In a perfect world, there would be no way for your computer to be infected via your browser. Browsers are supposed to run web pages in an untrusted sandbox, isolating them from the rest of your computer. Unfortunately, this doesn’t always happen.
Websites can use security holes in browsers or browser plugins to escape these sandboxes. Malicious websites will also try using social-engineering tactics to trick you.
Insecure Browser Plugins
Most people that are compromised through browsers are compromised through their browsers’ plugins. Oracle’s Java is the worst, most dangerous culprit. Apple and Facebook recently had internal computers compromised because they accessed websites containing malicious Java applets. Their Java plugins could have been completely up-to-date – it wouldn’t matter, because the latest versions of Java still contain unpatched security vulnerabilities.
To protect yourself, you should uninstall Java entirely. If you can’t because you need Java for a desktop application like Minecraft, you should at least disable the Java browser plugin to protect yourself.
Other browser plugins, particularly Adobe’s Flash player and PDF reader plugins, also regularly have to patch security vulnerabilities. Adobe has become better than Oracle at responding to these issues and patching their plugins, but it’s still common to hear about a new Flash vulnerability being exploited.
Plugins are juicy targets. Vulnerabilities in plugins can be exploited across all different browsers with the plugin across all different operating systems. A Flash plugin vulnerability could be used to exploit Chrome, Firefox, or Internet Explorer running on Windows, Linux, or Mac.
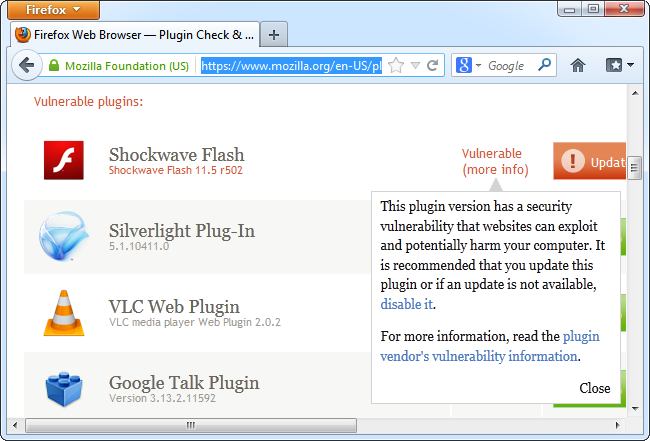
To protect yourself from plugin vulnerabilities, follow these steps:
- Use a website like Firefox’s plugin check to see if you have any out-of-date plugins. (This website was created by Mozilla, but it also works with Chrome and other browsers.)
- Update any out-of-date plugins immediately. Keep them updated by ensuring automatic updates are enabled for each plugin you have installed.
- Uninstall plugins you don’t use. If you don’t use the Java plugin, you shouldn’t have it installed. This helps reduce your “attack surface” – the amount of software your computer has available to be exploited.
- Consider using the click-to-play plugins feature in Chrome or Firefox, which prevents plugins from running except when you specifically request them.
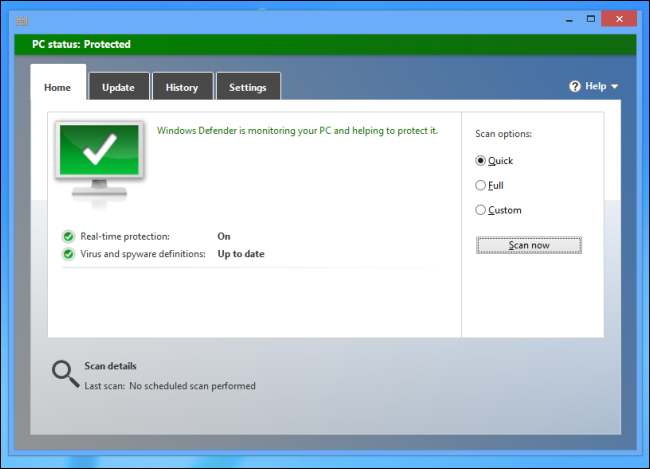
- Ensure you’re using an antivirus on your computer. This is the last line of defense against a “zero-day” vulnerability (a new, unpatched vulnerability) in a plugin that allows an attacker to install malicious software on your machine.
Browser Security Holes
Security vulnerabilities in web browsers themselves can also allow malicious websites to compromise your computer. Web browsers have largely cleaned up their act and security vulnerabilities in plugins are currently the main source of compromises.
However, you should keep your browser up-to-date anyway. If you’re using an old, unpatched version of Internet Explorer 6 and you visit a less-reputable website, the website could exploit security vulnerabilities in your browser to install malicious software without your permission.
