Quick Links
Some people believe Tor is a completely anonymous, private, and secure way to access the Internet without anyone being able to monitor your browsing and trace it back to you -- but is it? It's not quite that simple.
Tor isn't the perfect anonymity and privacy solution. It has several important limitations and risks, which you should be aware of if you're going to use it.
Exit Nodes Can Be Sniffed
Read our discussion of how Tor works for a more detailed look at how Tor provides its anonymity. In summary, when you use Tor, your Internet traffic is routed through Tor's network and goes through several randomly selected relays before exiting the Tor network. Tor is designed so that it is theoretically impossible to know which computer actually requested the traffic. Your computer may have initiated the connection or it may just be acting as a relay, relaying that encrypted traffic to another Tor node.
However, most Tor traffic must eventually emerge from the Tor network. For example, let's say you are connecting to Google through Tor -- your traffic is passed through several Tor relays, but it must eventually emerge from the Tor network and connect to Google's servers. The last Tor node, where your traffic leaves the Tor network and enters the open Internet, can be monitored. This node where traffic exits the Tor network is known as an "exit node" or "exit relay."
If you're accessing an encrypted (HTTPS) website such as your Gmail account, this is okay -- although the exit node can see that you're connecting to Gmail. if you're accessing an unencrypted website, the exit node can potentially monitor your Internet activity, keeping track of the web pages you visit, searches you perform, and messages you send.
People must consent to run exit nodes, as running exit nodes puts them at more of a legal risk than just running a relay node that passes traffic. It's likely that governments run some exit nodes and monitor the traffic that leaves them, using what they learn to investigate criminals or, in repressive countries, punish political activists.
This isn't just a theoretical risk. In 2007, a security researcher intercepted passwords and email messages for a hundred email accounts by running a Tor exit node. The users in question made the mistake of not using encryption on their email system, believing that Tor would somehow protect them with its internal encryption. But that's not how Tor works.
Lesson: When using Tor, be sure to use encrypted (HTTPS) websites for anything sensitive. Bear in mind that your traffic could be monitored -- not just by governments, but by malicious people looking for private data.
JavaScript, Plug-ins, and Other Applications Can Leak Your IP
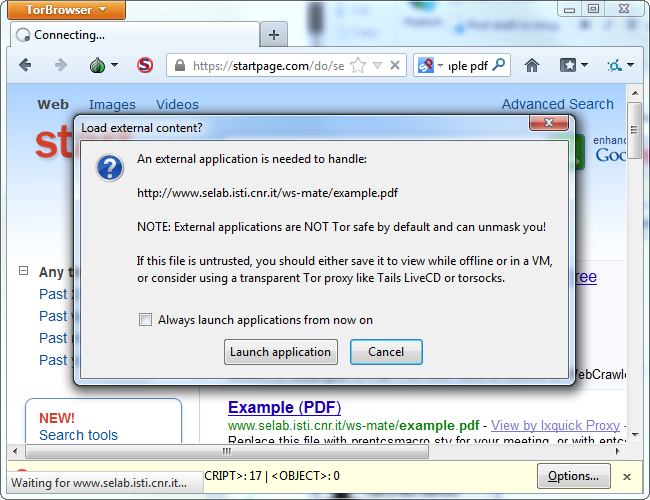
The Tor browser bundle, which we covered when we explained how to use Tor, comes preconfigured with secure settings. JavaScript is disabled, plug-ins can't run, and the browser will warn you if you attempt to download a file and open it on another application.
JavaScript isn't normally a security risk, but if you're trying to hide your IP, you don't want to use JavaScript. Your browser's JavaScript engine, plug-ins like Adobe Flash, and external applications like Adobe Reader or even a video player could all potentially "leak" your real IP address to a website that tries to acquire it.
The Tor browser bundle avoids all these problems with its default settings, but you could potentially disable these protections and use JavaScript or plug-ins in the Tor browser. Don't do this if you're serious about anonymity -- and if you aren't serious about anonymity, you shouldn't be using Tor in the first place.
This isn't just a theoretical risk, either. In 2011, a group of researchers acquired the IP addresses of 10,000 people who were using BitTorrent clients through Tor. Like many other types of applications, BitTorrent clients are insecure and capable of exposing your real IP address.
Lesson: Leave the Tor browser's secure settings in place. Don't try to use Tor with another browser -- stick with the Tor browser bundle, which has been preconfigured with the ideal settings. You shouldn't use other applications with the Tor network.
Running an Exit Node Puts You At Risk
If you're a big believer in online anonymity, you may be motivated to donate your bandwidth by running a Tor relay. This shouldn't be a legal problem -- a Tor relay just passes encrypted traffic back and forth inside the Tor network. Tor achieves anonymity through relays run by volunteers.
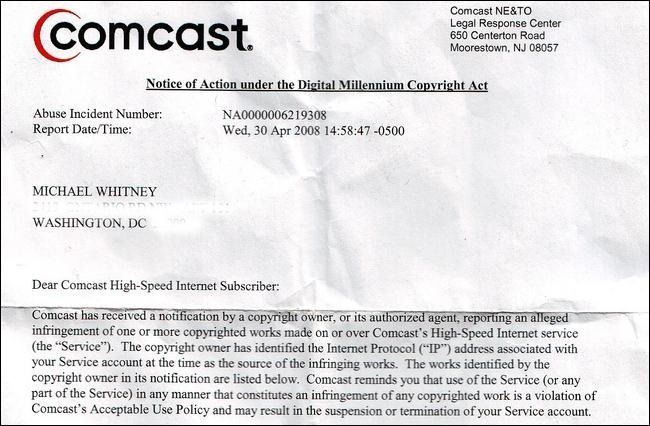
However, you should think twice before running an exit relay, which is a place where Tor traffic comes out of the anonymous network and connects to the open Internet. If criminals use Tor for illegal things and the traffic comes out of your exit relay, that traffic will be traceable to your IP address and you may get a knock on your door and your computer equipment confiscated. A man in Austria was raided and charged with distributing child pornography for running a Tor exit node. Running a Tor exit node allows other people to do bad things that can be traced back to you, just like operating an open Wi-Fi network -- but it's much, much, much more likely to actually get you into trouble. The consequences may not be a criminal penalty, however. You may just face a lawsuit for downloading copyrighted content or action under the Copyright Alert System in the USA.
The risks involved with running Tor exit nodes actually tie back into the first point. Because running a Tor exit node is so risky, few people do it. Governments could get away with running exit nodes, however -- and it's likely many do.
Lesson: Never run a Tor exit node -- seriously.
The Tor project has recommendations for running an exit node if you really want to. Their recommendations include running an exit node on a dedicated IP address in a commercial facility and using a Tor-friendly ISP. Don't try this at home! (Most people shouldn't even try this at work.)
Tor isn't a magic solution that grants you anonymity. It achieves anonymity by cleverly passing encrypted traffic through a network, but that traffic has to emerge somewhere -- which is a problem for both Tor's users and exit node operators. In addition, the software that runs on our computers wasn't designed to hide our IP addresses, which results in risks when doing anything beyond viewing plain HTML pages in the Tor browser.
Image Credit: Michael Whitney on Flickr, Andy Roberts on Flickr, The Tor Project, Inc.