Quick Links
Hollywood doesn't understand technology and "hacking." That's what we thought, anyway. But many of the ridiculous things we've seen in movies turned out to be completely true.
We laughed off many of these myths when we saw them in movies. "Don't believe what you see on TV," we told people. Boy, were we wrong.
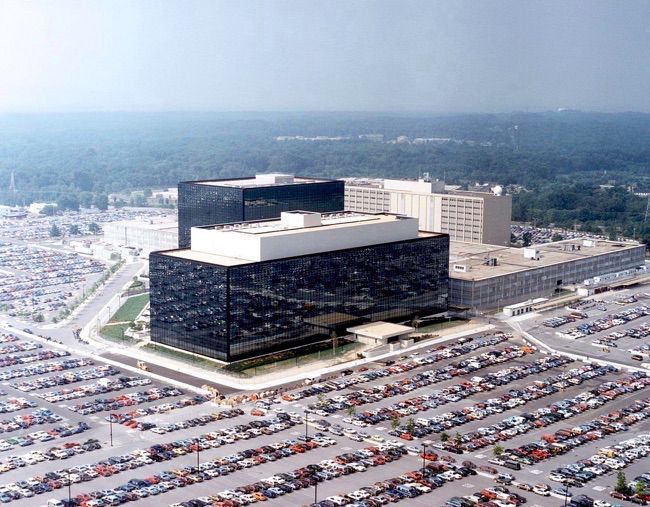
The NSA Spying on Everybody
One of the oldest themes is a government that knows all and sees all. If the hero needs some information to stop a plot, they can tap into a seemingly infinite amount of real-time information to find the villain, determine who they're communicating with, and then track them in real-time. Alternately, the all-seeing government surveillance state is often portrayed as a villain.
We all scoffed at this, but much of it appears to be true. The NSA (and other countries' intelligence agencies) are monitoring Internet traffic and phone calls, building up huge databases they can query. That scene where the hero taps into a massive database that gives them all the information they need -- well, it's more true than we could have ever imagined. Heck, even The Simpsons mentioned this in 2007's The Simpsons Movie!
Image Credit: Unknown on imgur
Your Location Can Be Tracked
Cell phones can be tracked by triangulating their relative signal strengths between three nearby cell towers, we know that. But the US government has gone to even greater lengths. They've placed fake cellular towers on small airplanes and flown over urban areas, intercepting communications between a suspect's cell phone and the real cell tower to determine someone's exact location without even needing to a cellular carrier for help. (Source)
Yes, that scene where a hero boards an airplane and flies over an urban area, staring at a map as they track a suspect's exact location somehow -- that's true, too.
Webcam Hijacking
Webcams can be scary. They offer a way for an unseen attacker to view us from afar. They may be used by a twisted mind to exploit someone, demanding that someone strip for the webcam or their secrets or private photographs will be sent to family members or the public. Or, a webcam may simply function as a convenient way for someone to snoop on an otherwise-secure area.
Webcam hijacking is certainly real, too. There's a whole community of twisted minds using RAT (Remote Access Tool) software to spy on people, hoping to catch a glimpse of them undressing, and attempting to manipulate them into stripping for the camera. (Source) The UK's GHCQ intelligence agency captured millions of Yahoo! webcam images, including many pornographic ones. (Source)
Hacking Traffic Lights and Cameras
Cut to the dramatic chase scene. Our heroes are chasing after a skilled hacker. Or, our heroes need to use their hacking skills to catch up with the villain. Either way, someone is manipulating the traffic cameras, turning them green when they need to drive through and red when their pursuers need to drive through. Or, our heroes hack into the traffic camera grid to spy on someone's movements throughout a city. Or, even worse, a city is taken over by a supervillian who turns all the traffic lights green to cause chaos while cackling maniacally.
That makes for a dramatic scene, but it's silly -- or is it? It turns out that hacking traffic lights and their cameras is often trivial. Researchers have found that many traffic lights are connected to open Wi-Fi networks and using default passwords. (Source)
2003's The Italian Job features a character "hacking" traffic lights, turning all lights at an intersection green to create a traffic jam.
Darknet Drug Rings, Arms Trafficking, and Hitmen
There's a secret part of the Internet where the criminals lurk, below the shiny exterior that us upstanding citizens walk over everyday. You can get anything here, for a price. Any type of illegal drug you want, stolen credit card numbers, fake identification documents, illegal weapons, and professional hitmen for hire.
