Quick Links
Key Takeaways
- Start with a Security Checkup- Use the built-in Security Checkup tool to review and confirm important information to ensure your account security.
- Set Sign-in and Recovery Options- Confirm recovery phone number and email address, and review devices that can be used to allow logins.
- Clean Up Apps That Have Permission to Access Your Account- Review and revoke access for any apps or devices that you no longer use or don't remember granting access to.
Out of all your online accounts, there's a good chance that Google holds most of your information. Think about it: if you use Gmail for email, Chrome for web browsing, and Android for your mobile OS, then you're already using Google for almost everything you do. Let's talk about how to make sure your account is as secure as it can be.
This Cybersecurity Awareness Week article is brought to you in association with Incogni.
Start with a Security Checkup
Google makes checking your account security very easy: just use the built-in Security Checkup tool on your account's "Sign in & security" page.
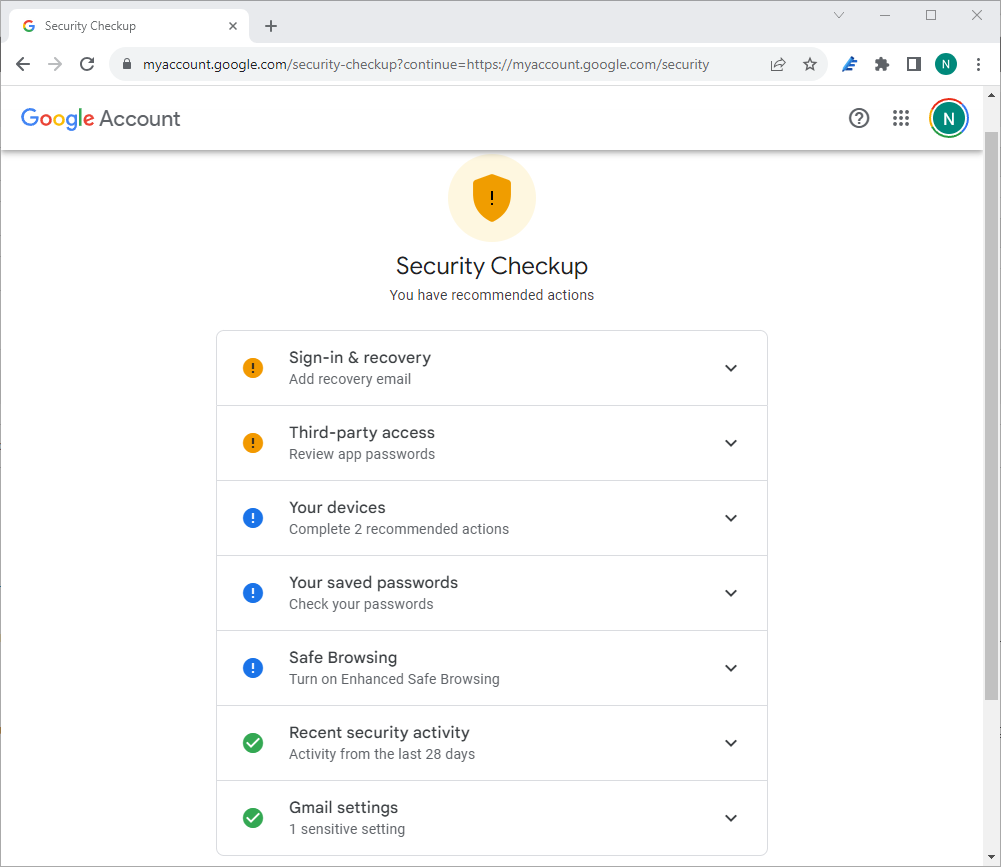
When you click the "Protect Your Account" option, you'll be tossed into a multi-section form that will basically just ask you to review and confirm some information — this shouldn't take that long, but you'll definitely want to take your time and thoroughly review the information you find here.
The order of these categories will change based on what Google thinks deserves most of your attention. Your order may not be the same as ours, but that isn't important — the categories are still the same.
