Quick Links
Windows' BitLocker encryption defaults to 128-bit AES encryption, but you can choose to use 256-bit AES encryption instead. Using a 256-bit AES key could potentially offer more security against future attempts to access your files.
Is this really more secure? Well, that's a matter of some debate. You might naively assume that 256-bit encryption offers more security, but it isn't that clear.
Is 256-bit AES Encryption More Secure?
Now here's a complicated topic. The common wisdom is that AES 128 and AES 256 actually offer about the same security. It would take so long to brute-force 128-bit AES encryption that 256-bit AES encryption doesn't really offer a meaningful amount of additional security. For example, if it would take a quadrillion years to brute-force 128-bit AES, does it really matter that it might take even longer to brute-force 256-bit AES? For all realistic purposes, they're equally secure.
But it's not quite all that simple. The NSA requires 128-bit keys for data marked SECRET, while it requires 256-bit keys for data marked TOP SECRET. The NSA clearly considers 256-bit AES encryption more secure. Does a secretive government agency tasked with breaking encryption know something we don't know, or is this just a case of silly government bureaucracy?
We aren't qualified to give the final word on this. Agile Bits has a great in-depth look at the subject in their blog post about why they moved the 1Password password manager from 128-bit AES to 256-bit AES. The NSA apparently considers 256-bit AES encryption protection against future quantum computing technologies that could break encryption much more quickly.
Select 256-bit AES Encryption for BitLocker
Let's assume you've decided you'd rather use 256-bit AES, or maybe you're an NSA employee with documents marked TOP SECRET and you have to do this. Bear in mind that 256-bit AES will be slower than 128-bit AES, although this performance difference is becoming less noticeable with faster computer hardware.
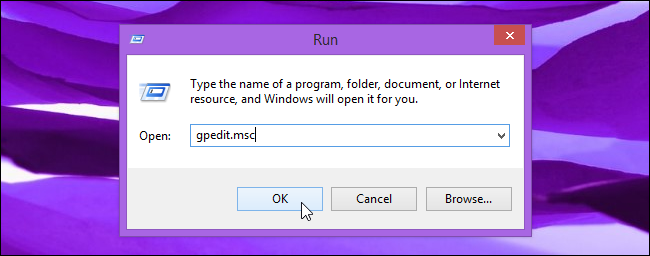
This setting is buried in group policy, which you can adjust on your own computer if your computer isn't part of a domain. Press Windows Key + R to open the Run dialog, type gpedit.msc into it, and press Enter to open the Local Group Policy Editor.
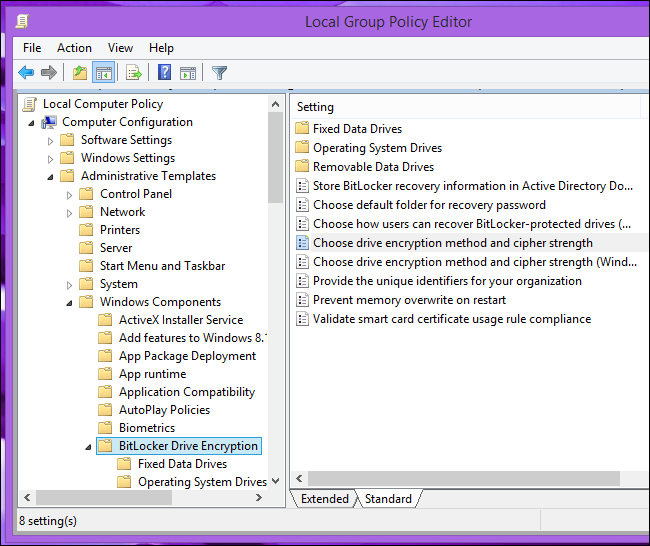
Navigate to Computer Configuration\Administrative Templates\Windows Components\BitLocker Drive Encryption. Double-click the "Choose drive encryption method and cipher strength" setting.
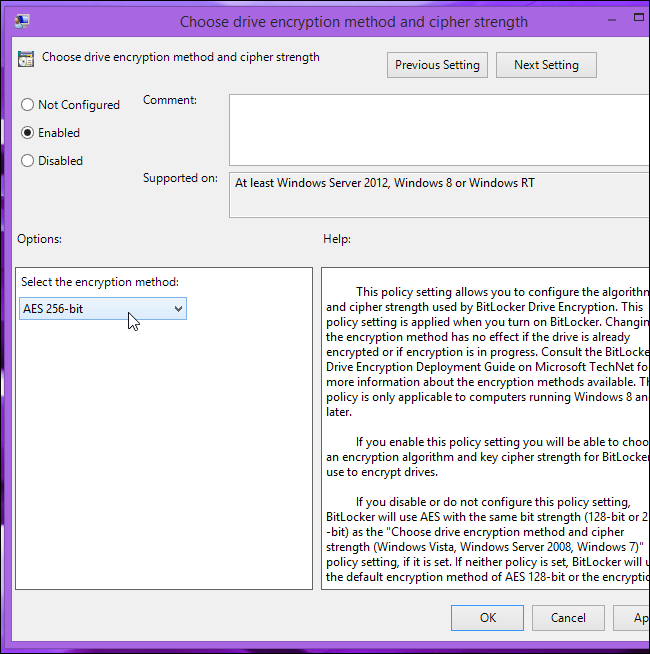
Select Enabled, click the drop-down box, and select AES 256-bit. Click OK to save your change.
