If you love tinkering with Windows and learning as you go, you may have noticed that Windows process and thread IDs are even-numbered and multiples of four. Why is that? Today's SuperUser Q&A post has the answers to a curious reader's questions.
Today’s Question & Answer session comes to us courtesy of SuperUser—a subdivision of Stack Exchange, a community-driven grouping of Q&A web sites.
The Question
SuperUser reader Peter Hahndorf wants to know why there are no odd-numbered Windows process IDs:
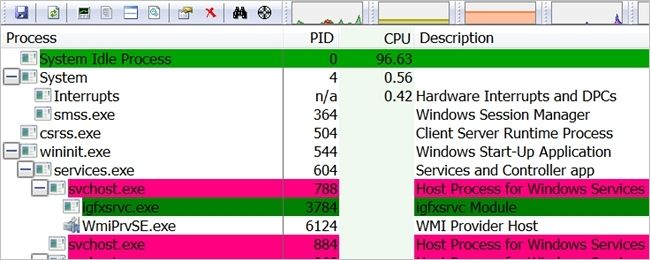
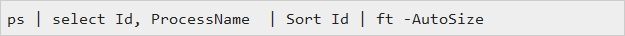
There are many ways to look at the process IDs in Windows. Using PowerShell:
I get this result:
As you can see, all the process IDs are even-numbered, not only that, they are all multiples of four. You can look as hard as you want and you will never find an odd-numbered process ID, at least not on any version that is Windows NT-based. What is the reason for this?
Why are there no odd-numbered Windows process IDs?
The Answer
SuperUser contributor DavidPostill has the answer for us:
Why are there no odd-numbered Windows process IDs?
The same code that allocates kernel handles is also used to allocate process and thread IDs. Since kernel handles are a multiple of four, so are process and thread IDs.
Why are process and thread IDs multiples of four?
On Windows NT-based operating systems, process and thread IDs always happen to be a multiple of four. Is this just a coincidence?
Yes, it is just a coincidence, and you should not rely on it since it is not part of the programming contract. For example, Windows 95 process and thread IDs were not always multiples of four. By comparison, the reason that kernel handles are always a multiple of four is part of the specification and will be guaranteed for the foreseeable future.
Process and thread IDs are multiples of four as a side-effect of code reuse. The same code that allocates kernel handles is also used to allocate process and thread IDs. Since kernel handles are multiples of four, so are process and thread IDs. This is an implementation detail, so do not write code that relies on it. I am just telling you to satisfy your curiosity.
Source: Why are process and thread IDs multiples of four?
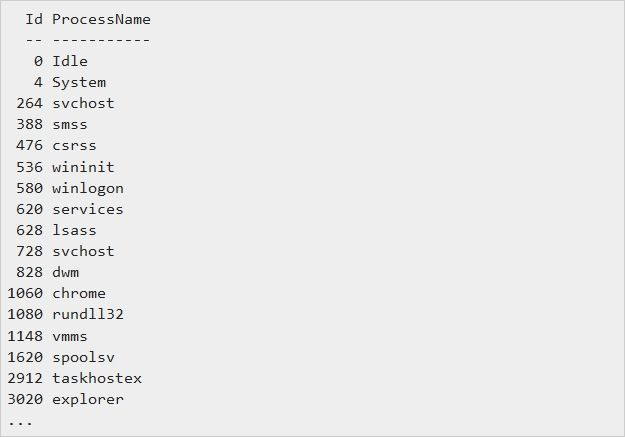
Why are kernel handles always a multiple of four?
Something that is not very well known is that the bottom two bits of kernel handles are always zero; in other words, their numeric value is always a multiple of four. Note that this applies only to kernel handles; it does not apply to pseudo-handles or to any other type of handle (USER handles, GDI handles, multimedia handles, etc.). Kernel handles are things you can pass to the CloseHandle function.
That at least the bottom bit of kernel handles are always zero is implied by the GetQueuedCompletionStatus function, which indicates that you can set the bottom bit of the event handle to suppress completion port notification. In order for this to work, the bottom bit must normally be zero.
This information is not useful for most application writers, which should continue to treat handles as opaque values. The people who would be interested in tag bits are those who are implementing low-level class libraries or are wrapping kernel objects inside a larger framework.
Source: Why are kernel handles always a multiple of four?
Further Reading
The Old New Thing: Practical Development Throughout the Evolution of Windows by Raymond Chen (Principal Software Design Engineer at Microsoft)
Have something to add to the explanation? Sound off in the comments. Want to read more answers from other tech-savvy Stack Exchange users? Check out the full discussion thread here.