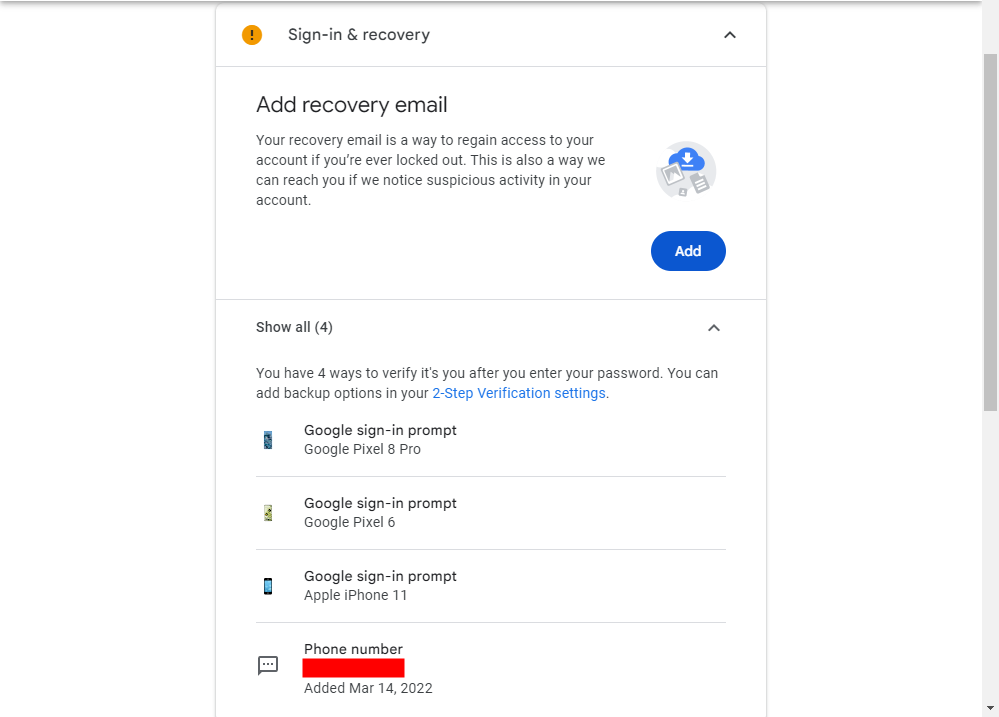
Set Sign-in and Recovery Options
The first option is very simple: confirm your recovery phone number and email address, and the devices that can be used to allow logins. Basically, if you get locked out of your Google account, you'll want to make sure this stuff is correct. Also, you'll get an email on your recovery account whenever your primary account is logged into a new location.
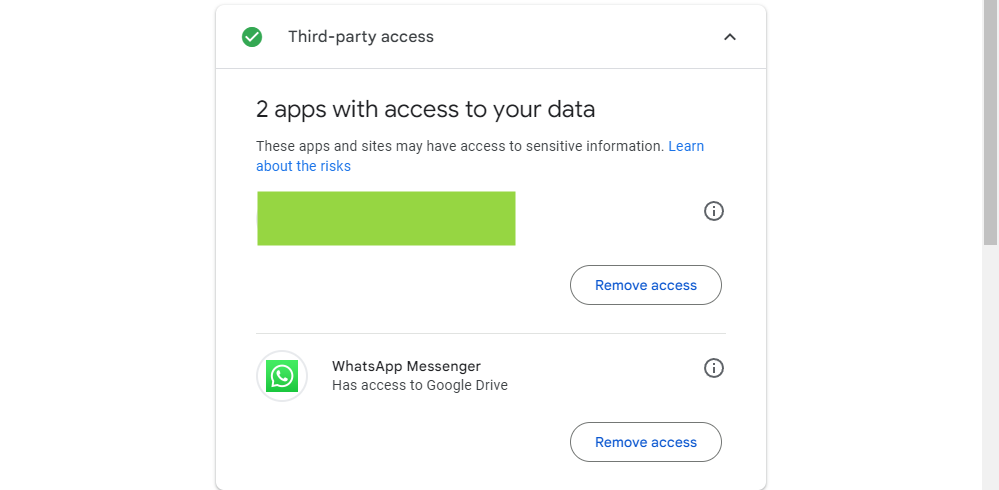
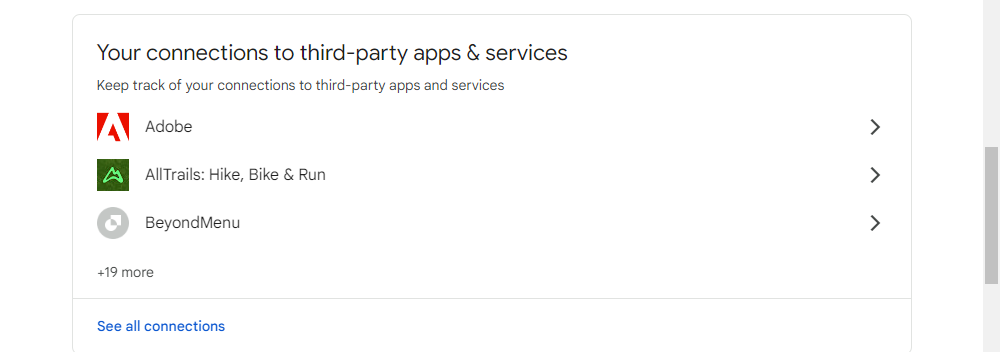
Clean Up Apps That Have Permission to Access Your Account
The next section is another important one: Account Permissions. Basically, this is anything that has access to your Google Account — anything you've logged into with Gmail or otherwise granted permissions to with your account. The list will not only show what the app or device is, but exactly what