Quick Links
You run a respectable website that your users can trust. Right? You might want to double check that. If your site is running on Microsoft Internet Information Services (IIS), you might be in for a surprise. When your users try to connect to your server over a secure connection (SSL/TLS) you may not be providing them a safe option.
Providing a better cipher suite is free and pretty easy to setup. Just follow this step by step guide to protect your users and your server. You’ll also learn how to test services you use to see how safe they really are.
Why Your Cipher Suites are Important
Microsoft’s IIS is pretty great. It’s both easy to setup and maintain. It has a user friendly graphical interface that makes configuration a breeze. It runs on Windows. IIS really has a lot going for it, but really falls flat when it comes to security defaults.
Here’s how a secure connection works. Your browser initiates a secure connection to a site. This is most easily identified by a URL starting with “HTTPS://”. Firefox offers up a little lock icon to illustrate the point further. Chrome, Internet Explorer, and Safari all have similar methods of letting you know your connection is encrypted. The server you’re connecting to replies to your browser with a list of encryption options to choose from in order of most preferred to least. Your browser goes down the list until it finds an encryption option it likes and we’re off and running. The rest, as they say, is math. (No one says that.)
The fatal flaw in this is that not all of the encryption options are created equally. Some use really great encryption algorithms (ECDH), others are less great (RSA), and some are just ill advised (DES). A browser can connect to a server using any of the options the server provides. If your site is offering up some ECDH options but also some DES options, your server will connect on either. The simple act of offering up these bad encryption options makes your site, your server, and your users potentially vulnerable. Unfortunately, by default, IIS provides some pretty poor options. Not catastrophic, but definitely not good.
