Quick Links
In this edition of Geek School, we are going to look at how IP addressing works. We will also cover some advanced topics like how your PC determines if the device you are communicating with is on the same network as you. We will then finish with a brief look at two name resolution protocols: LLMNR and DNS.
Be sure to check out the previous articles in this Geek School series on Windows 7:
- Introducing How-To Geek School
- Upgrades and Migrations
- Configuring Devices
- Managing Disks
- Managing Applications
- Managing Internet Explorer
And stay tuned for the rest of the series all week long.
IP Fundamentals
When you send a letter via snail mail you have to specify the address of the person you would like to receive the mail. Similarly, when one computer sends a message to another computer it needs to specify the address that the message should be sent to. These addresses are called IP addresses and typically look something like this:
192.168.0.1
These addresses are IPv4 (Internet Protocol Version 4) addresses and like most things these days they are a simple abstraction as to what the computer actually sees. IPv4 addresses are 32-bit, which mean they contain a combination of 32 ones and zeros. The computer would see the address listed above as:
11000000 10101000 00000000 00000001
Note: Each decimal octet has a maximum value of (2^8) – 1 which is 255. This is the maximum number of combinations that can be expressed using 8 bits.
If you wanted to convert an IP address to its binary equivalent you could create a simple table, like below. Then take one section of the IP address (technically called an octet), for example 192, and move from left to right checking if you can subtract the number in the header of the table from your decimal number. There are two rules:
- If the number in the header of the table is smaller than or equal to your number, mark the column with a 1. Your new number then becomes the number you had subtract the number in the header of the column. For example, 128 is smaller than 192 so I mark the 128s column with a 1. I am then left with 192 – 128, which is 64.
- If the number is larger than the number you have, mark it with a 0 and move on.
Here is how it would look using our example address of 192.168.0.1
|
128 |
64 |
32 |
16 |
8 |
4 |
2 |
1 |
|
1 |
1 |
0 |
0 |
0 |
0 |
0 |
0 |
|
1 |
0 |
1 |
0 |
1 |
0 |
0 |
0 |
|
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
|
0 |
0 |
0 |
0 |
0 |
0 |
0 |
1 |
In the above example, I took our first octet of 192 and marked the 128s column with a 1. I was then left with 64 which is the same as the number as the second column so I marked it with a 1 as well. I was now left with 0 since 64 – 64 = 0. That meant that the rest of the row was all zeros.
In the second row, I took the second octet, 168. 128 is smaller than 168 so I marked it with a 1 and was left with 40. 64 was then greater than 40 so I marked it with a 0. When I moved into the third column, 32 was less than 40 so I marked it with a 1 and was left with 8. 16 is greater than 8 so I marked it with a 0. When I got to the 8s column I marked it with 1 which left me with 0 so the rest of the columns were marked with 0.
The third octet was 0, and nothing can go into 0 so we marked all columns with a zero.
The last octet was 1 and nothing can go into 1 except 1, so I marked all columns with 0 until we got to the 1s column where I marked it with a 1.
Subnet Masks
Note: Subnet masking can get very complex, so for the scope of this article we are only going to discuss classful subnet masks.
An IP address is made up of two components, a network address and a host address. The subnet mask is what is used by your computer to separate your IP address into the network address and host address. A subnet mask typically looks something like this.
255.255.255.0
Which in binary looks like this.
11111111.11111111.11111111.00000000
In a subnet mask the network bits are denoted by the 1s and the host bits are denoted by the 0s. You can see from the above binary representation that the first three octets of the IP address are used to identify the network that the device belongs to and the last octet is used for the host address.
Given an IP address and subnet mask, our computers can tell if the device is on the same network by performing a bitwise AND operation. For example, say:
- computerOne wants to send a message to computerTwo.
- computerOne has an IP of 192.168.0.1 with a subnet mask of 255.255.255.0
- computerTwo has an IP of 192.168.0.2 with a subnet mask of 255.255.255.0
computerOne will first calculate the bitwise AND of its own IP and subnet mask.