it has access to. If you don't remember granting something access (or just no longer use the app/device in question), then click the "remove" button to revoke its account access. If it's an account you actually use and accidentally remove, you'll just have to re-grant it access the next time you log in.
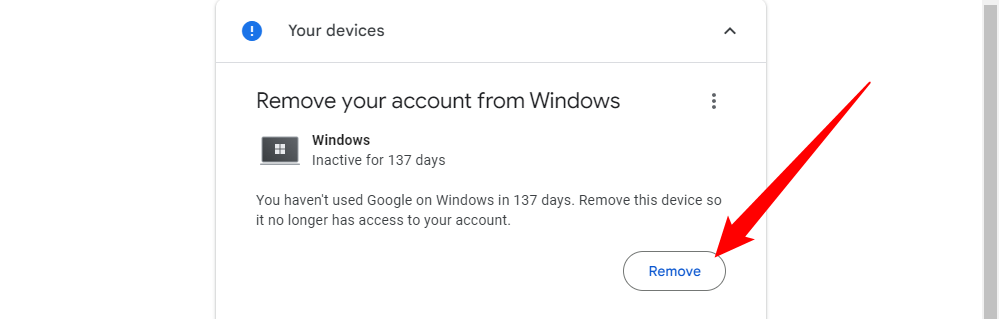
See What Other Devices Are Logged Into Your Account and Remove Old Devices
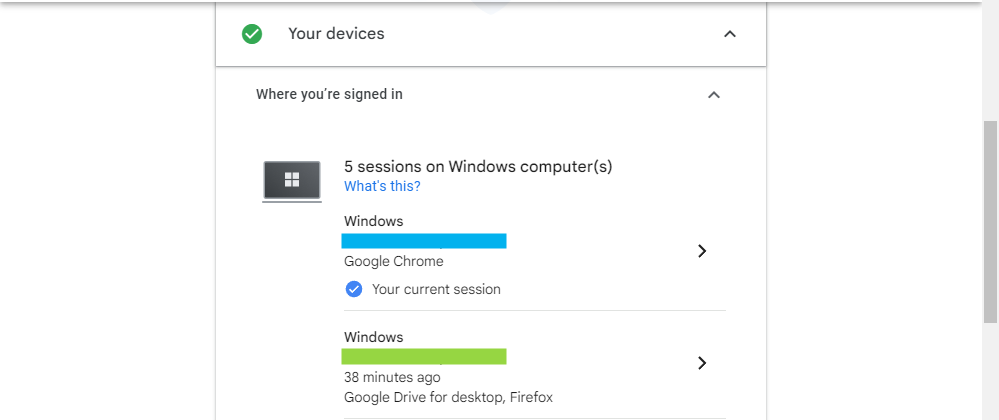
The next section may or may not take a while, depending on how many devices you have connected. This is definitely something you'll want to pay attention to, however: if you no longer have or use a specific device, there is no reason for it to have access to your account! It's also worth noting that if you've used the device semi-recently, the time, date, and location will show up next to the name.