How to See Where You Stand
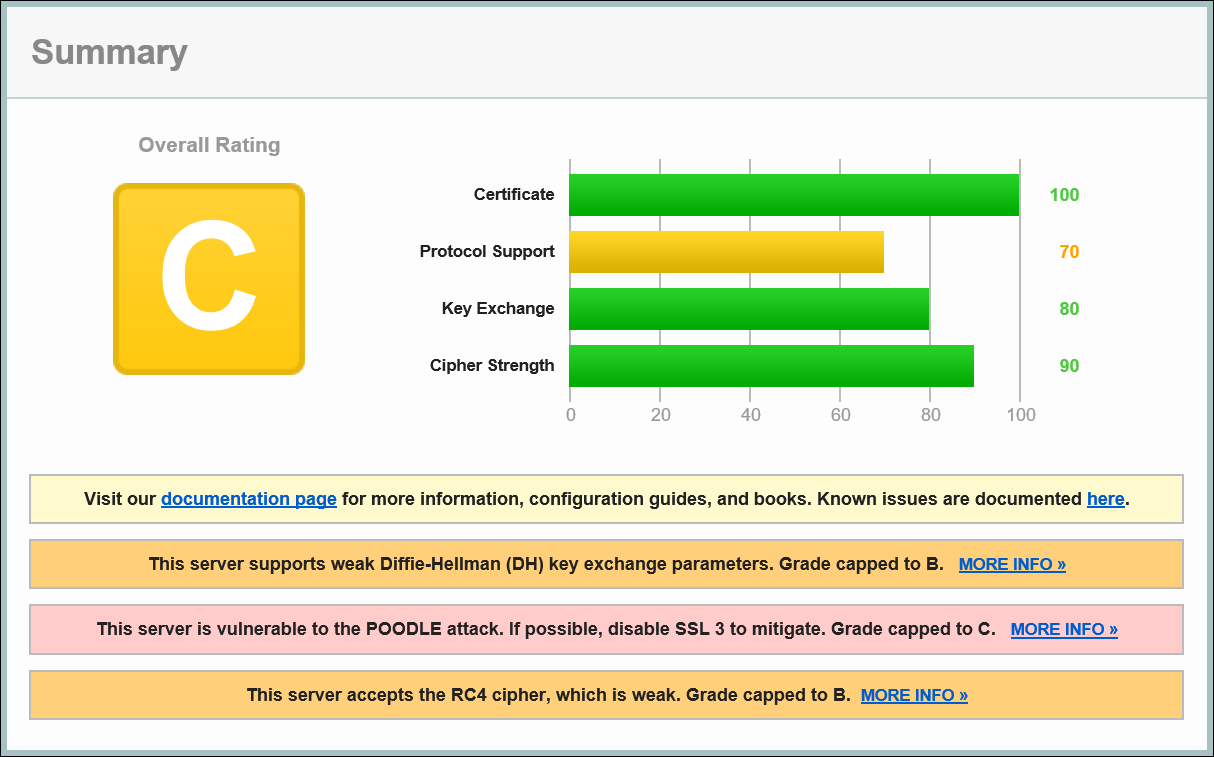
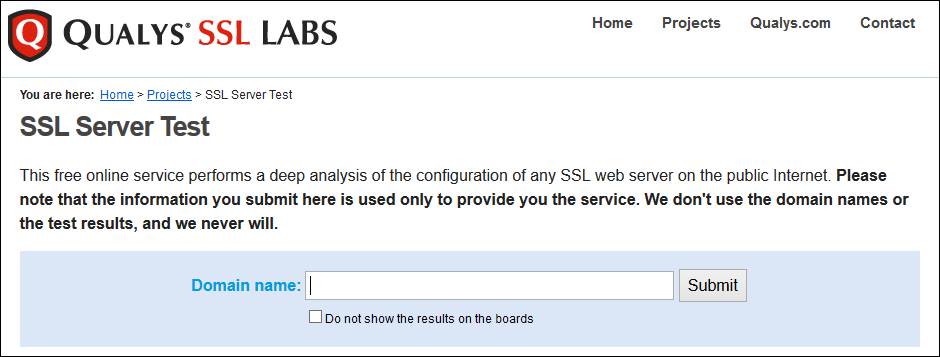
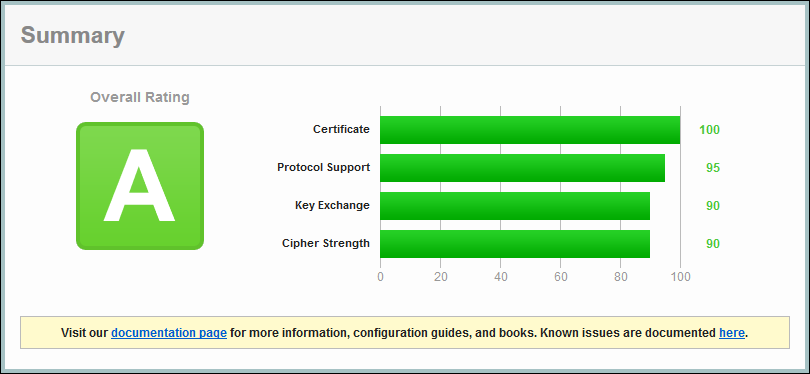
Before we start, you might want to know where your site stands. Thankfully the good folks at Qualys are providing SSL Labs to all of us free of charge. If you go to https://www.ssllabs.com/ssltest/, you can see exactly how your server is responding to HTTPS requests. You can also see how services you use regularly stack up.
One note of caution here. Just because a site doesn’t receive an A rating doesn’t mean the folks running them are doing a bad job. SSL Labs slams RC4 as a weak encryption algorithm even though there are no known attacks against it. True, it is less resistant to brute force attempts than something like RSA or ECDH, but it isn’t necessarily bad. A site may offer an RC4 connection option out of necessity for compatibility with certain browsers so use the sites rankings as a guideline, not an iron clad declaration of security or lack thereof.
Updating Your Cipher Suite
We’ve covered the background, now let’s get our hands dirty. Updating the suite of options your Windows server provides isn’t necessarily straightforward, but it definitely isn’t hard either.
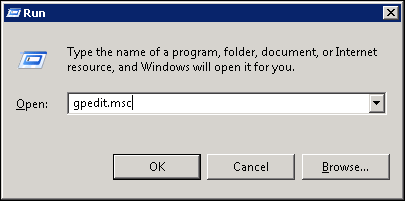
To start, press Windows Key + R to bring up the “Run” dialogue box. Type “gpedit.msc” and click “OK” to launch the Group Policy Editor. This is where we’ll make our changes.
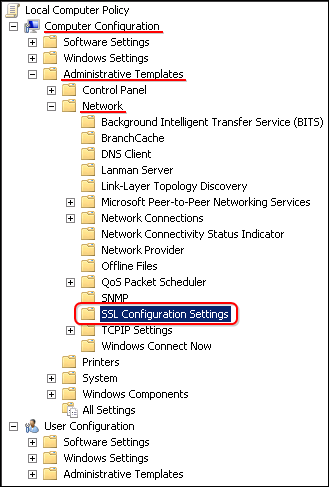
On the left hand side, expand Computer Configuration, Administrative Templates, Network, and then click on SSL Configuration Settings.
