Quick Links
Windows 10's integrated Windows Defender antivirus has some "cloud" features, like other modern antivirus applications. By default, Windows automatically uploads some suspicious-looking files and reports data about suspicious activity so new threats can be detected and blocked as quickly as possible.
These features are part of Windows Defender, the antivirus tool included with Windows 10. Windows Defender is always running unless you've installed a third-party antivirus application tool to replace it.
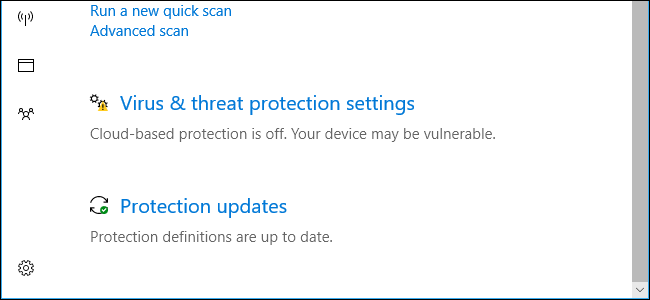
These two features are enabled by default. You can view whether they're currently enabled by launching the Windows Defender Security Center. You can find it by searching for "Windows Defender" in your Start menu, or by locating "Windows Defender Security Center" in the list of apps. Navigate to Virus & threat protection > Virus & threat protection settings.
Both Cloud-based protection and Automatic sample submission can be disabled here, if you like. However, we recommend you leave these features enabled. Here's what they do.
Cloud-Based Protection
The Cloud-based protection feature "provides increased and faster protection with access to the latest Windows Defender Antivirus protection data in the cloud", according to the Windows Defender Security Center interface.
This appears to be a new name for the latest version of the Microsoft Active Protection Service, also known as MAPS. It was formerly known as Microsoft SpyNet.
Think of this as a more advanced heuristics feature. With typical antivirus heuristics, an antivirus application watches that programs do on your system and decides whether their actions look suspicious. It makes this decision entirely on your PC.
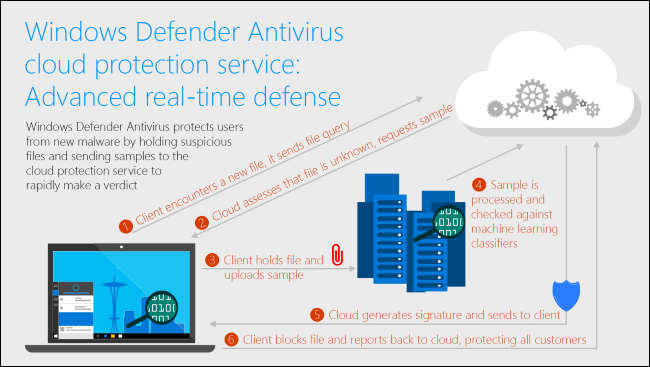
With the cloud-based protection feature, Windows Defender can send information to Microsoft's servers ("the cloud") whenever suspicious-looking events occur. Rather than making the decision entirely with the information available on your PC, the decision is made on Microsoft's servers with access to the latest malware information available from Microsoft's research time, machine-learning logic, and large amounts of up-to-date raw data.
Microsoft's servers send a near-instant response, telling Windows Defender that the file is probably dangerous and should be blocked, requesting a sample of the file for further analysis, or telling Windows Defender that everything is fine and the file should be run normally.
By default, Windows Defender is set to wait for up to 10 seconds to receive a response back from Microsoft's cloud protection service. If it hasn't heard back within this amount of time, it will let the suspicious file run. Assuming your Internet connection is fine, that should be more than enough time. The cloud service should often respond in less than a second.
Automatic Sample Submission
The Windows Defender interface notes that cloud-based protection works best with automatic sample submission enabled. That's because cloud-based protection can request a sample of a file is the file seems suspicious, and Windows Defender will automatically upload it to Microsoft's servers if you have this setting enabled.
This feature won't just haphazardly upload files from your system to Microsoft's servers. It will only upload .exe and other program files. It won't upload your personal documents and other files that could contain personal data. If a file could contain personal data but seems suspicious---for example, an Word document or Excel spreadsheet that seems to contain a potentially dangerous macro---you'll be prompted before it's sent to Microsoft.
When the file is uploaded to Microsoft's servers, the service quickly analyzes the file and its behavior to identify whether it's dangerous or not. If a file is found to be dangerous, it will be blocked on your system. The next time Windows Defender encounters that file on another person's PC, it can be blocked without needing extra analysis. Windows Defender learns the file is dangerous and blocks it for everyone.
There's also a "Submit a sample manually" link here, which takes you to the Submit a file for malware analysis page on Microsoft's website. You can manually upload a suspicious file here. However, with the default settings, Windows Defender will automatically upload potentially dangerous files and they can be blocked almost immediately. You won't even know a file was uploaded---if it's dangerous, it will just be blocked within a few seconds.
Why You Should Leave These Features Enabled
We recommend you leave these features enabled to help protect your PC against malware. Malware may appear and spread very quickly, and your antivirus may not download virus definition files frequently enough to stop it. These types of features help your antivirus respond much more quickly to new malware epidemics and block never-before-seen malware that would otherwise slip through the cracks.
Microsoft recently published a blog post that detailed a real-world example where a Windows user downloaded a new malware file. Windows Defender determined the file was suspicious and asked the cloud-based protection service for more information. Within the span of 8 seconds, the service had received an uploaded sample file, analyzed it to be malware, created an antivirus definition, and told Windows Defender to remove it from the PC. That file was then blocked on other Windows PCs whenever they encountered it thanks to the newly created virus definition.
This is why you should leave this feature enabled. Cut off from the cloud-based protection service, Windows Defender may have not had enough information and would have had to make a decision on its own, potentially allowing the dangerous file to run. With the cloud-based protection service, the file was labelled as malware---and all PCs protected by Windows Defender that found it in the future would know that file was dangerous.