Quick Links
Internet Explorer is a complex piece of software and hasn't always been the browser choice of us geeks, but the truth is that it has gotten a lot better over the years so come and see what it has to offer.
Be sure to check out the previous articles in this Geek School series on Windows 7:
- Introducing How-To Geek School
- Upgrades and Migrations
- Configuring Devices
- Managing Disks
- Managing Applications
And stay tuned for the rest of the series all week long.
Compatibility View
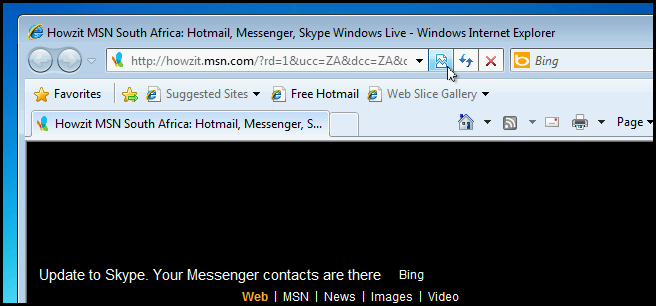
Internet Explorer is notorious for not being able to render pages that worked perfectly in previous generations of the browser. To remedy the situation Microsoft added a feature to IE called Compatibility View. In a nutshell, it allows you to view webpages using the rendering engines of past Internet Explorer versions. To use compatibility view all you have to do its click on the little icon that looks like a page that has been torn in half, which is located in the URL Bar.
RSS Feeds
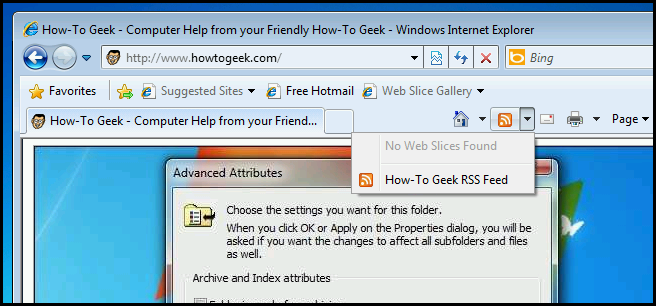
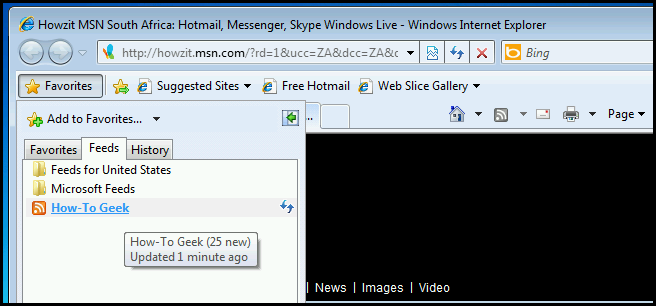
If you don’t already know what they are, RSS feeds provide a great way for you to stay up to date with your favorite websites by allowing you to subscribe to them. When one of the websites you are subscribed to adds new content, for example when How-To Geek releases a new article, you will automatically be notified. In Internet Explorer, if the RSS button turns orange it means that the website you are viewing supports RSS feeds.
Once you have subscribed to the feed, you can quickly check if any new content has been added.
Security Zones
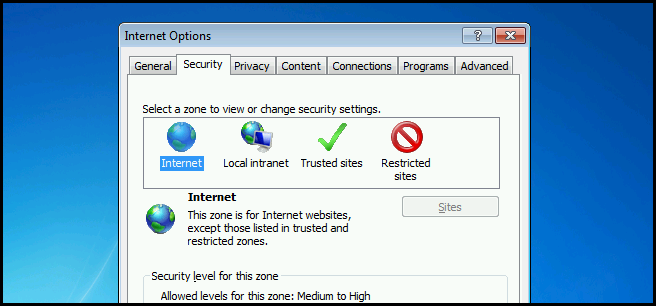
Internet Explorer assigns all websites to one of four security zones: Internet, Local intranet, Trusted sites, or Restricted sites. The zone to which a website is assigned specifies the security settings that are used for that site. Let's take a closer look at what type of websites each of the four zones should contain:
- Local intranet – This zone should contain sites that reside inside your company's firewall.
- Trusted – This zone contains all sites that you know are trusted, for example the site of a business partner.
- Internet – This zone contains all sites on the internet that are not in the Trusted, Local intranet or Restricted zones.
- Restricted – This zone contains sites that you do not trust.
