Quick Links
Thanks to bad design decisions, AutoRun was once a huge security problem on Windows. AutoRun helpfully allowed malicious software to launch as soon as you inserted discs and USB drives into your computer.
This flaw wasn't only exploited by malware authors. It was famously used by Sony BMG to hide a rootkit on music CDs. Windows would automatically run and install the rootkit when you inserted a malicious Sony audio CD into your computer.
The Origin of AutoRun
AutoRun was a feature introduced in Windows 95. When you inserted a software disc into your computer, Windows would automatically read the disc, and -- if an autorun.inf file was found in the root directory of the disc -- it would automatically launch the program specified in the autorun.inf file.
This is why, when you inserted a software CD or PC game disc into your computer, it automatically launched an installer or splash screen with options. The feature was designed to make such discs easy to use, reducing user confusion. If AutoRun didn't exist, users would have to open the file browser window, navigate to the disc, and launch a setup.exe file from there instead.
This worked quite well for a time, and there were no big issues. After all, home users didn't have an easy way to produce their own CDs before CD burners were widespread. You'd really only come across commercial discs, and they were generally trustworthy.
But even back in Windows 95 when AutoRun was introduced, it wasn't enabled for floppy disks. After all, anyone could place whatever files they wanted on a floppy disk. AutoRun for floppy disks would allow malware to spread from floppy to computer to floppy to computer.
AutoPlay in Windows XP
Windows XP refined this feature with an "AutoPlay" function. When you inserted a disc, USB flash drive, or another type of removable media device, Windows will examine its contents and suggest actions to you. For example, if you insert an SD card containing photos from your digital camera, it will recommend you do something appropriate for picture files. If a drive has an autorun.inf file, you'll see an option asking if you want to automatically run a program from the drive as well.
However, Microsoft still wanted CDs to work the same. So, in Windows XP, CDs and DVDs would still automatically run programs on them if they had an autorun.inf file, or would automatically begin playing their music if they were audio CDs. And, due to the security architecture of Windows XP, those programs would probably launch with Administrator access. In other words, they'd have full access to your system.
With USB drives containing autorun.inf files, the program would not automatically run, but would present you with the option in an AutoPlay window.
You could still disable this behavior. There were options buried in the operating system itself, in the registry, and the group policy editor. You could also hold down the Shift key as you inserted a disc and Windows wouldn't perform the AutoRun behavior.
Some USB Drives Can Emulate CDs, and Even CDs Aren't Safe
This protection began to break down immediately. SanDisk and M-Systems saw the CD AutoRun behavior and wanted it for their own USB flash drives, so they created U3 flash drives. These flash drives emulated a CD drive when you connect them to a computer, so a Windows XP system will automatically launch programs on them when they're connected.
Of course, even CDs aren't safe. Attackers could easily burn a CD or DVD drive, or use a rewritable drive. The idea that CDs are somehow safer than USB drives is wrong-headed.
Disaster 1: The Sony BMG Rootkit Fiasco
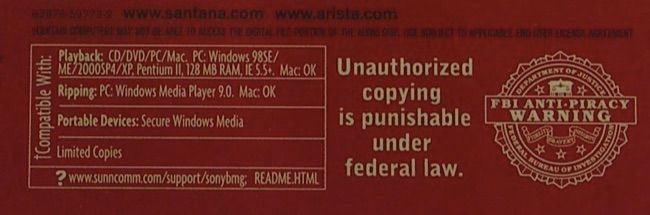
In 2005, Sony BMG began shipping Windows rootkits on millions of their audio CDs. When you inserted the audio CD into your computer, Windows would read the autorun.inf file and automatically run the rootkit installer, which sneakily infected your computer in the background. The purpose of this was to prevent you from copying the music disc or ripping it to your computer. Because these are normally supported functions, the rootkit had to subvert your entire operating system to suppress them.