Note: When using a bitwise AND operation, if the corresponding bits are both 1 the result is a 1, otherwise it’s a 0.
11000000 10101000 00000000 00000001
11111111 11111111 11111111 00000000
11000000 10101000 00000000 00000000
It will then calculate the bitwise AND for computerTwo.
11000000 10101000 00000000 00000010
11111111 11111111 11111111 00000000
11000000 10101000 00000000 00000000
As you can see, the results of the bitwise operations are they same, so that means that the devices are on the same network.
Classes
As you probably have guessed by now, the more networks (1s) you have in you subnet mask the less host (0s) you can have. The number of hosts and networks you can have is divided up into 3 classes.
|
Networks |
Subnet Mask |
Networks |
Hosts |
|
|
Class A |
1-126.0.0.0 |
255.0.0.0 |
126 |
16 777 214 |
|
Class B |
128-191.0.0.0 |
255.255.0.0 |
16 384 |
65 534 |
|
Class C |
192-223.0.0.0 |
255.255.255.0 |
2 097 152 |
254 |
Reserved Ranges
You will notice that the 127.x.x.x range has been left out. This is because the entire range is reserved for something called your loopback address. Your loopback address always points to your own PC.
The 169.254.0.x range was also reserved for something called APIPA which we will discuss later on in the series.
Private IP Ranges
Up until a few years ago every device on the internet had a unique IP address. When IP addresses began to run out, a concept called NAT was introduced which added another layer between our networks and the internet. IANA decided that they would reserve a range of addresses from each class of IPs:
- 10.0.0.1 – 10.255.255.254 from Class A
- 172.16.0.1 – 172.31.255.254 from Class B
- 192.168.0.1 – 192.168.255.254 from Class C
Then instead of assigning each device in the world an IP address, your ISP provides you with a device called a NAT Router which is assigned a single IP address. You can then assign your devices IP addresses from the most suitable private IP range. The NAT Router then maintains a NAT table and proxies your connection to the internet.
Note: The IP of your NAT Router is usually assigned dynamically via DHCP so it normally changes depending on the constraints your ISP has in place.
Name Resolution
It is way easier for us to remember human readable names like FileServer1 than it is to remember an IP address like 89.53.234.2. On small networks, where other name resolution solutions like DNS don’t exist, when you try to open a connection to FileServer1 you computer can send a multicast message (which is a fancy way of saying send a message to each device on the network) asking who FileServer1 is. This method of name resolution is called LLMNR (Link-lock Multicast Name Resolution), and while it’s a perfect solution for a home or small business network it doesn’t scale well, firstly because broadcasting to thousands of clients will take too long and secondly because broadcasts don’t typically traverse routers.
DNS (Domain Name System)
The most common method to solve the scalability issue is to use DNS. The Domain Name System is the phonebook of any given network. It maps human readable machine names to their underlying IP addresses using a giant database. When you try to open a connection to FileServer1 your PC asks your DNS Server, which you specify, who FileServer1 is. The DNS Server will then respond with an IP address which your PC can in turn make a connection to. This is also the name resolution method used by the largest network in the world: the internet.
Changing Your Network Settings
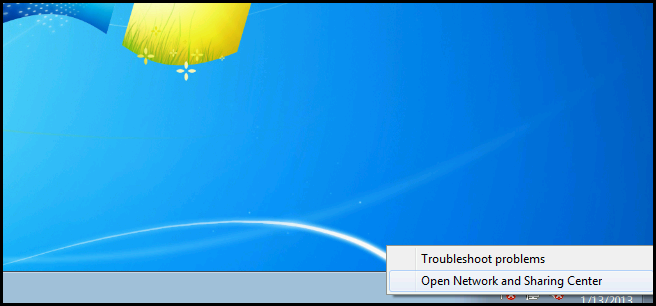
Right click on the network settings icon and select Open Network and Sharing Center from the context menu.