Google helpfully brings old devices you haven't used to log in for a while right to the top of the list. This isn't a super critical security measure unless one of those devices was lost or stolen, but it never hurts either.
If you go down a bit you can also see where you're signed in by clicking the small arrow next to "Where You're Signed In." It is broken down by operating system, so if you're signed in on an iPhone, a Windows PC, and an Android phone, you'll see three separate regions. This is extremely helpful if you're trying to spot an intruder accessing your account. Just keep in mind that if you use a VPN, you may very well have strange locations displayed here.
Change Compromised Passwords
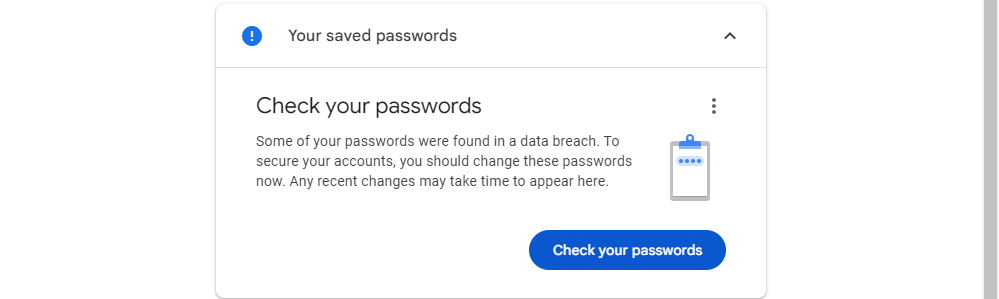
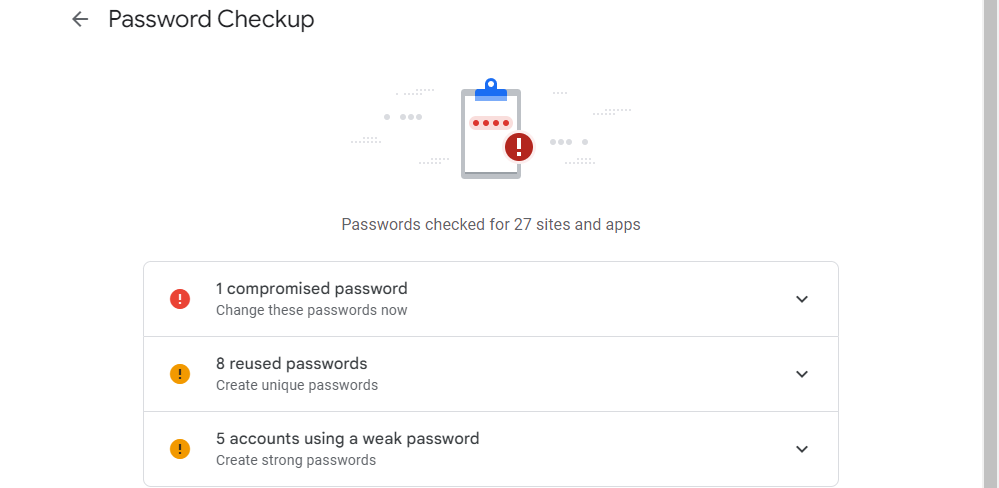
You can save passwords to your Google account if you want (you'll see this prompt a lot on Android devices and in Google Chrome). If a password saved to your Google Account is leaked, you'll see a notification about it here.
You'll have to jump through a few verification hoops before Google will actually display the problems it has with your passwords. It'll show you everything from compromised passwords to weak or reused passwords.
Credential stuffing is a very serious threat. You should change your leaked password immediately, and the password of any account that uses a similar password. For example, if your leaked password was "examplepassword1" for your Discord account, and you use "examplepassword2" as the password for your online banking login, it is important that you change both.
