Quick Links
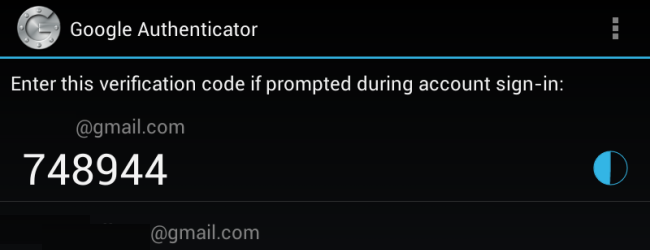
Most of the app data on your Android is probably synced online will automatically sync to a new phone or tablet. However, your Google Authenticator credentials won’t -- they aren’t synchronized for obvious security reasons.
If you’re doing a factory reset, getting a new phone, or just want to copy your credentials to second device, these steps will help you move your authenticator data over so you won’t lose your access codes.
Move to a Different Phone
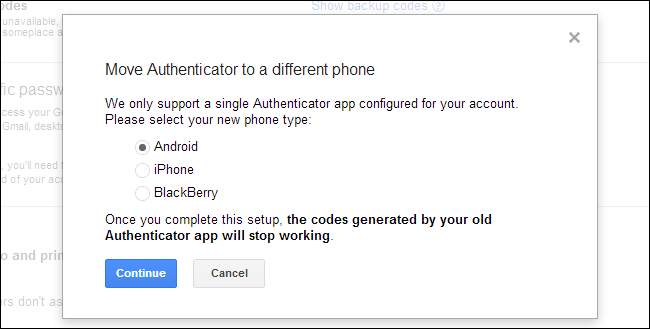
Google now allows you to move your credentials to a different phone. Access the 2-step verification page, click the Move to a different phone link, and scan the QR code or enter your credentials into a new phone. Your old authentication app will stop working.
Other services that use Google Authenticator may not offer this feature, so you may need to disable and re-enable your account or extract your codes instead. One of the processes below will also allow you to enable Google Authenticator on multiple devices – such as your phone and your tablet – although Google claims not to support this.
Disable & Re-enable Two-Step Authentication
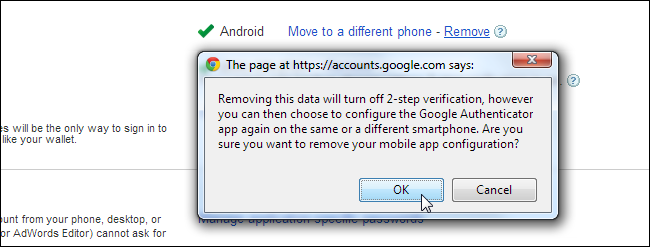
If you’re performing a factory reset and don’t want to rely on your printed security codes or SMS verification, you may want to disable two-step authentication ahead of time. To do so, click the Remove link on the 2-step verification page. This temporarily disables two-factor authentication.
Perform the factory reset and then add an authentication app again from this page. When you reach the stage where you’re given a QR code and a code you can manually type, re-enter it into your phone. If you want to enable Google Authenticator on multiple devices, enter the code into multiple devices before closing this window.
While you could write down the code displayed here and keep it in a safe place, that isn’t necessarily a good idea – anyone who found it would be able to enter it into their own phone and see your time-based authentication codes.
Back Up & Restore Your Google Authenticator Data [Root Only]
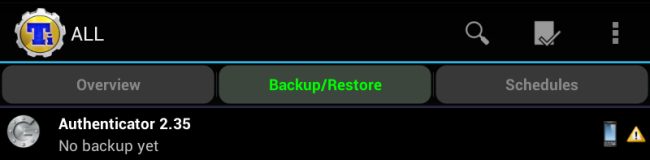
If your Android is rooted, you can use Titanium Backup, which we’ve written about before, to take a backup of your Google Authenticator app data. For security reasons, it’s not normally possible for another app to read this data – that’s why root access is required.
Locate Authenticator under the Backup/Restore tab and use the backup option to back up its data. Copy the backup data from the TitaniumBackup folder on your device to your computer. You can then copy it to your new device and restore it later.
Note that this may not work with devices running different versions of the Android operating system, but it’s perfect for restoring after a factory reset.
Manually Extract Your Credentials [Root Only]
If you have root access to your device, you can actually extract the credentials manually, although it’s more work than just using Titanium Backup.
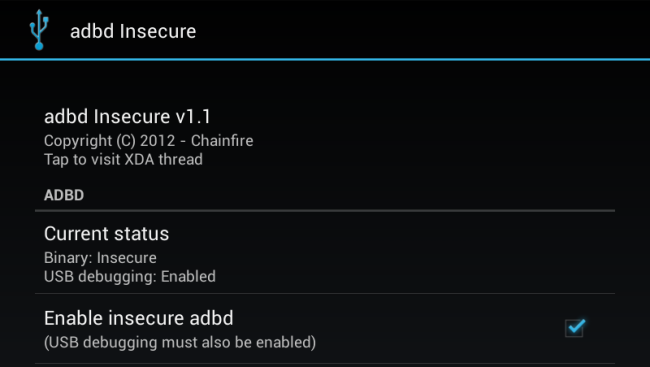
adb will need root access for you to do this – if you’re using a custom ROM, you may already have an adb with root access. If you’re using a stock ROM, you’ll need something like adbd Insecure to do this. You can download adb Insecure from Google Play or for free on the XDA Developers forums. Use the app to put adbd in insecure mode.
Note: If you have root access, you can also grab the databases file from /data/data/com.google.android.apps.authenticator2/databases/databases using a root file explorer and copy it to your computer
Once adb is in insecure mode, you can connect your Android device to your computer and use the adb command (setup instructions here) to grab the Google Authenticator databases file and copy it to your computer:
adb pull /data/data/com.google.android.apps.authenticator2/databases/databases
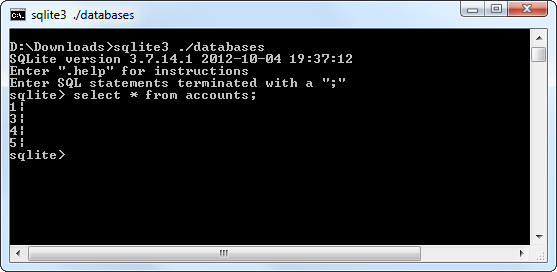
You can then use an sqlite editor to open the file and view its contents. If you’re using the command-line sqlite3 program, use the following commands:
sqlite3 ./databases
select * from accounts;
You’ll see your Google Authenticator keys, which you can now re-add to another device.
Luckily, Google no longer resets your application-specific passwords – even if you disable and re-enable Google Authenticator, your application-specific passwords will remain valid.
Thanks to Dan over at cadince for inspiring much of this post!