Once you start digging into a Linux system, you may find some confusing or unexpected things, like /usr/bin/false, for example. Why is it there and what is its purpose? Today's SuperUser Q&A post has the answer to a curious reader's questions.
Today’s Question & Answer session comes to us courtesy of SuperUser—a subdivision of Stack Exchange, a community-driven grouping of Q&A web sites.
The Question
SuperUser reader user7326333 wants to know why some system users have /usr/bin/false as their shell:
Why do some system users have /usr/bin/false as their shell? What does that mean?
Why do some system users have /usr/bin/false as their shell?
The Answer
SuperUser contributors duDE, Toby Speight, and bbaassssiiee have the answer for us. First up, duDE:
This helps to prevent users from logging onto a system. Sometimes you need a user account for a specific task. Nevertheless, no one should be able to interact with this account on the computer. These are, on one hand, system user accounts. On the other hand, this is an account for which FTP or POP3 access is possible, but just no direct shell login.
If you look more closely at the /etc/passwd file, you will find the /bin/false command as a login shell for many system accounts. Actually, false is not a shell, but a command that does nothing and then also ends with a status code that signals an error. The result is simple. The user logs in and immediately sees the login prompt again.
Followed by the answer from Toby Speight:
These users exist to be the owner of specific files or processes and are not intended to be login accounts. If the value of the "shell" field is not listed in /etc/shells, then programs such as FTP daemons do not allow access. Additionally, for programs that do not check /etc/shells, they make use of the fact that /bin/false will immediately return and deny an interactive shell.
And our final answer from bbaassssiiee:
Some users have /usr/bin/false, others have /sbin/nologin, or they may even have /usr/bin/passwd. They can either be system users that are needed to isolate program permissions or human users of programs that use the password files for authentication.
Have something to add to the explanation? Sound off in the comments. Want to read more answers from other tech-savvy Stack Exchange users? Check out the full discussion thread here.
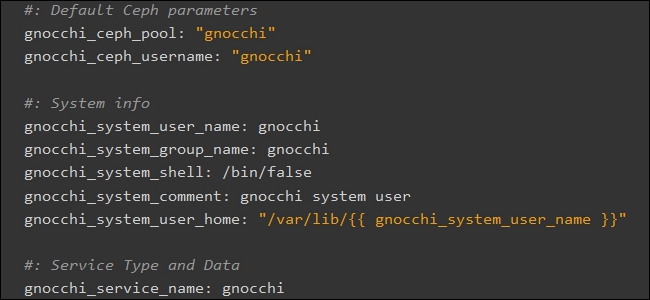
Image Credit: OpenStack Docs (OpenStack Project)