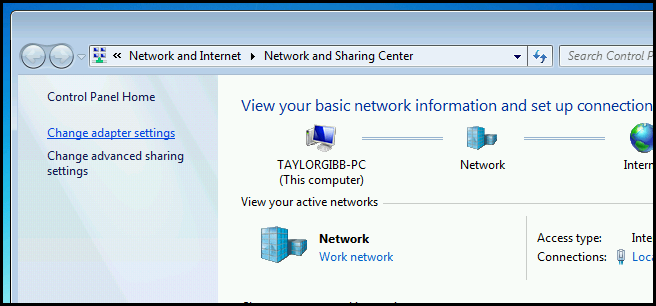
Now click on the Change adapter settings hyperlink on the left hand side.
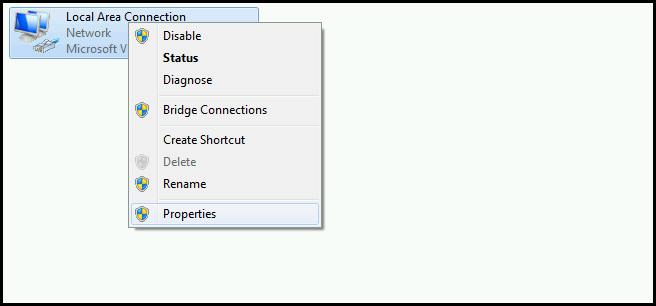
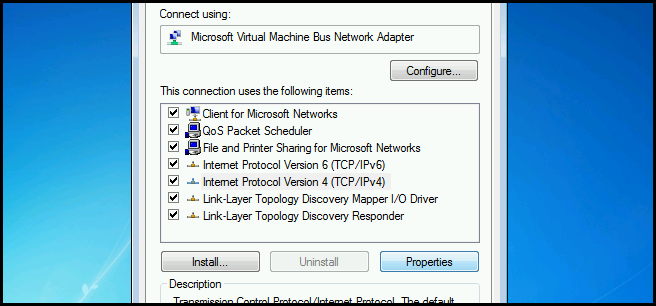
Then right click on your network adapter and select Properties from the context menu.
Now select Internet Protocol Version 4 and then click on the properties button.
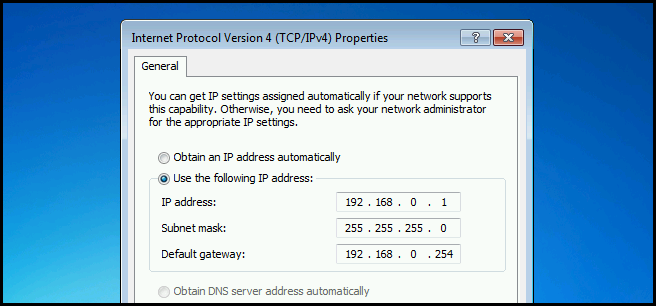
Here you can configure a static IP address by selecting the radio button for “Use the following IP address”. Armed with the information above, you can fill in an IP address and subnet mask. The default gateway, for all intents and purposes, is the IP address of your router.
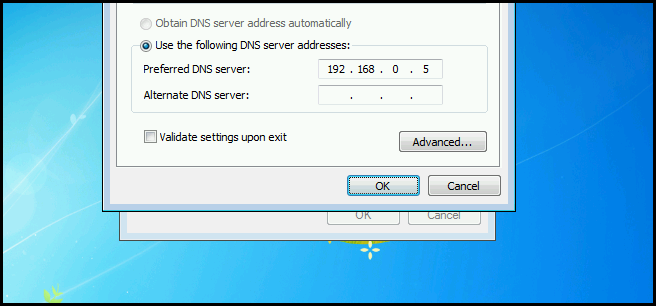
Near the bottom of the dialog you can set the address of your DNS server. At home you probably don’t have a DNS server, but your router often has a small DNS cache and forwards queries to your ISP. Alternatively, you could use Google's public DNS server, 8.8.8.8.
Homework
- There is no homework for today, but this has been a long one, so read over it again. If you are still hungry for more information you can read up on an advanced networking subject called CIDR (Classless Interdomain Routing).
If you have any questions you can tweet me @taybgibb, or just leave a comment.