So far in our series we've covered how to reset your Windows password with the Ultimate Boot CD, but if you are a little more technical you might want to simply use the excellent System Rescue CD, which is based on Linux.
Note that if you are using standard Windows encryption for your files, resetting the password will permanently disable access to those files. In that case you should crack the password, which is something we'll cover in an upcoming article.
If you are an Ubuntu user and forgot your password, we've covered how to do that as well, either the easy way with the grub menu or alternately with the live cd.
Creating the System Rescue CD
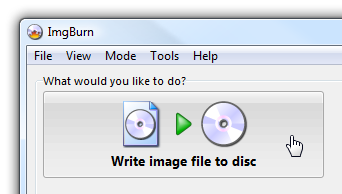
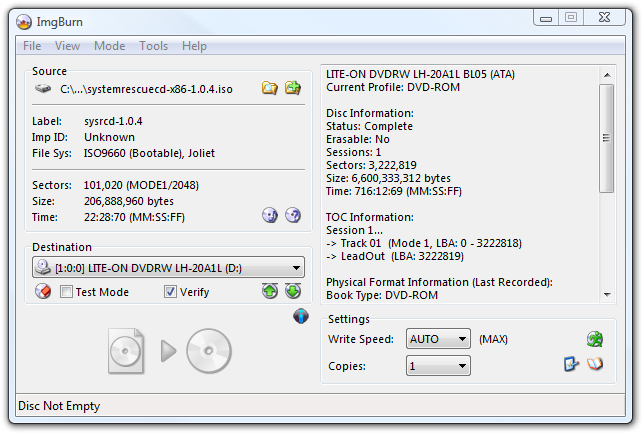
Before you can do anything else, you'll need to download a copy of the System Rescue CD and burn the ISO image to disc. For this task, I prefer the simple ImgBurn utility, but you are free to use whatever burning application you prefer instead.
If you are using ImgBurn, click the Write image file to disc button...
Click the File button near Source and then pick the ISO file, then click the Burn button near the bottom. That's about all there is to it.
Download the System Rescue CD from sysresccd.org
Resetting Your Password
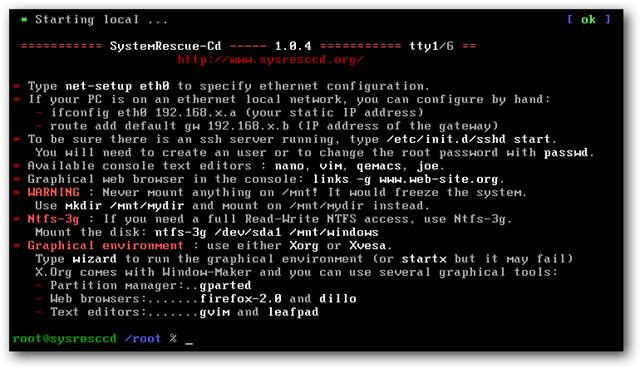
Now that you have your boot CD, you'll want to boot from it, which will take you to this very informative prompt, with some basic instructions on how to use the CD.
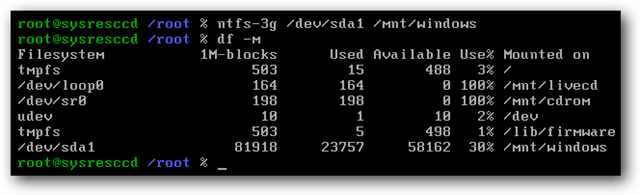
The first thing we'll want to do is mount the hard drive, using this command. (Note that you might not need to use the --o force argument, it's only really for when the system didn't shut down correctly)
ntfs-3g /dev/sda1 /mnt/windows --o force
You can use the df --m command to verify that the drive has been mounted and that it's the right drive. Note that it's mounted on /mnt/windows at this point.
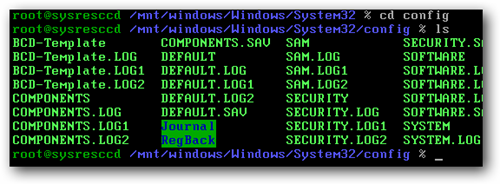
Now you'll want to change directory into the Windows/System32/config directory inside of your windows installation. For mine, the full path was something like this, but it might be different on yours:
cd /mnt/windows/Windows/System32/config
Once you are in that directory, you should see that there is a SAM file, which is where we'll want to change the passwords.
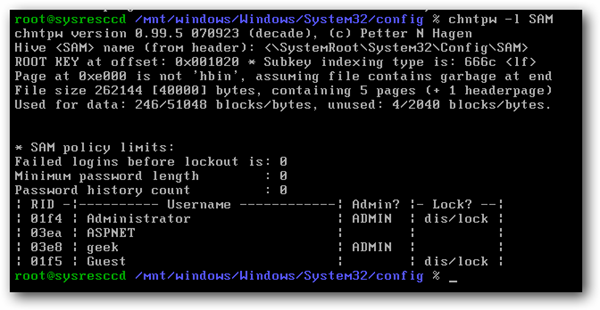
To change the password we'll use the chntpw command, and it's most useful to use the --l argument first to list out all the usernames in the file.
chntpw --l SAM
Now you can add the --u argument with your username, which will end up being something like this command, except you'll want to replace geek with your username:
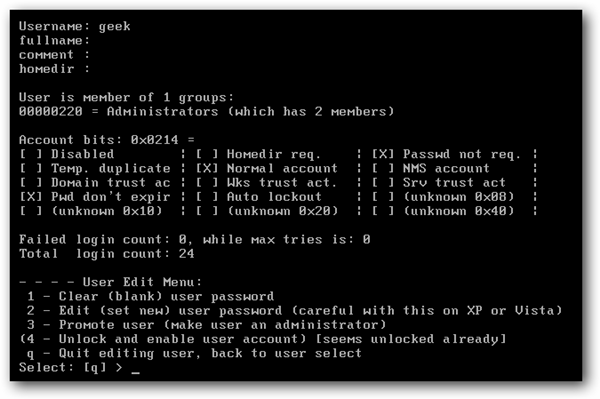
chntpw --u geek SAM
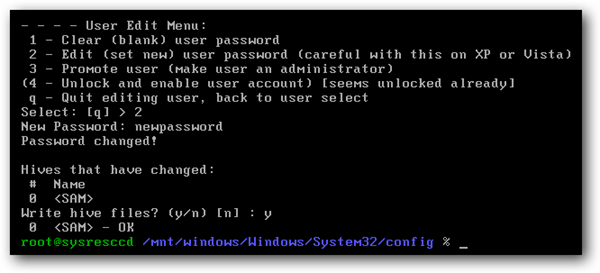
This will present you with a wizard type screen:
I'm going to assume that you want to set a new password, so just type "2" at the prompt, add in your password, and remember to use the "y" key when prompted to save.
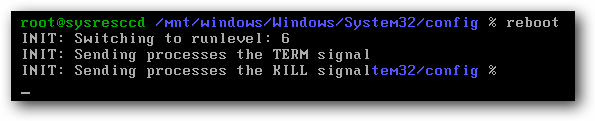
At this point your password has been changed, so you can issue the reboot command to restart the computer (should take the disc out of the drive)
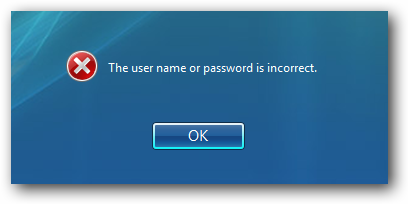
And now you should be able to login with the new password:
Note that I tested this technique on both XP, Vista and Windows 7 with good results.