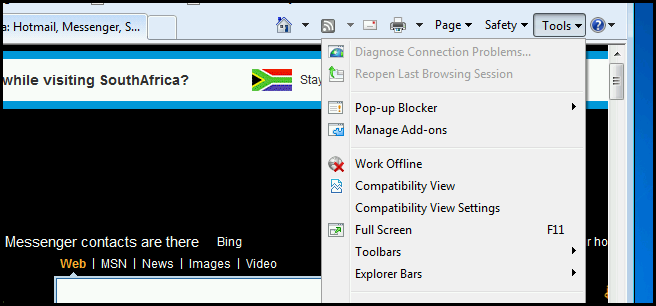
If you want to you can also change the security settings that are applied to any particular zone. To do this, click on Tools and then choose the Internet Options menu item.
Then switch over to the Security tab.
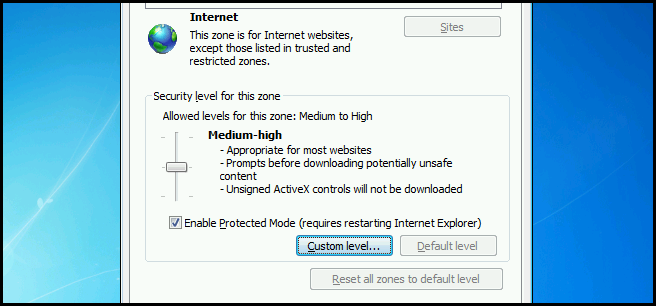
You can either choose one of the pre-defined security levels by moving the slider, or you can click on the Custom level button.
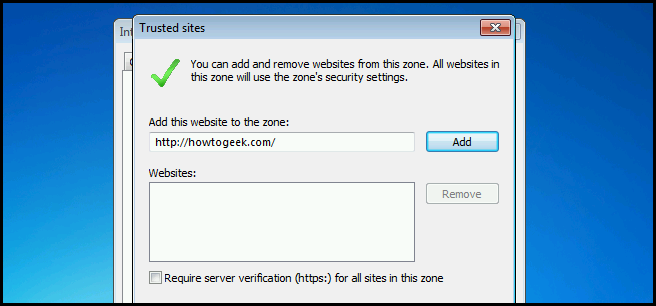
Configuring a Trusted Site
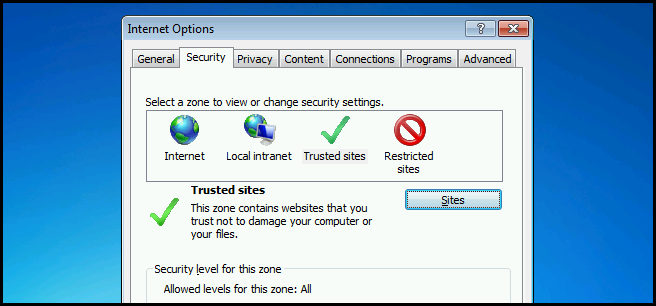
To add a site to the Trusted Sites security zone, select the zone and then click on the Sites button.
Now enter the URLs of any sites that you know for sure are not a threat. Then click add.
You can do the same for the other zones, just be careful about what you add to each zone.
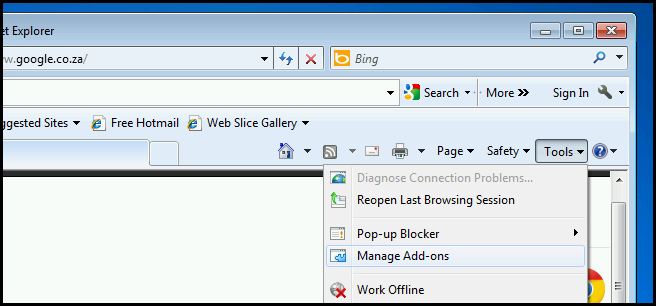
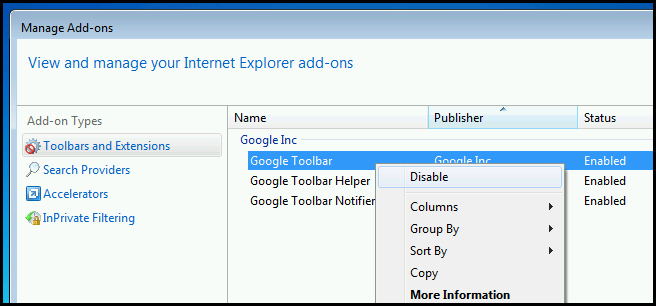
Managing Add-Ons
Internet Explorer has add-ons which are the equivalent of plug-ins in Chrome and Firefox, and serve to extend the functionality of the browser. One of the more infamous types of add-on is a toolbar. These are those pesky search bars that often get added to Internet Explorer when you install some kind of application. To manage toolbars, click on the Tools menu and then choose the Manage Add-ons menu item.
From here you can right click on any toolbar and disable it. If you wish to uninstall the toolbar, you must use the Control Panel to uninstall it just as you would any other application.
