Quick Links
There are few security problems a healthy dose of paranoia and know-how can't take care of. Today we're looking at how to secure your Android phone's mobile data connection against intrusion using free software and a simple SSH tunnel. HTG Reader Michael wrote in with a simple request that we're more than happy to fulfill:
Dear HTG, I read your guide to setting up an SSH server on your home router and configuring your laptop to connect through it, but I'm a little bit overwhelmed trying to translate what I learned in that guide to my Android phone. Is there a straight forward way to get that same home-link-encryption I'm enjoying on my laptop onto my Android phone? I successfully completed the original tutorial (so I have an SSH server running on my router now) for what it's worth. Can you help a just-smart-enough reader out? Sincerely, Michael
We think you're selling yourself short with the just-smart-enough label, Michael. After all, you were able to flash your home router, configure the built-in SSH server, and set up your laptop as a client. With that under your belt you'll find this guide to doing the same for your phone downright easy! Let's get started. If you're reading this an unsure on what exactly SSH is or why you would want to enable it on your smartphone (or other mobile device), we strongly suggest reading the What Is and Why Setup a Secure Tunnel section in our SSH router setup guide.
What You'll Need
For this tutorial you'll need the following things:
- A rooted Android phone running Android OS 1.6 or above.
- A free copy of SSH Tunnel for Android.
- An SSH Server to connect to.
A few notes on the above requirements are in order. First, to properly configure and deploy SSH Tunnel for Android, you need to have root access on your Android phone. If your phone is not already rooted, we strongly recommend reading our guide on the subject, How to Root Your Android Device & Why You Might Want To, as it both covers the basics of rooting and shows you how to do so. Second, we will be building on our guide Setup SSH on Your Router for Secure Web Access from Anywhere in this tutorial. You do not need to be using the exact same setup we're using (the built-in SSH server on a router flashed with third-party Tomato firmware) but you will need to have an SSH server (whether hosted on a remote server or your home network) to connect into. Moving forward from this point we will be assuming that you have, at minimum, an SSH account with the username, password and (if you want increased security) an authorized key pair for that account on hand. If any of these terms seem unfamiliar, again, we would strongly suggest reading the Setup SSH on your Router guide linked to above.
Downloading and Configuring SSH Tunnel for Android
While SSH Tunnel for Android isn't the only SSH tool available for the Android platform, we favor it for a variety of reasons including ease of configuration, ease of daily use, and---most importantly---the target audience. SSH Tunnel was conceived as a tool for users in China and other countries where oppressive and censoring governments heavily restrict access to the internet. If it's good enough for people in places like China (who risk their freedom circumventing government firewalls) then it's good enough for us. Grab a free copy in the Google Play store (or, if you're unable to access the Google Play store in your location, grab the APK file here to manually install it). Install the application and run it for the first time to begin the configuration process. The first screen you'll see will look like this:
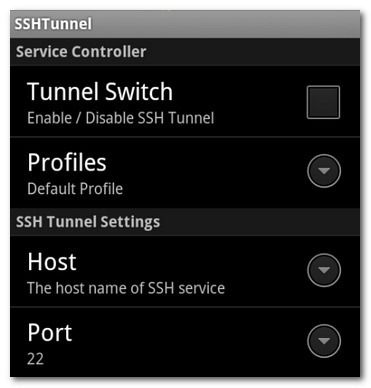
Resist the urge to check Tunnel Switch and turn the tunnel on---we haven't inputted any of the login information yet so it will just error out. Let's start out by visiting the SSH Tunnel Settings section of the menu. Input the following information: your host's IP and the port the SSH server is listening on. The default port is 22 for SSH; unless you have specifically changed the port or been instructed by your SSH host to use an alternate port, leave it as 22. In the Account Information section, input your username and password on the SSH server. At this point we have enough information entered to form a simple connection between SSH Tunnel and your SSH server with password-based authorization. If you wish to use a key-pair to further secure your connection to your SSH server---and we strongly recommend you do so--you'll need the private key half of the pair now. (If you need to generate a pair, please reference the Generating Keys section of our SSH router guide.) Note: You toggle your SSH server between using login/password only and login/key-pair from the SSH server side of things, not the SSH tunnel application on your phone. Please reference the appropriate help menu/documentation on your SSH server for assistance if necessary. Once you have the private key file (ending with .ppk) you'll need to copy it to /sdcard/sshtunnel/key/. In order to use the key, press the menu button on your phone to pull up the following interface:
Press Key File Manager and simply navigate to the /sshtunnel/key/ directory. Select the appropriate key for your SSH server---you may find it handy to name each key based on the service such as HomeRouter.ppk or SomeSSHService.ppk if you decide to use the Profiles function to utilize multiple SSH servers. Once you have either set up the password and/or private key, it's time to finish up the last of the configuration.
