans on solving the problem during the next major release of Skype---it's not clear when that will be.
That's...not ideal. Thankfully, there's an alternative.
The Solution: Use the Windows Store Version
Microsoft offers two versions of Skype for Windows: the "Desktop" version, which has been around for ages, and the Universal Windows Platform (UWP) version, which you can download from the Microsoft Store app bundled with Windows. Only the desktop version is vulnerable to this particular exploit, because only the desktop version uses its own update tool.
Microsoft has been pushing users to the Microsoft Store version of Skype for a while: the Skype download page directs users to the Store, for example. But many users still have the desktop version on their systems, and they should uninstall that and only use the Store version if they want to stay safe from this exploit.
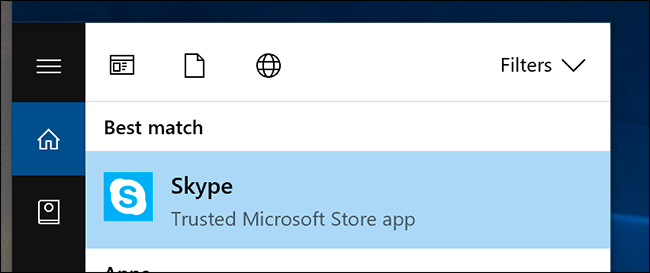
How can you tell which version you have? The simplest way is to search for "Skype" in the start menu. If you see the words "Trusted Microsoft Store app" below Skype's name, you're probably covered.
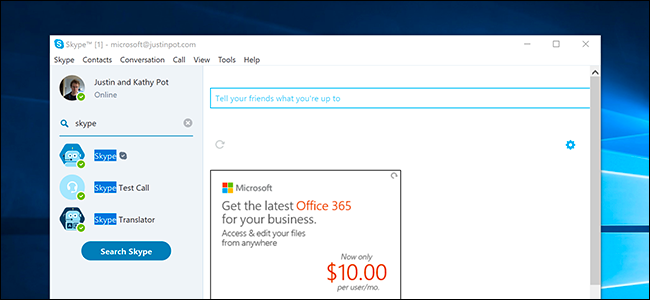
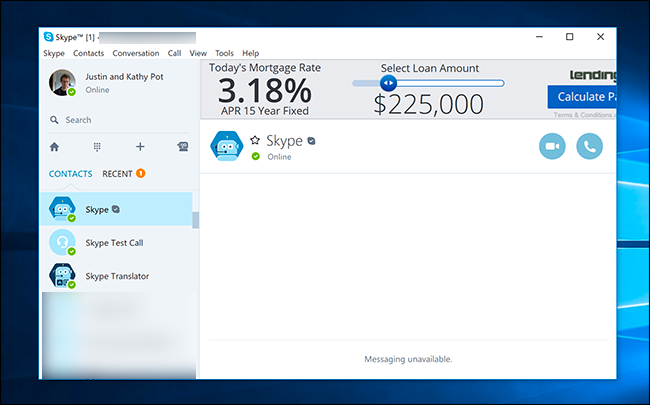
The two apps also look completely different. Here's the "desktop" version:
If your Skype looks like this, you're vulnerable to the exploit. You should uninstall Skype, then download the Microsoft Store version.
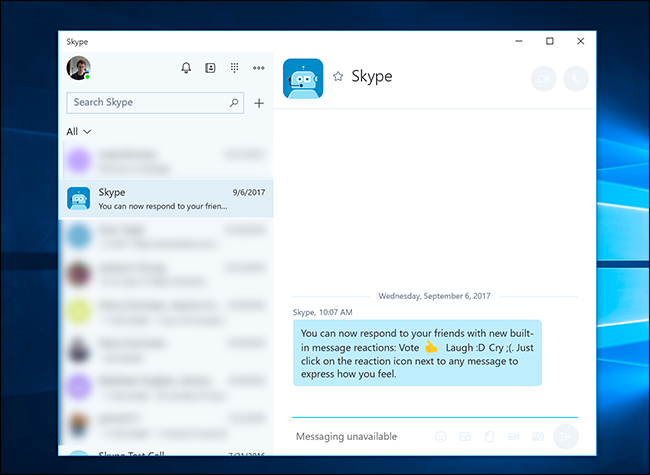
Here's the Microsoft Store version:
If your Skype looks like this, you're safe: updates for this version are handled using Microsoft Store, so the vulnerability is not relevant.
It's unfortunate that Microsoft won't just patch this vulnerability, but at least there's a working version of Skype that's locked down. And while the interface and features of the Microsoft Store version will be an adjustment, things like calling and chat work just fine in our tests, even if the interface offers fewer options. And hey: there's no ugly ads on the Store version, so that's a plus.