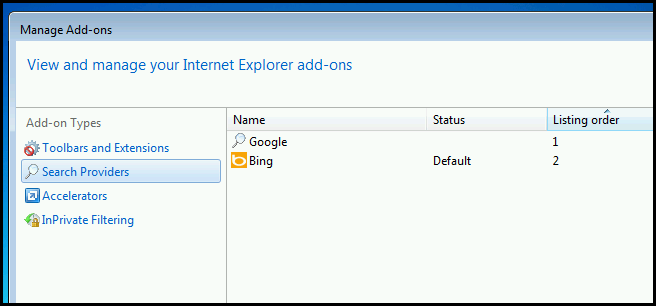
Search Providers
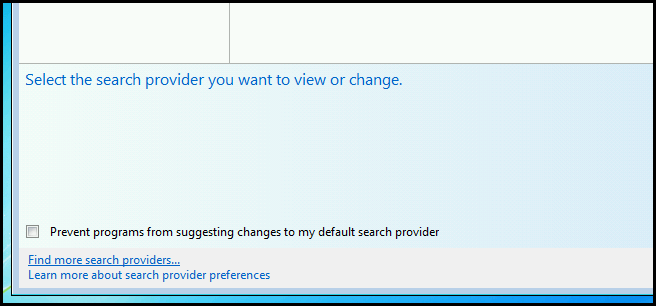
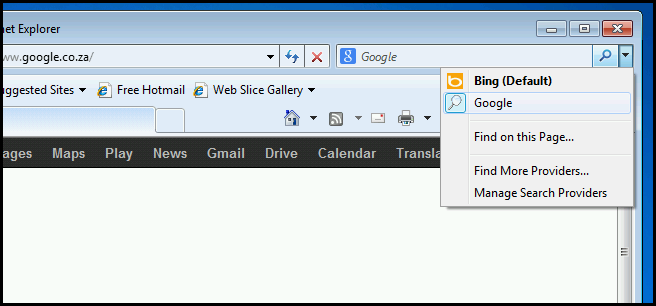
Another type of add-on is a Search Provider, which allows you add additional search engines to Internet Explorer. To add a Search Provider, switch over to the Search Providers section.
In the bottom left hand corner of the Window you will see a Find more search providers… hyperlink. Click on it.
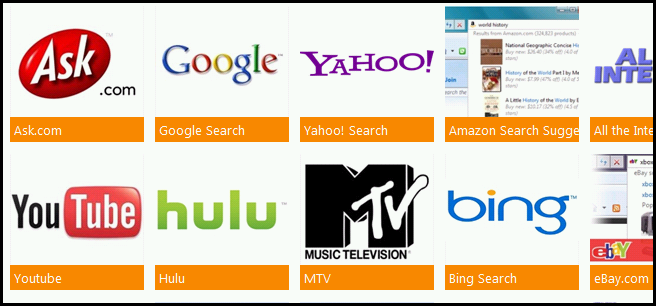
From here you can choose from thousands of providers.
Once added, you can search that site directly from the search bar.
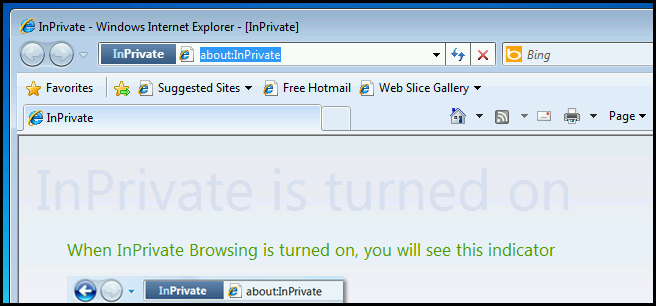
InPrivate Mode
InPrivate Mode is the Internet Explorer equivalent of Chrome's Incognito mode. For those who have never used either before, it's simply a way to privately browse the web without leaving a trace on your PC. It does this by only keeping browsing data within your session. When you close an InPrivate session its deletes:
- All cookies from that session
- Your browsing history
- Any objects that may have been in your browser cache
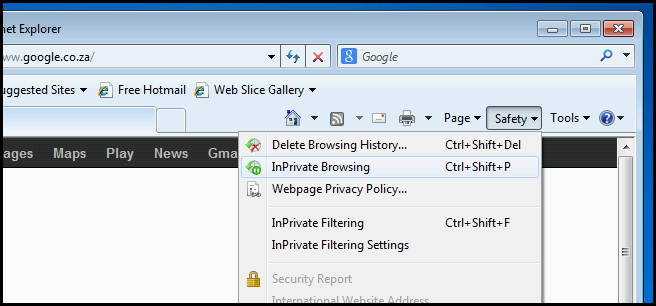
To open InPrivate browsing session, click on Safety and then choose InPrivate browsing.