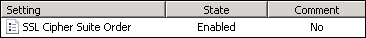
On the right hand side, double click on SSL Cipher Suite Order.
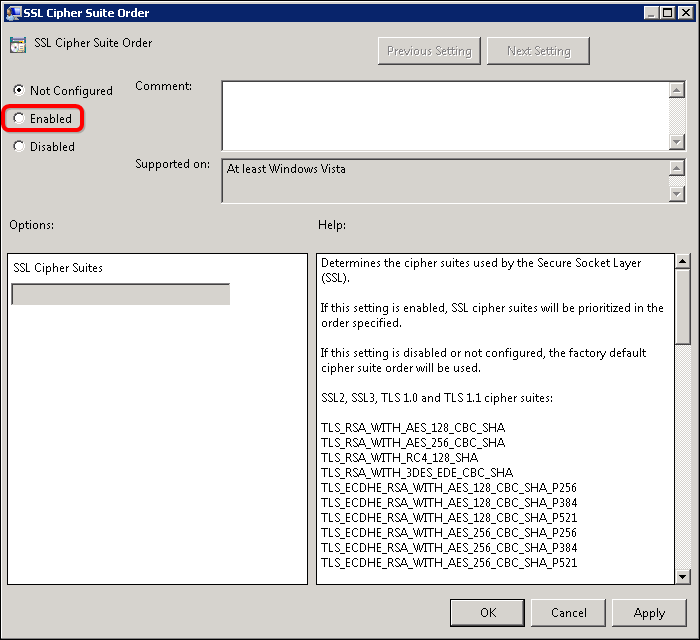
By default, the “Not Configured” button is selected. Click on the “Enabled” button to edit your server’s Cipher Suites.
The SSL Cipher Suites field will fill with text once you click the button. If you want to see what Cipher Suites your server is currently offering, copy the text from the SSL Cipher Suites field and paste it into Notepad. The text will be in one long, unbroken string. Each of the encryption options is separated by a comma. Putting each option on its own line will make the list easier to read.
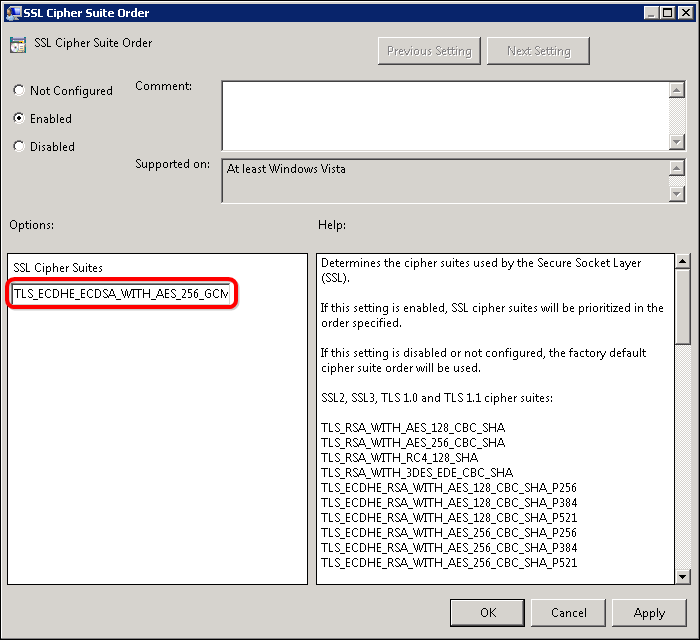
You can go through the list and add or remove to your heart’s content with one restriction; the list cannot be more than 1,023 characters. This is especially annoying because the cipher suites have long names like “TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384_P384”, so choose carefully. I recommend using the list put together by Steve Gibson over at GRC.com: https://www.grc.com/miscfiles/SChannel_Cipher_Suites.txt.
Once you’ve curated your list, you have to format it for use. Like the original list, your new one needs to be one unbroken string of characters with each cipher separated by a comma. Copy your formatted text and paste it into the SSL Cipher Suites field and click OK. Finally, to make the change stick, you have to reboot.
With your server back up and running, head over to SSL Labs and test it out. If everything went well, the results should give you an A rating.
If you would like something a little more visual, you can install IIS Crypto by Nartac (https://www.nartac.com/Products/IISCrypto/Default.aspx). This application will allow you to make the same changes as the steps above. It also lets you enable or disable ciphers based on a variety of criteria so you don’t have to go through them manually.
No matter how you do it, updating your Cipher Suites is an easy way to improve security for you and your end users.