Protecting yourself from browser security vulnerabilities is simple:
- Keep your web browser updated. All major browsers now check for updates automatically. Leave the auto-update feature enabled to stay protected. (Internet Explorer updates itself through Windows Update. If you use Internet Explorer, staying up-to-date on updates for Windows is extra important.)
- Ensure you’re running an antivirus on your computer. As with plugins, this is the last line of defense against a zero-day vulnerability in a browser that allows malware to get onto your computer.
Social-Engineering Tricks
Malicious web pages try to trick you into downloading and running malware. They often do this using “social engineering” – in other words, they try to compromise your system by convincing you to let them in under false pretenses, not by compromising your browser or plugins themselves.
This type of compromise isn’t just limited to your web browser – malicious email messages may also try to trick you into opening unsafe attachments or downloading unsafe files. However, many people are infected with everything from adware and obnoxious browser toolbars to viruses and Trojans via social-engineering tricks that take place in their browsers.
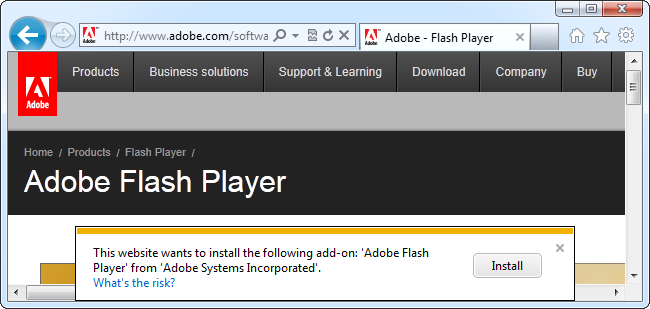
- ActiveX Controls: Internet Explorer uses ActiveX controls for its browser plugins. Any website can prompt you to download an ActiveX control. This can be legitimate – for example, you might need to download the Flash player ActiveX control the first time you play a Flash video online. However, ActiveX controls are just like any other software on your system and have permission to leave the web browser and access the rest of your system. A malicious website pushing a dangerous ActiveX control may say the control is necessary to access some content, but it may actually exist to infect your computer. When in doubt, don't agree to run an ActiveX control.
- Auto-Downloading Files: A malicious website may attempt to automatically download an EXE file or another type of dangerous file onto your computer in the hopes that you will run it. If you didn’t specifically request a download and don’t know what it is, don’t download a file that automatically pops up and asks you where to save it.
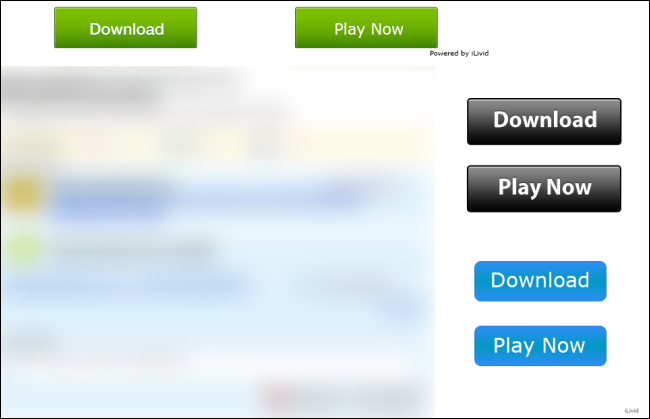
- Fake Download Links: On websites with bad ad networks – or websites where pirated content is found – you’ll often see advertisements imitating download buttons. These advertisements try to trick people into downloading something they’re not looking for by masquerading as a real download link. There’s a good chance links such as this one contain malware.
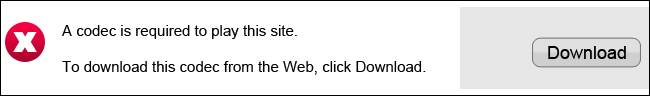
- “You Need a Plugin to Watch This Video”: If you stumble across a website that says you need to install a new browser plug-in or codec to play a video, beware. You may need a new browser plugin for some things – for example, you need Microsoft’s Silverlight plugin to play videos on Netflix – but if you’re on a less-reputable website that wants you to download and run an EXE file so you can play their videos, there’s a good chance they’re trying to infect your computer with malicious software.
- “Your Computer is Infected”: You may see advertisements saying your computer is infected and insisting you need to download an EXE file to clean things up. If you do download this EXE file and run it, your computer probably will be infected.
This isn’t an exhaustive list. Malicious people are constantly on the look-out for new ways to trick people.
As always, running an antivirus can help protect you if you do accidentally download a malicious program.
These are the ways the average computer user (and even the employees at Facebook and Apple) have their computers “hacked” via their browsers. Knowledge is power, and this information should help you protect yourself online.