BitLocker will now use 256-bit AES encryption when creating new volumes. This setting only applies to new volumes you enable BitLocker on. Any existing BitLocker volumes will continue to use 128-bit AES.
Convert 128-bit AES Volumes to 256-bit AES Encryption
BitLocker doesn't provide a way to convert existing BitLocker volumes to a different encryption method. You can do this yourself by decrypting the drive and then re-encrypting it with BitLocker. BitLocker will use 256-bit AES encryption when setting it up.
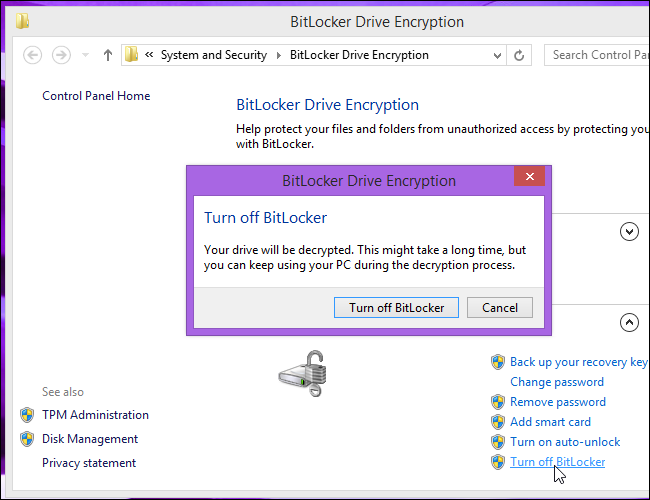
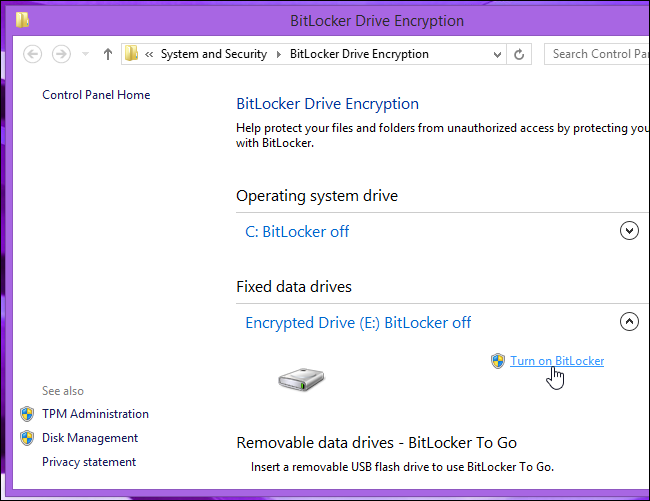
To do this, right-click an encrypted drive and select Manage BitLocker or navigate to the BitLocker pane in the Control Panel. Click the Turn off BitLocker link under an encrypted volume.
Allow Windows to decrypt the drive. When it's done, re-enable BitLocker for the volume by right-clicking it and selecting Turn on BitLocker or clicking Turn on BitLocker in the Control Panel window. Go through the normal BitLocker setup process.
Check Your BitLocker Volume's Encryption Method
You'll need a special command to see whether a drive is using 128-bit AES or 256-bit AES encryption.
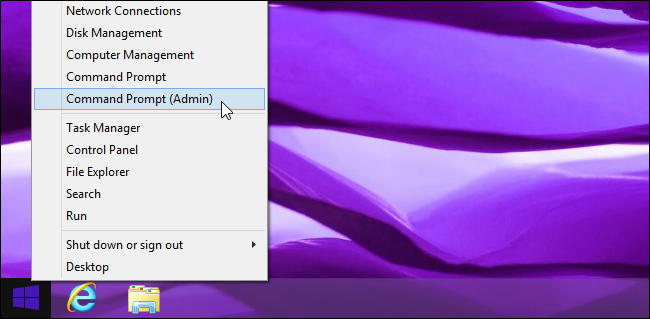
First, open a Command Prompt window as Administrator. On Windows 8.1 or 8, right-click in the bottom-left corner of your screen or press Windows Key + X and select Command Prompt (Admin). On Windows 7, open the Start menu, search for Command Prompt, right-click the Command Prompt shortcut, and select Run as Administrator.
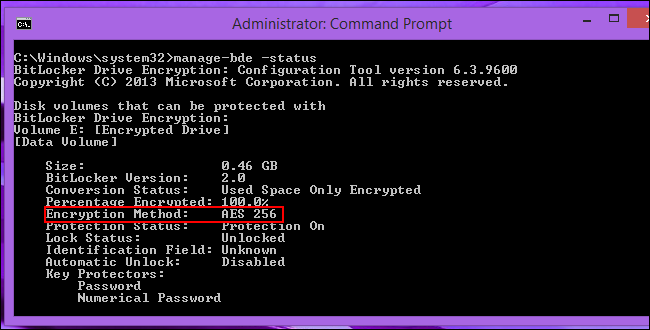
Type the following command into the Command Prompt window and press Enter:
manage-bde -status
You'll see information about each encrypted BitLocker drive on your computer, including its encryption method. Look for "AES 128" or "AES 256" to the right of "Encryption Method," under the drive.
Drives you set up will continue using either AES 128 or AES 256 encryption afterward, no matter the group policy setting. The setting only affects the encryption method Windows uses when setting up new BitLocker volumes.
Image Credit: Michelangelo Carrieri on Flickr