Quick Links
The Intel Management Engine has been included on Intel chipsets since 2008. It's basically a tiny computer-within-a-computer, with full access to your PC's memory, display, network, and input devices. It runs code written by Intel, and Intel hasn't shared a lot of information about its inner workings.
This software, also called Intel ME, has popped up in the news because of security holes Intel announced on November 20, 2017. You should patch your system if it's vulnerable. This software's deep system access and presence on every modern system with an Intel processor means it's a juicy target for attackers.
What Is Intel ME?
So what is the Intel Management Engine, anyway? Intel provides some general information, but they avoid explaining most of the specific tasks the Intel Management Engine performs and precisely how it works.
As Intel puts it, the Management Engine is "a small, low-power computer subsystem". It "performs various tasks while the system is in sleep, during the boot process, and when your system is running".
In other words, this is a parallel operating system running on an isolated chip, but with access to your PC's hardware. It runs when your computer is asleep, while it's booting up, and while your operating system is running. It has full access to your system hardware, including your system memory, the contents of your display, keyboard input, and even the network.
We now know that the Intel Management Engine runs a MINIX operating system. Beyond that, the precise software that runs inside the Intel Management Engine is unknown. It's a little black box, and only Intel knows exactly what's inside.
What Is Intel Active Management Technology (AMT)?
Aside from various low-level functions, the Intel Management Engine includes Intel Active Management Technology. AMT is a remote management solution for servers, desktops, laptops, and tablets with Intel processors. It's intended for large organizations, not home users. It's not enabled by default, so it isn't really a "backdoor", as some people have called it.
AMT can be used to remotely power on, configure, control, or wipe computers with Intel processors. Unlike typical management solutions, this works even if the computer isn't running an operating system. Intel AMT runs as part of the Intel Management Engine, so organizations can remotely manage systems without a working Windows operating system.
In May 2017, Intel announced a remote exploit in AMT that would allow attackers to access AMT on a computer without providing the necessary password. However, this would only affect people that went out of their way to enable Intel AMT---which, again, isn't most home users. Only organizations who used AMT needed to worry about this problem and update their computers' firmware.
This feature is just for PCs. While modern Macs with Intel CPUs do also have the Intel ME, they do not include Intel AMT.
Can You Disable It?
You can't disable the Intel ME. Even if you disable Intel AMT features in your system's BIOS, the Intel ME coprocessor and software is still active and running. At this point, it's included on all systems with Intel CPUs and Intel provides no way to disable it.
While Intel provides no way to disable the Intel ME, other people have experimented with disabling it. It isn't as simple as flicking a switch, though. Enterprising hackers have managed to disable the Intel ME with quite some effort, and Purism now offers laptops (based on older Intel hardware) with the Intel Management Engine disabled by default. Intel likely isn't happy about these efforts, and will make it even more difficult to disable the Intel ME in the future.
But, for the average user, disabling the Intel ME is basically impossible---and that's by design.
Why the Secrecy?
Intel doesn't want its competitors to know the exact workings of the Management Engine software. Intel also seems to be embracing "security by obscurity" here, attempting to make it more difficult for attackers to learn about and find holes in the Intel ME software. However, as the recent security holes have shown, security by obscurity is no guaranteed solution.
This isn't any sort of spying or monitoring software---unless an organization has enabled AMT and is using it to monitor their own PCs. If Intel's Management Engine was contacting the network in other situations, we'd likely have heard of it thanks to tools like Wireshark, which allow people to monitor traffic on a network.
However, the presence of software like Intel ME that can't be disabled and is closed source is certainly a security concern. It's another avenue for attack, and we've already seen security holes in Intel ME.
Is Your Computer's Intel ME Vulnerable?
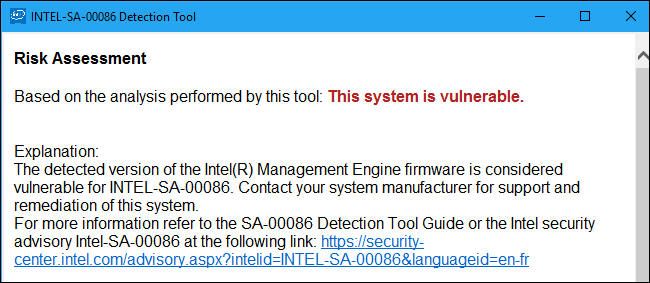
On November 20, 2017, Intel announced serious security holes in Intel ME that had been discovered by third-party security researchers. These include both flaws that would allow an attacker with local access to run code with full system access, and remote attacks that would allow attackers with remote access to run code with full system access. It's unclear just how hard they would be to exploit.
Intel offers a detection tool you can download and run to find out if your computer's Intel ME is vulnerable, or whether it's been fixed.
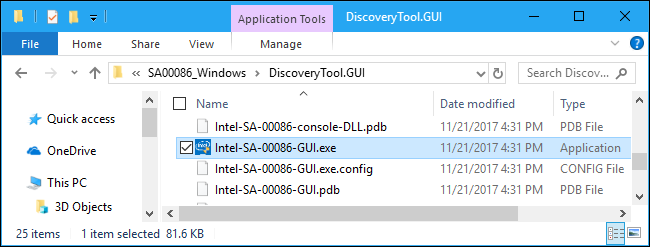
To use the tool, download the ZIP file for Windows, open it, and double-click the "DiscoveryTool.GUI" folder. Double-click the "Intel-SA-00086-GUI.exe" file to run it. Agree to the UAC prompt and you'll be told whether your PC is vulnerable or not.
If your PC is vulnerable, you can only update the Intel ME by updating your computer's UEFI firmware. Your computer's manufacturer has to provide you with this update, so check the Support section of your manufacturer's website to see if there are any UEFI or BIOS updates available.
Intel also provides a support page with links to information about updates provided by different PC manufacturers, and they're keeping it updated as manufacturers release support information.
AMD systems have something similar named AMD TrustZone, which runs on a dedicated ARM processor.
Image Credit: Laura Houser.