Much of this is true thanks to the "darknet" -- Tor hidden services, for example. It's become more public knowledge thanks to the bust of Silk Road, but other sites have sprung up. Of course, there's no guarantee all this stuff is actually legitimate. When Silk Road's "Dread Pirate Roberts" attempted to hire hitmen and pay them in BitCoin, he seems to have hired both someone who took the money and vanished as well as police who used it to build a case against him. There's no evidence the hundreds of thousands of dollars in BitCoin he spent actually got anyone killed, so maybe this criminal mastermind isn't as clever as he thought he was. (Source)
Hacking Security Cameras and Security Systems
Our heroes -- or villains -- need to break into a secure location. To scope it out, they hack the security cameras and examine the place's security, noting the amount of guards, their patrols, and other security features they'll need to bypass.
It's convenient, but also not too hard. Many IP security cameras have horifically weak security and can be trivially hacked. You can even find websites that provide a list of publicly exposed security cameras you scan snoop on yourself. (Source)
Like many other products, security systems themselves often have horrifically weak security, so they can be shut down or jammed if someone put the effort in.
Hacking ATMs for Cash
ATMs are a great hacking target. If someone needs some cash, they can simply hack an ATM to get it. While the ATM may not start shooting bills all over the street as it might in the movies, we've also seen a variety of ATM hacks springing up. The most pedestrian of them involve attaching a magnetic strip reader and camera to the machine itself to "skim" people's ATM card credentials, but there are attacks that work directly by hacking the ATM's software. (Source)
This one shows up as far back as 1991's Terminator 2, where John Connor jacks a device into an ATM and gets it to dispense some free cash.
Security Backdoors in Encryption Protocols
"It's no good, sir -- he isn't talking. We'll never break the encryption on his hard drive." It's a line that might be spoken before a clever government hacker speaks up and says it's no problem. After all, the government has a backdoor into the encryption and can crack it. That's just a dramatic version of a possible scene -- in reality, this usually manifests itself as the government being able to crack any encryption it wants, just because.
We've now seen backdoors inserted into encryption systems in the real world. The NSA manipulated the NIST into inserting a backdoor into the Dual_EC_DRBG encryption standard, which was recommended by the US government. (Source) The NSA then paid $10 million to RSA Security in a secret deal, and this compromised encryption standard was then used by default in their BSAFE library. (Source) And that's just a backdoor we know about.
Windows 8.1's default "device encryption" goes out of its way to hand a recovery key over to Microsoft, so the government could get it from them. Backdoors may also look like this one in Windows, which offers some convenient features for Windows users, access for the US government, and plausible deniability for Microsoft.
Hotel Key Cards Can Be Easily Hacked
Does someone want to get into a hotel room? No problem! Hotel room locks are easily hijacked thanks to their card readers. Just pop open the lock, do something with the wires, and you're in.
Whoever invented this myth probably didn't spend much time thinking of it, but it's possible. With some cheap hardware and a few seconds, an attacker could open up the assembly on the outside of the lock, plug hardware into an open port, read the decryption key from memory, and open the lock. Millions of hotel room locks around the world are vulnerable to this. (Source)
Onity, the company that manufactured the locks, will give hotels a cap to put over the port and screws that make the assembly harder to unscrew. But hotels don't want to fix this, and Onity doesn't want to give out replacement locks for free, so many locks will never be fixed. (Source)
Passwords Can Be Easily Hacked
Passwords are never too much of an obstacle in the movies. Either a clever person sits down and attempts to guess someone's password, or they plug something in and quickly crack their password.
Many passwords are horrible, so trying combinations like "password," "letmein," a child's name, a pet's name, a spouse's birthday, and other obvious bits of data will often let you luck into someone's password. And, if you re-use the same password in multiple places, attackers probably already have login information for your accounts.
If you do gain access to a password database so you can perform a brute-force attack against it, it's often quick to guess the password thanks to lists that include obvious, common passwords. Rainbow tables also speed this up, offering precomputed hashes that let you quickly identify common passwords without spending a lot of computing power. (Source)
These are far from the only myths that turned out to be true. If there's one common thread here, it's that security (and privacy) is often an afterthought in the real world, and the technology we use is never as secure as we'd like it to be. As we charge towards ever-more connected devices thanks to "The Internet of Things," we'll need to take security much more seriously.
Image Credit: Kenneth Lu on Flickr, Aleksander Markin on Flickr, Sean McGrath on Flickr, Tax Credits on Flickr, NSA