You can tell when you are in InPrivate mode by looking at the URL bar.
Security Features
Internet Explorer has a few other security features that you need to know about for the exam. However, you just need to know what they are and that they are built-in features, so let's take a look.
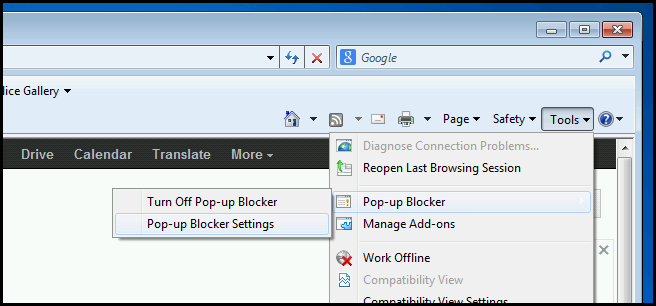
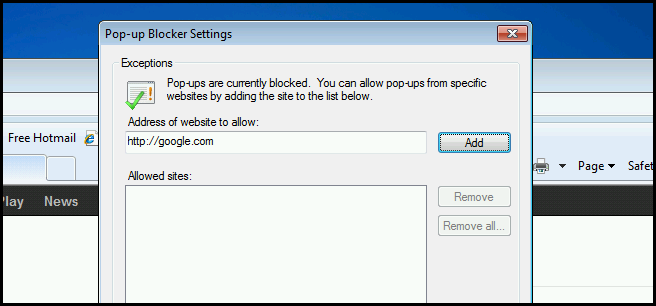
Popup Blocker
Internet Explorer comes with its own Popup blocker to stop those pesky adverts from opening. The popup blocker works on a whitelist system where by default all popups are blocked and you can allow popups on certain websites by whitelisting the URL. To whitelist a URL, click on Tools, select Pop-up Blocker and then Pop-up Blocker Settings.
Then type in the URL of the site and click add.
InPrivate Filtering
Many websites generate income from adverts that originate from a third party advertising company, that means that the content you see on a webpage doesn’t originate from the website that you think you are on. While that isn't uncommon in practice, over the years advertising companies have caught on and started using these adverts to build a profile of the websites you visit so that they can show you targeted adverts. InPrivate Filtering sets out to stop this and does so by blocking any content that originates from any site other than the one you are on.
Protected Mode
Protected Mode takes advantage of three Windows components, UAC (User Account Control), MIC (Mandatory Integrity Control) and UIPI (User Interface Privilege Isolation). Together they allow you to run Internet Explorer with a low integrity level, even if you are logged in as an administrator. The idea is that even if an attacker somehow gets access to the IE process they will be very limited in what they can do.
SmartScreen Filter
The SmartScreen filter consists of three components. Firstly, its has a heuristics engine that analyses webpages for suspicious behavior as you browse the web and will warn you to proceed with caution. Secondly, it helps against phishing attacks by checking the URL of websites you visit against a list of known phishing websites and blocks them if necessary. Finally, it checks any files you download against a list of programs that are known to be unsafe.
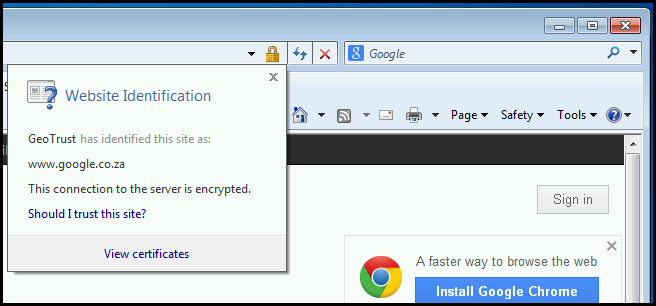
Certificates
Imagine you own a bank and open an online banking portal, but the problem is your customers are hesitant to use it because they don’t know if they are in fact connecting to your bank. This is an issue of identity verification and is what certificates were designed for.
It all starts with a few select companies called Public Certification Authorities, who we automatically trust. The reason we trust them is because we have a small file for each company, called a certificate, which lives in our Trusted Root Certification Store. When you want to verify your identity you can go to one of these companies, for example Thawte or VeriSign, who will in turn do background checks and then issue you a certificate which you can put on your web server.
Now, when your users connect to your bank's online portal, their browser will see that the certificate for your bank was created by a company that we already trust. Therefore we can be certain that your bank owns this website. In addition to being able to verify that they are connected to your web servers, the certificates will also be used to encrypt their browsing traffic.
You can see who verified a website by clicking on the lock in the URL bar.
Homework
Today we went through nearly every feature the browser has to offer, so feel free to take the day off.
If you have any questions you can tweet me @taybgibb, or just leave a comment.