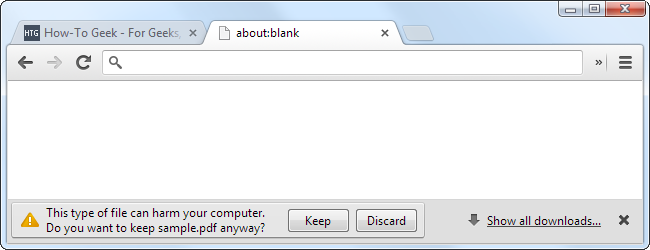
Chrome often warns you "This type of file can harm your computer" when you try to download something, even if it's a PDF file. But how can a PDF file be so dangerous -- isn't a PDF just a document with text and images?
PDF readers like Adobe Reader have been a source of many security vulnerabilities over the years. This is because a PDF file isn't just a document -- it can contain scripts, embedded media, and other questionable things.
PDFs Aren't Just Documents
The PDF file format is actually very complicated. It can contain many things, not just text and images, as you might expect. PDF supports many features that it arguably shouldn't, which have opened many security holes in the past.
- JavaScript: PDFs can contain JavaScript code, which is the same language used by web pages in your browser. PDFs can be dynamic and run code that modifies the PDF's contents or manipulates the PDF viewer's features. Historically, many vulnerabilities have been caused by PDFs using JavaScript code to exploit Adobe Reader. Adobe Reader's JavaScript implementation even contains Adobe-specific JavaScript APIs, some of which were insecure and have been exploited.
- Embedded Flash: PDFs can contain embedded Flash content. Any vulnerability in Flash could also be used to compromise Adobe Reader. Until April 10, 2012, Adobe Reader contained its own bundled Flash Player. Security flaws fixed in the main Flash Player may not have been fixed in Adobe Reader's bundled Flash Player until weeks later, leaving security holes wide open for exploitation. Adobe Reader now uses the Flash Player installed on your system rather than an internal player.
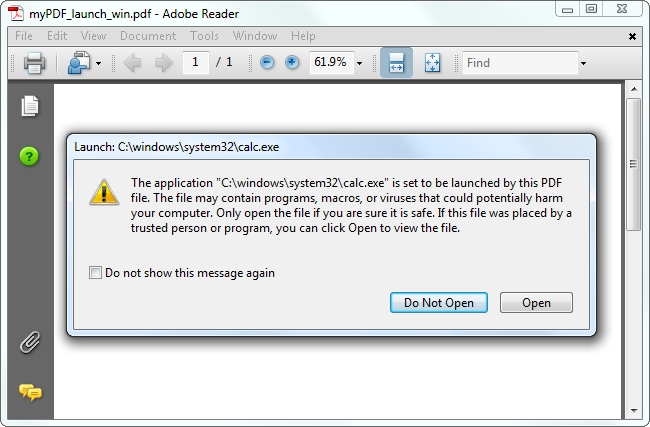
- Launch Actions: PDF files had the ability to launch any command after popping up a confirmation window. In older versions of Adobe Reader, a PDF file could attempt to launch a dangerous command as long as the user clicked OK. Adobe Reader now contains a blacklist that restricts PDF files from launching executable files.
- GoToE: PDF files can contain embedded PDF files, which can be encrypted. When a user loads the main PDF file, it could immediately load its embedded PDF file. This allows attackers to hide malicious PDF files inside other PDF files, fooling antivirus scanners by preventing them from examining the hidden PDF file.
- Embedded Media Controls: In addition to Flash, PDFs could historically contain Windows Media Player, RealPlayer, and QuickTime media. This would allow a PDF to exploit vulnerabilities in these embeddable multimedia player controls.
There are many more features in the PDF file format that increase its attack surface, including the ability to embed any file inside a PDF and use 3D graphics.
PDF Security Has Improved
You should now hopefully understand why Adobe Reader and PDF files have been a source of so many security vulnerabilities. PDF files may look like simple documents, but don't be deceived -- there could be much more going on under the surface.
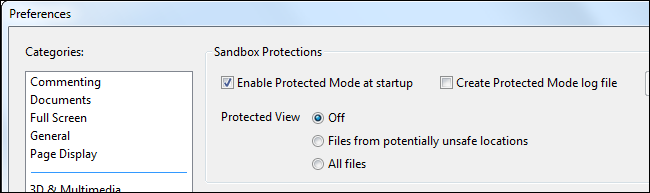
The good news is that PDF security has improved. Adobe added a sandbox named "Protected Mode" in Adobe Reader X. This runs the PDF in a limited, locked-down environment where it only has access to certain parts of your computer, not your entire operating system. It's similar to how Chrome's sandboxing isolates web page processes from the rest of your computer. This creates much more work for attackers. They don't just have to find a security vulnerability in the PDF viewer -- they have to find a security vulnerability and then use a second security vulnerability in the sandbox to escape the sandbox and do damage to the rest of your computer. This isn't impossible to do, but much fewer security vulnerabilities have been discovered and exploited in Adobe Reader since the sandbox was introduced.
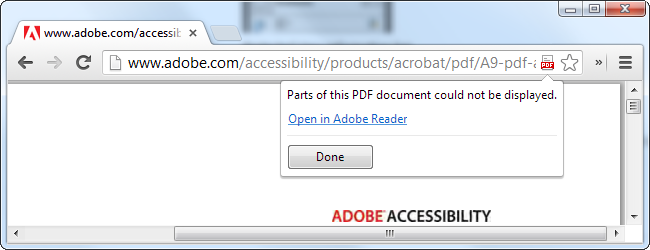
You can also use third-party PDF readers, which generally don't support every PDF feature. This can be a blessing in a world where PDF contains so many questionable features. Chrome has an integrated PDF viewer that uses its sandbox, while Firefox has its own integrated PDF viewer written entirely in JavaScript, so it runs in the same security environment that a normal web page does.
While we can wonder if PDFs should really be able to do all of these things, PDF security has at least improved. That's more than we can say for the Java plug-in, which is terrible and is currently the primary attack vector on the web. Chrome warns you before running Java content if you have the Java plug-in installed, too.