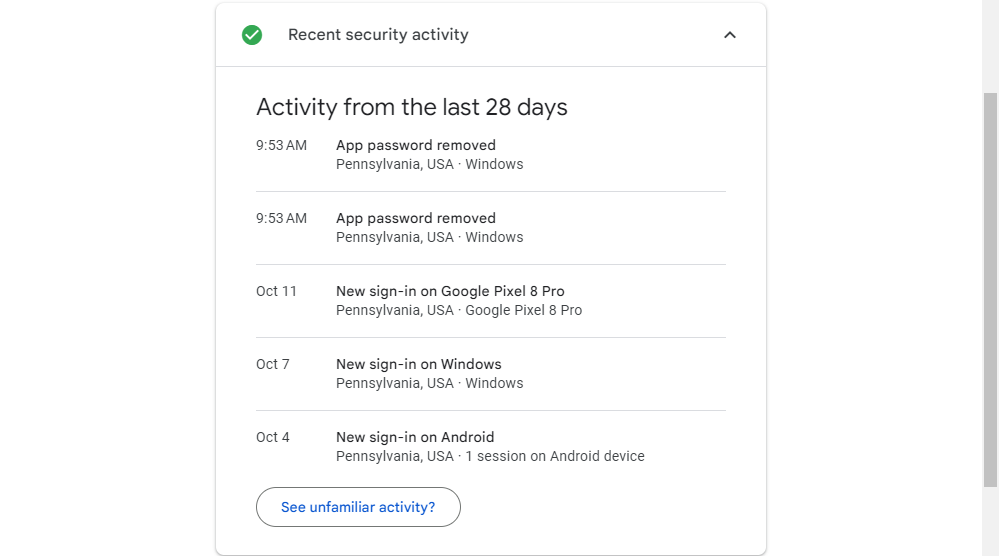
Check Recent Security Activity
The Recent Security Activity menu provides a convenient overview of every security related change on your account. If you add or remove a password, login from a strange location or with a new device, you'll see it here. If there is something and you haven't made any changes, definitely take a closer look — this could be indicative of some sort of suspicious activity on your account.
If something does look amiss, click the "See Unfamiliar Activity" button to change your password and sign out of all devices in one click.
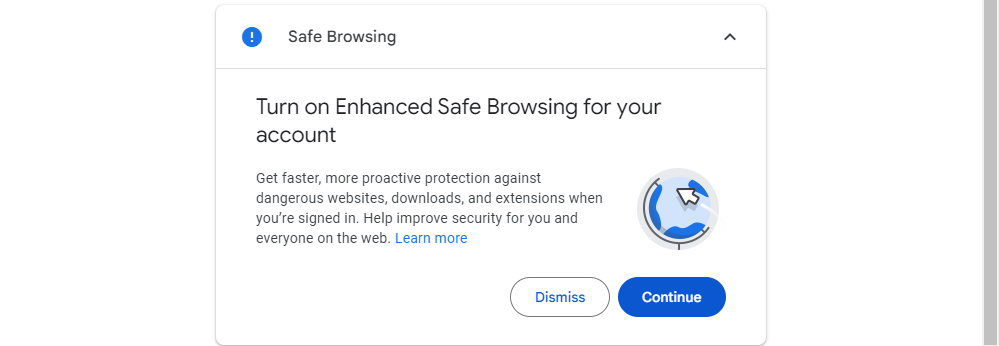
Enable Enhanced Safe Browsing (Optional)
Google also offers some enhanced browsing security for your account. This effectively filters your browsing before it reaches you, allowing Google to block any malicious sites before you land on them. This isn't really necessary, but you can opt in if you want.
Use a Strong Password and 2-Step Verification
If you've been on the internet for any reasonable amount of time, then you already know the spiel: use a strong password. Your child's name or birthday, your birthday, or anything else that can be easily guessed are not examples of strong passwords — those are the kinds of passwords you use when you basically want your data to get stolen. Hard truth, I know, but that's what it is.
We highly, highly recommend using some sort of a password generator and manager to get the strongest passwords possible — one that's part of a password vault is even better. You can use any password manager you like, just be sure to find a reputable company.
