Quick Links
USB devices are apparently more dangerous than we've ever imagined. This isn't about malware that uses the AutoPlay mechanism in Windows---this time, it's a fundamental design flaw in USB itself.
Now you really shouldn't pick up and use suspicious USB flash drives you find lying around. Even if you ensured they were free of malicious software, they could have malicious firmware.
It's All In The Firmware
USB stands for "universal serial bus." It's supposed to be a universal type of port and communication protocol that allows you to connect many different devices to your computer. Storage devices like flash drives and external hard drives, mice, keyboards, game controllers, audio headsets, network adapters, and many other type of devices all use USB over the same type of port.
These USB devices---and other components in your computer---run a type of software known as "firmware." Essentially, when you connect a device to your computer, the firmware on the device is what allows the device to actually function. For example, a typical USB flash drive firmware would manage transferring the files back and forth. A USB keyboard's firmware would convert physical key-presses on a keyboard to digital key-press data sent over the USB connection to the computer.
This firmware itself isn't actually a normal piece of software that your computer has access to. It's the code running the device itself, and there's no real way to check for and verify a USB device's firmware is safe.
What Malicious Firmware Could Do
The key to this problem is the design goal that USB devices could do many different things. For example, a USB flash drive with malicious firmware could function as a USB keyboard. When you connect it to your computer, it could send keyboard-press actions to the computer as if someone sitting at the computer were typing the keys. Thanks to keyboard shortcuts, a malicious firmware functioning as a keyboard could---for example---open a Command Prompt window, download a program from a remote server, run it, and agree to a UAC prompt.
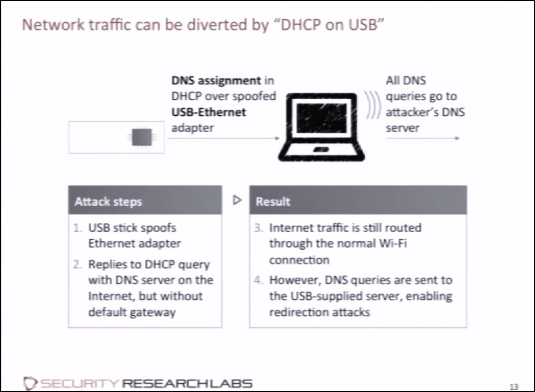
More sneakily, a USB flash drive could appear to function normally, but the firmware could modify files as they leave the device, infecting them. A connected device could function as a USB Ethernet adapter and route traffic over malicious servers. A phone or any type of USB device with its own Internet connection could use that connection to relay information from your computer.
A modified storage device could function as a boot device when it detects the computer is booting, and the computer would then boot from USB, loading a piece of malware (known as a rootkit) that would then boot the real operating system, running underneath it.
Importantly, USB devices can have multiple profiles associated with them. A USB flash drive could claim to be a flash drive, a keyboard, and a USB Ethernet network adapter when you insert it. It could function as a normal flash drive while reserving the right to do other things.
This is just a fundamental issue with USB itself. It enables the creation of malicious devices that can pretend to only be one type of device, but also be other types of devices.
Computers Could Infect a USB Device's Firmware
This is rather terrifying so far, but not completely. Yes, someone could create a modified device with a malicious firmware, but you probably won't come across those. What are the odds you'll be handed a specially crafted malicious USB device?
The "BadUSB" proof-of-concept malware takes this to a new, scarier level. Researchers for SR Labs spent two months reverse-engineering basic USB firmware code on many devices and found that it could actually be reprogrammed and modified. In other words, an infected computer could reprogram a connected USB device's firmware, turning that USB device into a malicious device. That device could then infect other computers it was connected to, and the device could spread from computer to USB device to computer to USB device, and on and on.
This has happened in the past with USB drives containing malware that depended on the Windows AutoPlay feature to automatically run malware on computers they were connected to. But now antivirus utilities can't detect or block this new type of infection that could spread from device to device.
This could potentially be combined with "juice jacking" attacks to infect a device as it charges via USB from a malicious USB port.
The good news is that this is only possible with about 50% of USB devices as of late 2014. The bad news is that you can't tell which devices are vulnerable and which aren't without cracking them open and examining the internal circuitry. Manufacturers will hopefully design USB devices more securely to protect their firmware from being modified in the future. However, for the meantime, a huge amount of USB devices in the wild are vulnerable to being reprogrammed.
Is This a Real Problem?
So far, this has proven to be a theoretical vulnerability. Real attacks have been demonstrated, so it's a real vulnerability---but we haven't seen it exploited by any actual malware in the wild yet. Some people have theorized that the NSA has known about this problem for a while and has used it. The NSA's COTTONMOUTH exploit appears to involve using modified USB devices to attack targets, although it appears the NSA is also implanted specialized hardware into these USB devices.
Nevertheless, this problem is probably not something you'll run into any time soon. In an everyday sense, you probably don't need to view your friend's Xbox controller or other common devices with much suspicion. However, this is a core flaw in USB itself that should be fixed.
How You Can Protect Yourself
You should exercise caution when dealing with suspicious devices. In the days of Windows AutoPlay malware, we would occasionally hear about USB flash drives left in company parking lots. The hope was that an employee would pick up the flash drive and plug it into a company computer, and then the drive's malware would automatically run and infect the computer. There were campaigns to raise awareness of this, encouraging people not to pick up USB devices from the parking lots and connect them to their computers.
With AutoPlay now disabled by default, we tend to think the problem is solved. But these USB firmware problems show suspicious devices can still be dangerous. Don't pick up USB devices from parking lots or the street and plug them in.
How much you should worry depends on who you are and what you're doing, of course. Companies with critical business secrets or financial data might want to be extra careful of what USB devices can plug into what computers, preventing infections from spreading.
Although this problem has only been seen in proof-of-concept attacks so far, it exposes a huge, core security flaw in the devices we use everyday. It's something to bear in mind, and---ideally---something that should be solved to improve the security of USB itself.
Image Credit: Harco Rutgers on Flickr