Quick Links
Ever since the first person wrote out 5318008 on a calculator, nerds have been hiding secret numbers inside of your PC, and using them to negotiate secret handshakes between applications and files. Today we take a quick look at some of the more entertaining examples.
What are Magic Numbers?
Most programming languages use a 32-bit integer type to represent certain types of data behind the scenes -- internally the number is stored in RAM or used by the CPU as 32 ones and zeros, but in the source code it would be written out in either regular decimal format, or as hexadecimal format, which uses the numbers 0 through 9 and the letters A through F.
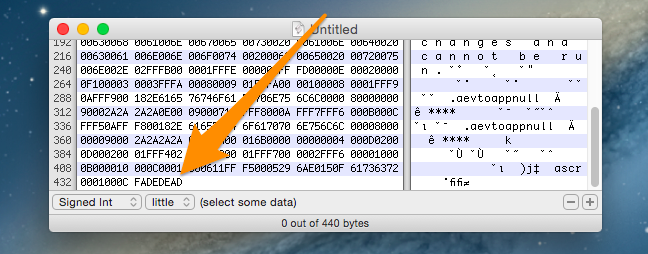
When the operating system or an application wants to determine the type of a file, it can look to the beginning of the file for a special marker that signifies the type of the file. For instance, a PDF file might start with the hex value 0x255044462D312E33, which equals "%PDF-1.3" in ASCII format, or a ZIP file starts with 0x504B, which equals "PK", which descends from the original PKZip utility. By looking at this "signature," a file type can be easily identified even without any other metadata.
The Linux utility "file" can be used from the terminal to determine the type of a file -- in fact, it reads the magic numbers from a file called "magic."
When an application wants to call a function, it can pass values to that function using standard types like integer, which can be expressed in the source code in hexadecimal format. This is especially true for constants, which are identifiers defined with human-readable names like AUTOSAVE_INTERVAL, but they map to actual integer (or other type) values. So instead of a programmer typing out a value like 60 every time they call the function in the source code, they could use the AUTOSAVE_INTERVAL constant for better readability. (Constants are usually easily recognized because they are written in all capital letters).
All of these examples can fall under the term Magic Numbers, because they might require a specific hexadecimal number in order for a function or file type to work properly... if the value isn't correct it won't work. And when a programmer wants to have a little fun, they might define these values using hexadecimal numbers that spell out something in English, otherwise known as hexspeak.
Fun With Magic Numbers: Some Notable Examples
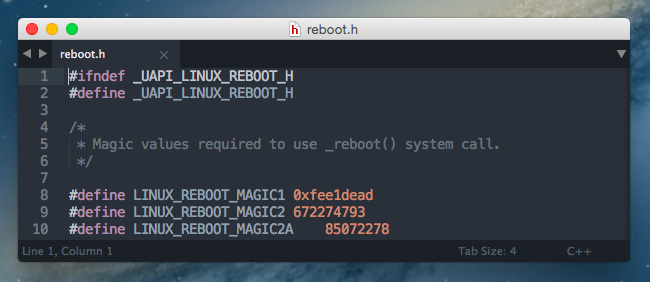
If you take a quick look into the Linux source code, you'll see that the _reboot() system call on Linux requires a "magic" variable to be passed that equals the hexadecimal number 0xfee1dead. If something tried to call that function without passing in that magic value first, it would just return an error.
The GUID (globally unique identifier) for a BIOS boot partition in the GPT partitioning scheme is 21686148-6449-6E6F-744E-656564454649, which forms the ASCII string "Hah!IdontNeedEFI", an allusion to the fact that GPT would normally be used in computers that replaced BIOS with UEFI, but it doesn't necessarily have to be.
Microsoft famously hid 0x0B00B135 in their Hyper-V virtual-machine supporting source code submitted to Linux, then they changed the value to 0xB16B00B5, and finally they switched it to decimal before it was removed from the source code altogether.
More fun examples include:
- 0xbaaaaaad - used by iOS crash logging to indicate that a log is a stackshot of the entire system.
- 0xbad22222 - used by iOS crash logging to indicate that a VoIP app has been killed by iOS because it misbehaved.
- 0x8badf00d - (Ate Bad Food) used by iOS crash logs to indicate that an application took too long to do something and was killed by the watchdog timeout.
- 0xdeadfa11 - (Dead Fall) used by iOS crash logging when an app is force quit by a user.
- 0xDEADD00D - used by Android to indicate a VM abort.
- 0xDEAD10CC (Dead Lock) used by iOS crash logging when an application locks a resource in the background.
- 0xBAADF00D (Bad Food) used by the LocalAlloc function in Windows for debugging.
- 0xCAFED00D (Cafe dude) used by Java's pack200 compression.
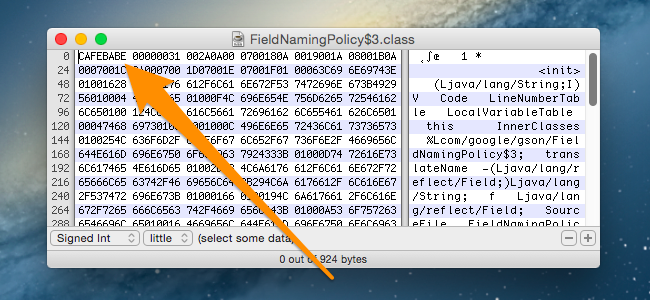
- 0xCAFEBABE (Cafe babe) used by Java as the identifier for compiled class files
- 0x0D15EA5E (Disease) used by Nintendo on the Gamecube and Wii to indicate a normal boot happened.
- 0x1BADB002 (1 bad boot) used by the multiboot specification as a magic number
- 0xDEADDEAD - used by Windows to indicate a manually initiated debug crash, otherwise known as the Blue Screen of Death.
These aren't the only ones out there, of course, but just a short list of examples that seemed fun. Know of any more? Tell us in the comments.
Seeing Examples for Yourself
You can see more examples by opening up a hex editor and then opening up any number of file types. There are plenty of freeware hex editors available for Windows, OS X, or Linux -- just make sure you are careful when installing freeware to not get infected with crapware or spyware.
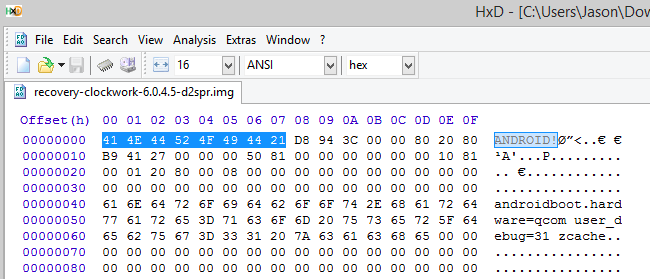
As an added example, recovery images for Android phones like ClockworkMod start with "ANDROID!" if read in ASCII format.
Note: don't go changing anything while you're looking around. Hex editors can break things!