Quick Links
A credit card skimmer is a malicious device criminals attach to a payment terminal---most commonly on ATMs and gas pumps. When you use an terminal that's been compromised in such a way, the skimmer will create a copy of your card and capture your PIN (if it's an ATM card).
If you use ATMs and gas pumps, you should be aware of these attacks. Armed with the right knowledge, it's actually pretty easy to spot most skimmers---though just like with everything else, these types of attacks continue to get more advanced.
How Skimmers Work
A skimmer traditionally has two components. The first is a small device that's generally inserted over the card slot. When you insert your card, the device creates a copy of the data on the magnetic strip of your card. The card passes through the device and enters the machine, so everything will appear to be functioning normally---but your card data has just been copied.
The second part of the device is a camera. A small camera is placed somewhere it can see the keypad---perhaps at the top of an ATM's screen, just above the number pad, or to the side of the pad. The camera is pointed at the keypad and it captures you entering your PIN. The terminal continues to function normally, but the attackers just copied your card's magnetic strip and stole your PIN.
The attackers can use this data to program a bogus card with the magnetic strip data and use it in other ATMs, entering your PIN and withdrawing money from your bank accounts.
All that said, skimmers are also becoming more and more sophisticated. Instead of a device fitted over a card slot, a skimmer may be a small, unnoticeable device inserted into the card slot itself, often called a shimmer.
Instead of a camera pointed at the keypad, the attackers may also be using an overlay---a fake keyboard fitted over the real keypad. When you press a button on the fake keypad, it logs the button you pressed and presses the real button underneath. These are harder to detect. Unlike a camera, they're also guaranteed to capture your PIN.
Skimmers generally store the data they capture on the device itself. The criminals have to come back and retrieve the skimmer to get the data it's captured. However, more skimmers are now transmitting this data wirelessly over Bluetooth or even cellular data connections.
How to Spot Credit Card Skimmers
Here are some tricks for spotting card skimmers. You can't spot every skimmer, but you should definitely take a quick look around before withdrawing money.
- Jiggle the Card Reader: If the card reader moves around when you try to jiggle it with your hand, something probably isn't right. A real card reader should be attached to the terminal so well that it won't move around---a skimmer overlaid over the card reader may move around.
- Look at the Terminal: Take a quick look at the payment terminal itself. Does anything look a bit out of place? Perhaps the bottom panel is a different color from the rest of the machine because it's a fake piece of plastic placed over the real bottom panel and the keypad. Perhaps there's an odd-looking object that contains a camera.
- Examine the Keypad: Does the keypad look a bit too thick, or different from how it usually looks if you've used the machine before? It may be an overlay over the real keypad.
- Check for Cameras: Consider where an attacker might hide a camera---somewhere above the screen or keypad, or even in the brochure holder on the machine.
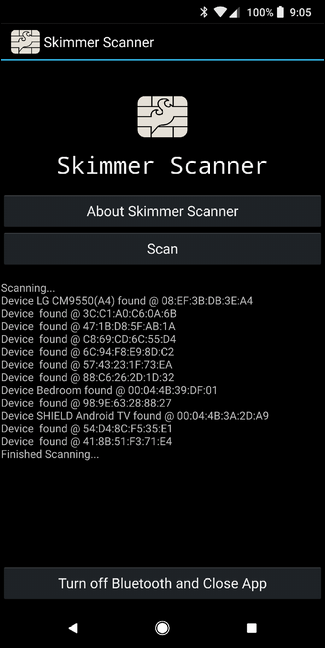
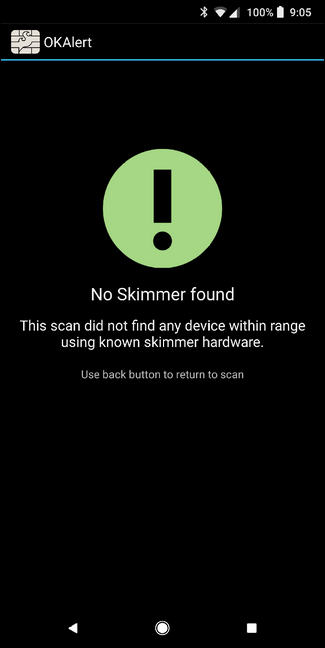
- Use Skimmer Scanner for Android: If you use an Android phone, there's a great new tool called Skimmer Scanner that will scan for nearby Bluetooth devices and detect the most common skimmers on the market. It's not foolproof, but this is an excellent tool for finding modern skimmers that transmit their data over Bluetooth.
If you find something seriously wrong---a card reader that moves, a hidden camera, or a keypad overlay---be sure to alert the bank or business in charge of the terminal. And of course, if something just doesn't seem right, go somewhere else.
Other Basic Security Precautions You Should Take
You can find common, cheap skimmers with tricks like attempting to jiggle the card reader. But here's what you should always do to protect yourself when using any payment terminal:
- Shield Your PIN With Your Hand: When you type your PIN into a terminal, shield the PIN pad with your hand. Yes, this won't protect you against the most sophisticated skimmers that use keypad overlays, but you're much more likely to run into a skimmer that uses a camera---they're much cheaper for criminals to purchase. This is the number one tip you can use to protect yourself.
- Monitor Your Bank Account Transactions: You should regularly check your bank accounts and credit card accounts online. Check for suspicious transactions and notify your bank as quickly as possible. You want to catch these problems as soon as possible---don't wait until your bank mails you a printed statement a month after money has been withdrawn from your account by a criminal. Tools like Mint.com---or an alert system your bank might offer---can also help here, notifying you when unusual transactions take place.
- Use Contactless Payment Systems: Where applicable, you can also help protect yourself by using contactless payment tools like Android Pay or Apple Pay. These are both inherently secure and completely bypass any sort of swipe system, so your card (and card data) never actually make it near the terminal. Unfortunately, most ATMs still don't accept contactless methods for withdrawals, but at least this is becoming more and more common at gas pumps.
The Industry Is Working on Solutions...Slowly
Just like the skimmer industry is constantly trying to find new ways to steal your info, the credit card industry is moving forward with new technology to keep your data safe. Most companies have recently switched to EMV chips, which make stealing your card data almost impossible since these are significantly harder to replicate.
The problem is that while most card companies and banks have been fairly quick to adopt this new tech on their cards, many card readers---payment terminals, ATMs, etc.---continue to use the traditional swipe method. As long as these sorts of systems are still in place, skimmers will always be a risk. To this day, I can't say I've seen a single ATM or gas pump terminal that utilizes the chip system, both of which have the highest probability of having a skimmer attached. Hopefully we'll start to see the chip system become more prolific at payment terminals as we transition into 2018.
But until then, you can use the steps found in this piece to protect yourself as much as possible. Like I said, it's not foolproof, but doing what you can will help protect your data and your finances is never a bad idea.
To learn more about this terrifying topic---or just to see photos of all the skimming hardware involved---check out Brian Krebs' All About Skimmers series over at Krebs on Security. It's a bit dated at this point, with many of the articles dating back to 2010, but it's all still very relevant to today's attacks and worth reading up on if you're interested.
Image Credit: Aaron Poffenberger on Flickr, nick v on Flickr