Quick Links
If you're practicing lax password management and hygiene, it's only a matter of time until one of the increasingly numerous large-scale security breaches burns you. Stop being thankful you dodged the past security breach bullets and armor yourself against the future ones. Read on as we show you how to audit your passwords and protect yourself.
What's the Big Deal and Why Does this Matter?
In October of this year, Adobe revealed that there had been a major security breach that affected 3 million users of Adobe.com and Adobe software. Then they revised the number to 38 million. Then, even more shockingly, when the database from the hack was leaked, security researchers that analyzed the database came back and said it was more like 150 million compromised user accounts. This degree of user exposure puts the Adobe breach in the running as one of the worst security breaches in history.
Adobe is hardly alone on this front, however; we simply opened with their breach because it's painfully recent. In the last few years alone there have been dozens of massive security breaches where user information, including passwords, have been compromised.
LinkedIn was hit in 2012 (6.46 million user records compromised). That same year, eHarmony was hit (1.5 million user records) as was Last.fm (6.5 million user records) and Yahoo! (450,000 user records). The Sony Playstation Network was hit in 2011 (101 million user records compromised). Gawker Media (the parent company of sites like Gizmodo and Lifehacker) was hit in 2010 (1.3 million user records compromised). And those are just examples of large breaches that made the news!
The Privacy Rights Clearinghouse maintains a database of security breaches from 2005 to the present. Their database includes a wide range of breach types: compromised credit cards, stolen social security numbers, stolen passwords, and medical records. The database, as of the publication of this article, is composed of 4,033 breaches containing 617,937,023 user records. Not every one of those hundreds of millions of breaches involved user passwords, but millions upon millions of them did.
So why does it matter? Aside from the obvious and immediate security implications of a breach, the breaches create collateral damage. The hackers can immediately start testing the logins and passwords they harvest at other web sites.
Most people are lazy with their passwords, and there's a good chance that if somebody used bob@somewebemail.com with the password bob1979, that the same login/password pair will work at other web sites. If those other websites are higher profile (like banking sites or if the password he used at Adobe actually unlocks his email inbox), then there's an issue. Once someone has access to your email inbox, they can start resetting password on other services and gaining access to them too.
The only way to stop this kind of chain reaction from causing even more security problems within the network of web sites and services you use is to follow two cardinal rules of good password hygiene:
- Your email password should be long, strong, and completely unique among all your logins.
- Every login gets a long, strong, and unique password. No password reuse. Ever.
Those two rules are the takeaway from every security guide we've ever shared with you, including our emergency it-has-hit-the-fan guide How to Recover After Your Email Password Is Compromised.
Now at this point, you're probably squirming a little because, frankly, hardly anyone has perfectly airtight password practices and security. You're not alone if your password hygiene is lacking. In fact, it's time for a confession.
I've written dozens of security articles, posts about security breaches, and other password-related posts over the years I've been at How-To Geek. Despite being precisely the kind of informed person who should know better, despite using a password manager and generating secure passwords for every new website and service, when I ran my email through the list of compromised Adobe logins and matched it against the compromised password, I still found out that I'd gotten burned.
I made that Adobe account a long time ago when I was significantly more lax with my password hygiene, and the password I used was common across dozens of websites and services that I'd signed up with before I got super serious about making good passwords.
All of that could have been prevented if I'd fully practiced what I preached and not just created unique and strong passwords but also audited my old passwords to ensure this situation never happened in the first place. Whether you've never even attempted to be consistent and secure with your password practices or you just need to check them over to put yourself at ease, a thorough password audit is the path to password security and peace of mind. Read on as we show you how.
Preparing for Your Lastpass Security Challenge
You could manually audit your passwords, but that would be enormously tedious and you wouldn't gain any of the benefits of using a good universal password manager. Instead of manually auditing everything, we're going to take the easy and largely automated route: we're going to audit our passwords by taking the LastPass Security Challenge.
This guide won't cover setting up LastPass, so if you don't already have a LastPass system up and running, we strongly encourage you to set one up. Check out The HTG Guide to Getting Started with LastPass to get started. Although LastPass has updated since we wrote the guide (the interface is much prettier and better streamlined now), you can still follow the steps with ease. If you're setting up LastPass for the first time, make sure to import all your stored passwords from your browsers, as our goal is to audit every single password you're using.
