Just because an email shows up in your inbox labeled Bill.Smith@somehost.com, doesn't mean that Bill actually had anything to do with it. Read on as we explore how to dig in and see where a suspicious email actually came from.
Today’s Question & Answer session comes to us courtesy of SuperUser—a subdivision of Stack Exchange, a community-drive grouping of Q&A web sites.
The Question
SuperUser reader Sirwan wants to know how to figure out where emails actually originate from:
How can I know where an Email really came from?
Is there any way to find it out?
I have heard about email headers, but I don't know where can I see email headers for example in Gmail.
Let's take a look at these email headers.
The Answers
SuperUser contributor Tomas offers a very detailed and insightful response:
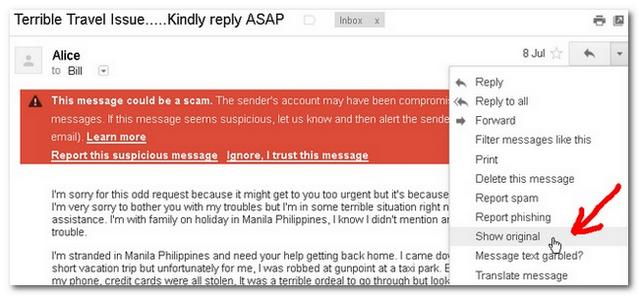
See an example of scam that has been sent to me, pretending it is from my friend, claiming she has been robbed and asking me for financial aid. I have changed the names — suppose that I am Bill, the scammer has send an email to
bill@domain.com, pretending he is
alice@yahoo.com. Note that Bill has forward to
bill@gmail.com.
First, in Gmail, use
show original:
Then, the full email and its headers will open:
Delivered-To: bill@gmail.com
Received: by 10.64.21.33 with SMTP id s1csp177937iee;
Mon, 8 Jul 2013 04:11:00 -0700 (PDT)
X-Received: by 10.14.47.73 with SMTP id s49mr24756966eeb.71.1373281860071;
Mon, 08 Jul 2013 04:11:00 -0700 (PDT)
Return-Path: <SRS0=Znlt=QW=yahoo.com=alice@domain.com>
Received: from maxipes.logix.cz (maxipes.logix.cz. [2a01:348:0:6:5d59:50c3:0:b0b1])
by mx.google.com with ESMTPS id j47si6975462eeg.108.2013.07.08.04.10.59
for <bill@gmail.com>
(version=TLSv1 cipher=RC4-SHA bits=128/128);
Mon, 08 Jul 2013 04:11:00 -0700 (PDT)
Received-SPF: neutral (google.com: 2a01:348:0:6:5d59:50c3:0:b0b1 is neither permitted nor denied by best guess record for domain of SRS0=Znlt=QW=yahoo.com=alice@domain.com) client-ip=2a01:348:0:6:5d59:50c3:0:b0b1;
Authentication-Results: mx.google.com;
spf=neutral (google.com: 2a01:348:0:6:5d59:50c3:0:b0b1 is neither permitted nor denied by best guess record for domain of SRS0=Znlt=QW=yahoo.com=alice@domain.com) smtp.mail=SRS0=Znlt=QW=yahoo.com=alice@domain.com
Received: by maxipes.logix.cz (Postfix, from userid 604)
id C923E5D3A45; Mon, 8 Jul 2013 23:10:50 +1200 (NZST)
X-Original-To: bill@domain.com
X-Greylist: delayed 00:06:34 by SQLgrey-1.8.0-rc1
Received: from elasmtp-curtail.atl.sa.earthlink.net (elasmtp-curtail.atl.sa.earthlink.net [209.86.89.64])
by maxipes.logix.cz (Postfix) with ESMTP id B43175D3A44
for <bill@domain.com>; Mon, 8 Jul 2013 23:10:48 +1200 (NZST)
Received: from [168.62.170.129] (helo=laurence39)
by elasmtp-curtail.atl.sa.earthlink.net with esmtpa (Exim 4.67)
(envelope-from <alice@yahoo.com>)
id 1Uw98w-0006KI-6y
for bill@domain.com; Mon, 08 Jul 2013 06:58:06 -0400
From: "Alice" <alice@yahoo.com>
Subject: Terrible Travel Issue.....Kindly reply ASAP
To: bill@domain.com
Content-Type: multipart/alternative; boundary="jtkoS2PA6LIOS7nZ3bDeIHwhuXF=_9jxn70"
MIME-Version: 1.0
Reply-To: alice@yahoo.com
Date: Mon, 8 Jul 2013 10:58:06 +0000
Message-ID: <E1Uw98w-0006KI-6y@elasmtp-curtail.atl.sa.earthlink.net>