This was all possible thanks to AutoRun. Some people recommended holding Shift whenever you inserted an audio CD into your computer, and others openly wondered if holding Shift to suppress the rootkit from installing would be considered a violation of the DMCA's anti-circumvention prohibitions against bypassing copy protection.
Others have chronicled the long, sorry history her. Let's just say the rootkit was unstable, malware took advantage of the rootkit to more easily infect Windows systems, and Sony got a huge and well-deserved black eye in the public arena.
Disaster 2: The Conficker Worm and Other Malware
Conficker was a particularly nasty worm first detected in 2008. Among other things, it infected connected USB devices and created autorun.inf files on them that would automatically run malware when they were connected to another computer. As antivirus company ESET wrote:
"USB drives and other removable media, which are accessed by the Autorun/Autoplay functionalities each time (by default) you connect them to your computer, are the most frequently used virus carriers these days."
Conficker was the most well-known, but it wasn't the only malware to abuse the dangerous AutoRun functionality. AutoRun as a feature is practically a gift to malware authors.
Windows Vista Disabled AutoRun By Default, But...
Microsoft eventually recommended that Windows users disable the AutoRun functionality. Windows Vista made some good changes that Windows 7, 8, and 8,1 have all inherited.
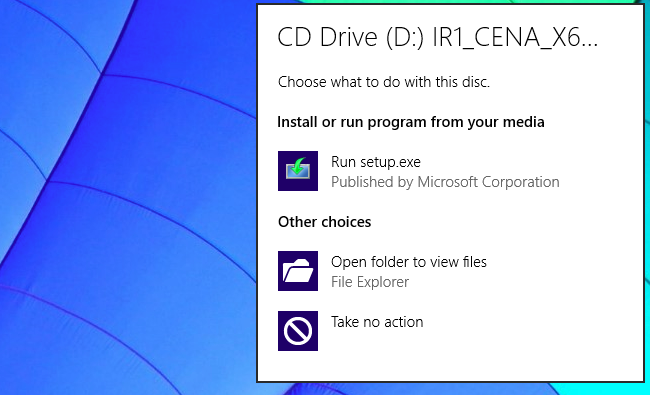
Instead of automatically running programs from CDs, DVDs, and USB drives masquerading as discs, Windows simply shows the AutoPlay dialog for these drives as well. If a connected disc or drive has a program, you'll see it as an option in the list. Windows Vista and later versions of Windows won't automatically run programs without asking you -- you'd have to click the "Run [program].exe" option in the AutoPlay dialog to run the program and get infected.
But it would still be possible for malware to spread via AutoPlay. If you connect a malicious USB drive to your computer, you're still just one click away from running the malware via the AutoPlay dialog -- at least with the default settings. Other security features like UAC and your antivirus program can help protect you, but you should still be alert.
And, unfortunately, we now have an even scarier security threat from USB devices to be aware of.
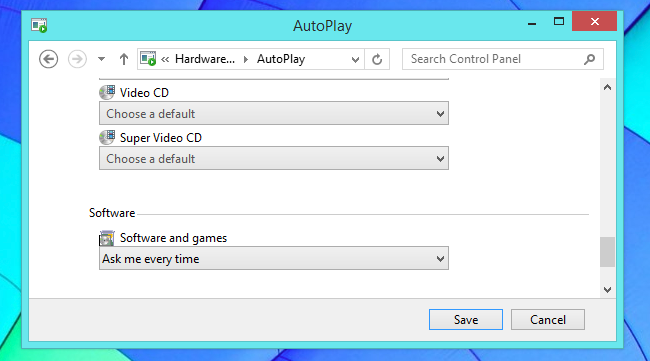
If you like, you can disable AutoPlay entirely -- or just for certain types of drives -- so you won't get an AutoPlay pop-up when you insert removable media into your computer. You'll find these options in the Control Panel. Perform a search for "autoplay" in the Control Panel's search box to find them.
Image Credit: aussiegal on Flickr, m01229 on Flickr, Lordcolus on Flickr