Enter every login and password into LastPass: Whether you're brand new to LastPass or you haven't fully been using it for every login, now is the time to make sure you've entered every login into the LastPass system. We're going to echo the advice we gave in our email recovery guide for combing your email inbox for reminders:
Search your email for registration reminders. It won’t be hard to remember your frequently used logins like Facebook and your bank but there are likely dozens of outlaying services that you may not even remember that you use your email to log into. Use keyword searches like “welcome to”, “reset”, “recovery”, “verify”, “password”, “username”, “login”, “account” and combinations there of like “reset password” or “verify account”. Again, we know this is a hassle, but once you’ve done this with a password manager at your side, you have a master list of all your account and you’ll never have to do this keyword hunt again.
Enable two-factor authentication on your LastPass account: This step is not strictly necessary to perform the security audit, but while we have your attention we're going to do everything we can to encourage you, while you're mucking around in your LastPass account, to turn on two-factor authentication to further secure your LastPass vault. (Not only does it increase your account security, you'll get a boost in your security audit score, too!)
Taking the LastPass Security Challenge
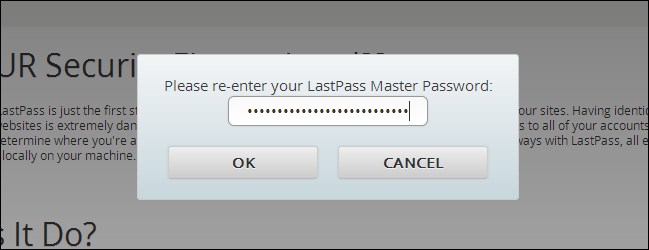
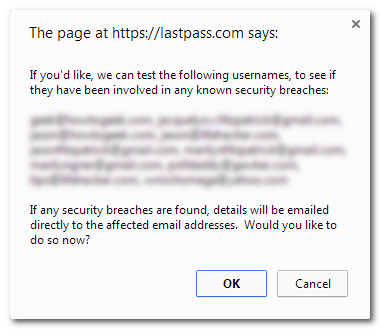
Now that you've imported all your passwords, it's time to brace yourself for the shame of not being in the 1% of hardcore password security ninjas. Visit the LastPass Security Challenge page and press "Start the Challenge" at the bottom of the page. You'll be prompted to enter your master password, as seen in the screenshot above, and then LastPass will offer to check if any of the email addresses contained in your vault were part of any breaches it has tracked. There's no good reason to not take advantage of this:
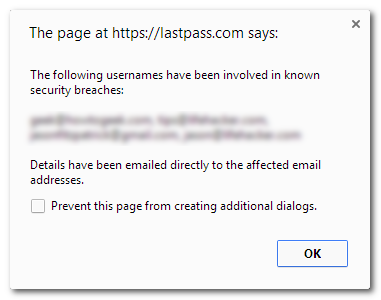
If you're lucky, it returns a negative. If you're lucky, you get a pop-up like this asking if you want more information about the breaches your email was involved in:
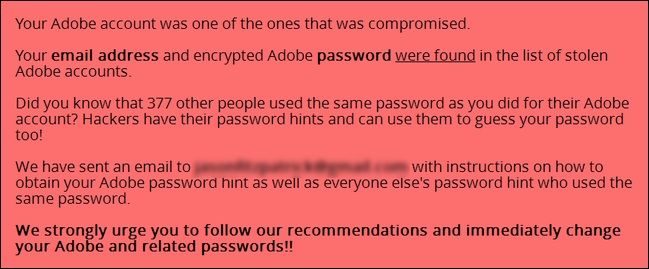
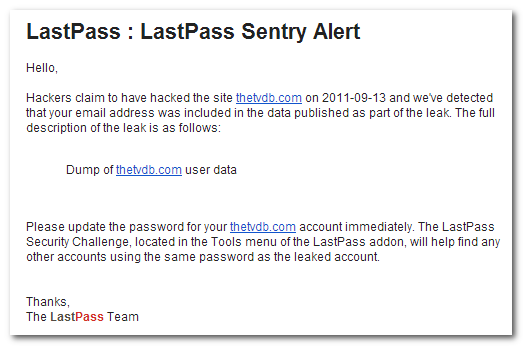
LastPass will issue a single security alert for each instance. If you've had your email address for a long time, be prepared to be shocked at how many password breaches it has been tangled up in. Here's an example of a password breach notice:
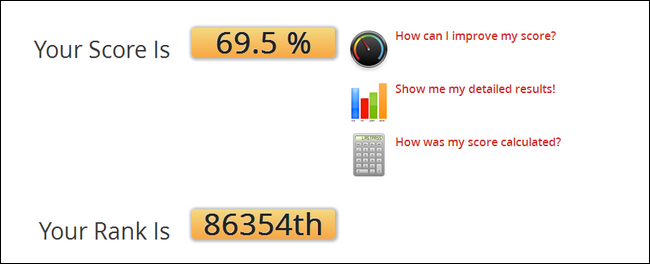
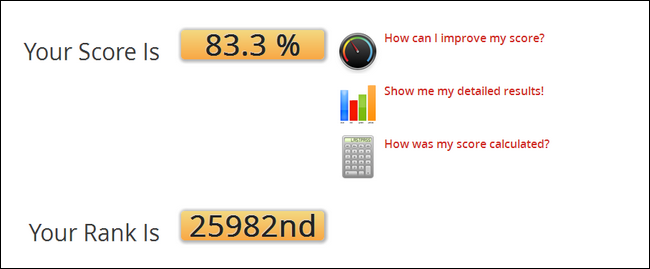
After the pop-ups, you'll be dumped into the main panel of the LastPass Security Challenge. Remember earlier in the guide when I talked about how I currently practice good password hygiene but that I'd never gotten around to properly updating a lot of older web sites and service? It really shows in the score I received. Ouch:
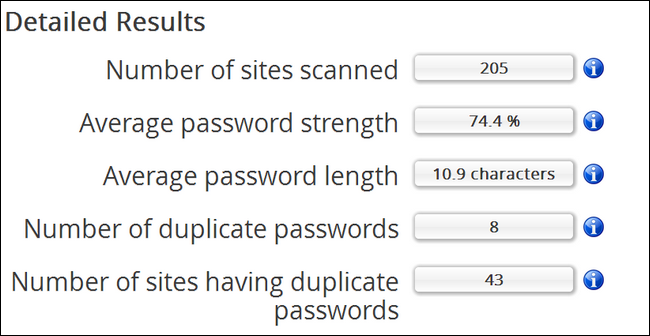
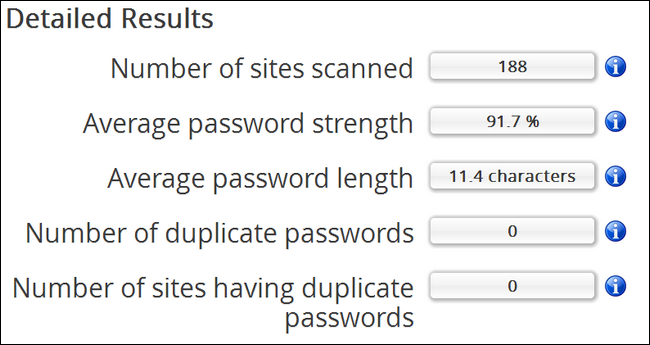
That's my score with years worth of random passwords mixed in. Don't be too shocked if your score is even lower if you've been using the same handful of weak passwords over and over again. Now that we have our score (however awesome or shameful it might be), it's time to dig into the data. You can use the quick links beside your score percentage or just start scrolling. First stop, let's check out the detailed results. Consider this a 10,000 foot overview of the state of your passwords:
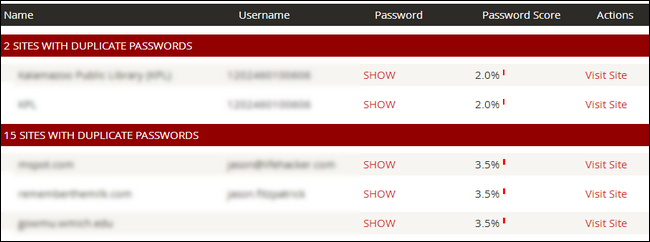
While you should pay attention to all the stats here, the really important ones are "Average password strength", how weak or strong your average password is and, even more important, "Number of duplicate passwords" and "Number of sites having duplicate passwords". In the cause of my audit, there were 8 dupes across 43 sites. Clearly I had been pretty lazy reusing the same low-grade password on more than a few sites.
Next stop, the Analyzed Sites section. Here you'll find a very concrete break down of all your logins and passwords organized by duplicate password use (if you had duplicates), unique passwords, and finally, logins without a password stored in LastPass. While you're looking over the list, marvel at the contrast between password strengths. In my case, one of my financial logins was given a 45% Password Score while my daughter's Minecraft login was given a perfect 100% score. Again, ouch.