X-ELNK-Trace: 52111ec6c5e88d9189cb21dbd10cbf767e972de0d01da940e632614284761929eac30959a519613a350badd9bab72f9c350badd9bab72f9c350badd9bab72f9c
X-Originating-IP: 168.62.170.129
[... I have cut the email body ...]The headers are to be read chronologically from bottom to top — oldest are at the bottom. Every new server on the way will add its own message — starting with
Received. For example:Received: from maxipes.logix.cz (maxipes.logix.cz. [2a01:348:0:6:5d59:50c3:0:b0b1])
by mx.google.com with ESMTPS id j47si6975462eeg.108.2013.07.08.04.10.59
for <bill@gmail.com>
(version=TLSv1 cipher=RC4-SHA bits=128/128);
Mon, 08 Jul 2013 04:11:00 -0700 (PDT)This says that
mx.google.comhas received the mail frommaxipes.logix.czatMon, 08 Jul 2013 04:11:00 -0700 (PDT).Now, to find the real sender of your email, your goal is to find the last trusted gateway — last when reading the headers from top, i.e. first in the chronological order. Let's start by finding the Bill's mail server. For this, you query MX record for the domain. You can use some online tools, or on Linux you can query it on command line (note the real domain name was changed to
domain.com):~$ host -t MX domain.com
domain.com MX 10 broucek.logix.cz
domain.com MX 5 maxipes.logix.czSo you see the mail server for domain.com is
maxipes.logix.czorbroucek.logix.cz. Hence, the last (first chronologically) trusted "hop" — or last trusted "Received record" or whatever you call it — is this one:Received: from elasmtp-curtail.atl.sa.earthlink.net (elasmtp-curtail.atl.sa.earthlink.net [209.86.89.64])
by maxipes.logix.cz (Postfix) with ESMTP id B43175D3A44
for <bill@domain.com>; Mon, 8 Jul 2013 23:10:48 +1200 (NZST)You can trust this because this was recorded by Bill's mail server for
domain.com. This server got it from209.86.89.64. This could be, and very often is, the real sender of the email — in this case the scammer! You can check this IP on a blacklist. — See, he is listed in 3 blacklists! There is yet another record below it:Received: from [168.62.170.129] (helo=laurence39)
by elasmtp-curtail.atl.sa.earthlink.net with esmtpa (Exim 4.67)
(envelope-from <alice@yahoo.com>)
id 1Uw98w-0006KI-6y
for bill@domain.com; Mon, 08 Jul 2013 06:58:06 -0400but you cannot actually trust this, because that could just be added by the scammer to wipe out his traces and/or lay a false trail. Of course there is still the possibility that the server
209.86.89.64is innocent and only acted as a relay for the real attacker at168.62.170.129, but then the relay is often considered to be guilty and is very often blacklisted. In this case,168.62.170.129is clean so we can be almost sure the attack was done from209.86.89.64.And of course, as we know that Alice uses Yahoo! and
elasmtp-curtail.atl.sa.earthlink.netisn't on the Yahoo! network (you may want to re-check its IP Whois information), we may safely conclude that this email was not from Alice, and that we should not send her any money to her claimed vacation in the Philippines.
Two other contributors, Ex Umbris and Vijay, recommended, respectively, the following services for assisting in decoding of email headers: SpamCop and Google's Header Analysis tool.
Have something to add to the explanation? Sound off in the the comments. Want to read more answers from other tech-savvy Stack Exchange users? Check out the full discussion thread here.