Once you have a strong password, it's time to set up 2-step authentication (also commonly referred to as two-factor authentication or "2FA") if you haven't already. Basically, this means that you need two things to get into your account: your password, and a second form of authentication — generally something that is only accessible to you. For example, you can receive a text message with a unique code, use an authentication app on your phone (like Google Authenticator or Authy), or even use Google's codeless authentication system, which is my personal favorite.
That way, your device is secured with something you know, and something you have. If someone gets your password, they won't be able to access your account unless they've also stolen your phone.
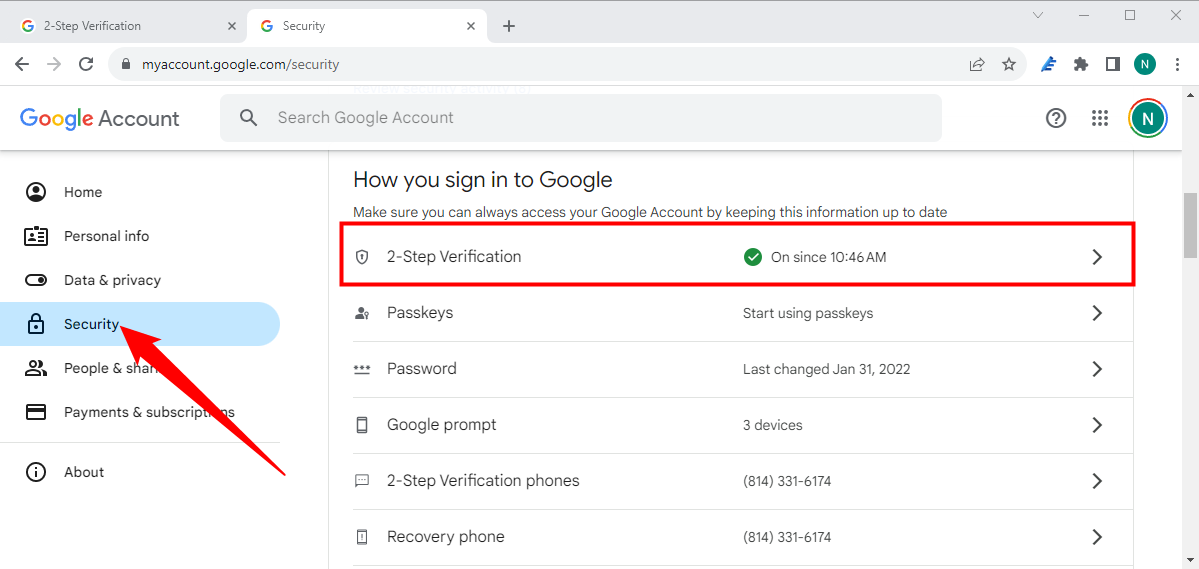
To change your password or set up 2-step verification, you first need to head into your Google Account Security Page, then scroll down to the "How You Sign In To Google" section. This is is where you'll see a breakdown of pertinent information, like the last time you changed your password, when you set up 2-step verification, and the like. To set up or modify your two-factor authenication, just click "2 Step Verification."
To change your password, click the "Password" box. You'll first be asked to input your current password, then be presented with a new password entry box. Easy enough.
Once you have 2-step verification set up (of if you had it set up in the first place), you can control exactly what your second step is— this is where you can change to the code-less "Google Prompt" method, switch to using an authenticator app, and make sure your backup codes are current.
To set up a new second step method, just use the "Set up alternative second step" section.
Boom, you're done: your account is now much safer. Good for you!
Keep an Eye on Connected Apps, Device Activity, and Notifications
The rest of the security page is pretty straightforward (and also a part of the Security Checkup we talked about earlier), as it covers connected devices, apps, and notification settings. More than something you can actively do, everything in the "Device activity & notifications" and "Connected apps & sites" are something you'll have to passively keep an eye on.
You can monitor account activity here — like devices that have recently been signed into your Google account, for example — along with currently logged-in devices and apps that have access to your account.
Securing your Google account isn't hard, nor is it all that time consuming, and it's something that everyone who has a Google account should do. Google has done an excellent job of putting everything in one place and making it incredibly easy to parse, control, and edit.