Fixing Your Terrible Security Challenge Score
There are two very useful links built right into the audit listings. If you click "SHOW" it will show you the password for that site and if you click "Visit Site" you can jump right to the web site so you can change the password. Not only should every duplicate password be changed, but any password that was attached to an account that was breached (such as Adobe.com or LinkedIn) should be retired permanently.
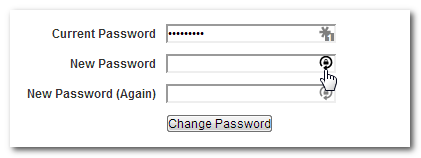
Depending on how many or few passwords you have (and how diligent you've been about good password practices), this step of the process might take you ten minutes or the whole afternoon. Although the process of changing your passwords will vary based on the layout of the site you're updating, here are some general guidelines to follow (we're using our password update at Remember the Milk as an example): Visit the password change page. Typically you'll need to input your current password and then generate a new password.
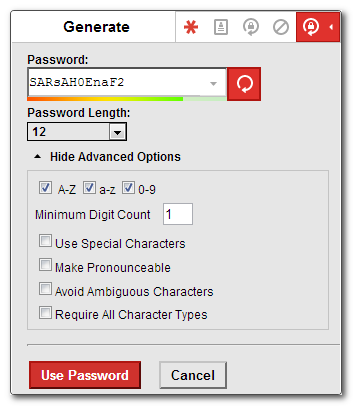
Do so by clicking on the lock-with-circular-arrow logo. LastPass inserts into the new password slot (as seen in the screenshot above). Look over your new password and make adjustments if you desire (such as lengthening it or adding in special characters):
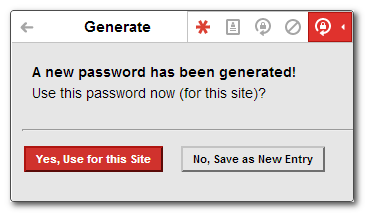
Click "Use Password" and then confirm you want to update the entry you're editing:
Make sure to confirm the change with the website too. Repeat the process for every duplicate and weak password in your LastPass vault.
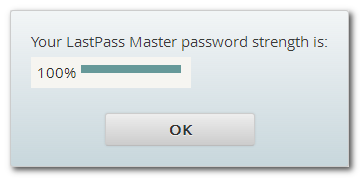
Finally, the last thing you need to audit is your LastPass Master Password. Do so by clicking the link at the bottom of the Challenge screen labeled "Test the strength of my LastPass Master Password". If you don't see this:
You need to reset your LastPass Master Password and increase the strength until you receive a nice, positive, 100% strength confirmation.
Surveying the Results and Further Enhancing Your LastPass Security
After you've slogged through the list of duplicate passwords, deleted old entries, and otherwise tidied up and secured your login/password list, it's time to run the audit again. Now, for emphasis, the score you see below was brought up solely by improving password security. (If you enable additional security features, like multi-factor authentication, you'll receive a boost of around 10%).
Not bad! After eliminating every duplicate password and bringing all the existing passwords up to 90% strength or better, it really improved our score. If you're curious why it didn't jump to 100%, there are a few factors at play, the most prominent of which is that some passwords can never be brought up to snuff by LastPass standards because of silly policies in place by the site administrators. For example, my local library's login password is a four digit pin (which scores a 4% on the LastPass security scale). Most people will have some sort of outliers like that in their list and that will drag their score down.
In such cases, it's important to not get discouraged, and to use your detailed breakdown as a metric:
In the password updating process I pruned 17 duplicate/expired sites, created a unique password for every site and service, and brought the number of sites with duplicate passwords down from 43 to 0 in the process.
It only took about an hour of seriously focused time (12.4% of which was spent cursing web site designers who put password update links in obscure places), and all it took to get me motivated was a password breach of catastrophic proportions! I'm making a note here, huge success.
Now that you've audited your passwords and you're pumped about having a stable of unique passwords, let's take advantage of that forward momentum. Hit up our guide to making LastPass even more secure by increasing password iterations, restricting logins by country, and more. Between running the audit we outlined here, following our LastPass security guide, and turning on two-factor algorithms, you'll have a bulletproof password management system you can be proud of.