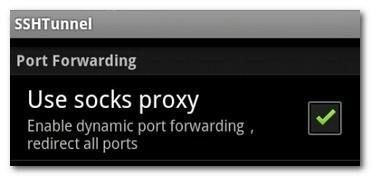
Under the Account Information section is the Port Forwarding section. In order to expedite the process, we suggest turning on the built-in SOCKS proxy server in order to increase application compatibility with SSH Tunnel. Simply check "Use socks proxy" to turn it on.
Finally, it's time to decide if you want to route your entire Android data connection through your SSH server or selectively redirect applications through the server. To route your entire connection check "Global Proxy". To selectively route applications choose "Individual Proxy" and then check the individual applications you wish to route---such as your web browser and Facebook---as seen above. At this point we're ready to rock, but before we fire up the tunnel let's take a peek at the last few configuration options so you can decide if you wish to use them or not. From the Feature Settings sub-section of the configuration menu:
- Auto Connect: Turning this on will set SSH Tunnel to automatically probe and connect to the SSH server whenever it is available.
- Auto Reconnect: Turning this on toggles the auto-reconnection protocol so SSH Tunnel will re-establish connection in the event of unexpected loss.
- Enable GFW List: This is a feature specifically for Chinese citizens; it enables the SSH Tunnel proxy service only for web sites specifically blocked by China's Great Firewall.
- Enable DNS Proxy: This is checked by default and we recommend leaving it checked. When checked, all your DNS requests are routed through the SSH server. If you uncheck it, your DNS requests will be sent through your phone's data connection without the protection of the SSH tunnel. (e.g. anyone spying on you will see where you're going but not the data you're getting from the web site you're visiting.)
Have that all set to your satisfaction? Great! Let's test the connection now.
Testing Your SSH Tunnel Connection
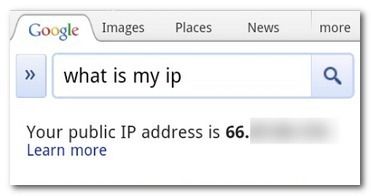
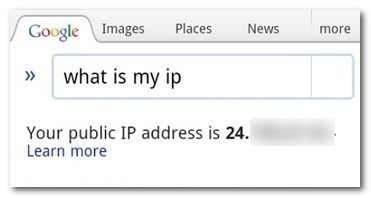
In order to establish our SSH connection is working we need to first establish the IP address of our mobile device. Open your phone's web browser and perform a Google search for "what is my ip". Your results should show your mobile data connection IP address like so:
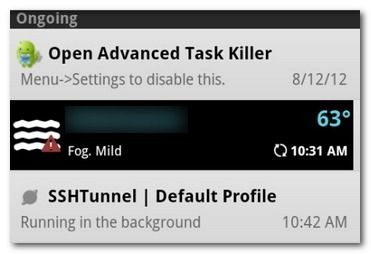
That's the IP address assigned by our cellular provider to our Android smartphone. Although we have SSH Tunnel configured, it isn't on yet and we're still sending all our DNS requests and data requests out in the open. Open SSH Tunnel back up and, at the very top, check Tunnel Switch. This turns on the SSH tunnel---the first time you do this you'll get a prompt from the root/SuperUser interface verifying that it's OK to give SSH Tunnel super user permissions. It's fine, go ahead and check the Remember box (otherwise you'll need to authorize it every single time it connects in the future). Give it a moment to connect---it will notify you that the connection is successful. If you left the notifications on in the settings menu, you'll also see a notice in your pull-down notification drawer like so:
Now it's time to check if the browser is routing properly through the SSH tunnel. Go ahead and switch back over to the web browser and refresh your "what is my ip" query. You should see a new IP address that corresponds to the IP address of your SSH server, like so:
Success! With a simple tap of a button, we've swapped all our web browser traffic over to remote SSH server. Now everything that happens between our mobile browser (or entire phone if you configured it for Global Proxy) is completely encrypted to anyone who may be snooping on the connection between the phone and the exit point at the SSH server.
That's it! You're now browsing on the go like a super-spy-guy and nobody can get up in your business. Whether you're trying to keep packet sniffers at the coffee shop from seeing your Facebook login and traffic or the boot of a corrupt government off your neck, you're in business.