Quick Links
SSH offers more than just a secure, remote terminal environment. You can use SSH to tunnel your traffic, transfer files, mount remote file systems, and more. These tips and tricks will help you take advantage of your SSH server.
SSH doesn't just authenticate over an encrypted connection -- all your SSH traffic is encrypted. Whether you're transferring a file, browsing the web, or running a command, your actions are private.
SSH Tunneling
SSH tunneling allows a remote SSH server to function as a proxy server. Network traffic from your local system can be sent through the secure connection to the SSH server. For example, you could direct your web browsing traffic through an SSH tunnel to encrypt it. This would prevent people on public Wi-Fi networks from seeing what you're browsing or bypass website and content filters on a local network.
Of course, the traffic becomes unencrypted when it leaves the SSH server and accesses the Internet. To a web server you access through the tunnel, your connection will appear to be coming from the computer running your SSH server, not the local system.
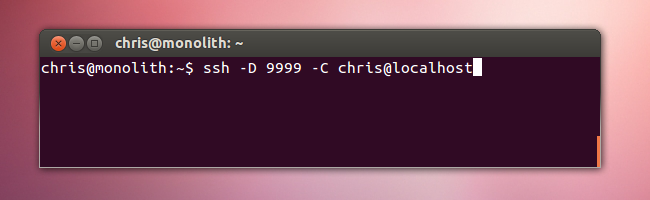
On Linux, use the following command to create a SOCKS proxy at port 9999 on your local system:
ssh -D 9999 -C user@host
'
The tunnel will be open until your SSH connection terminates.
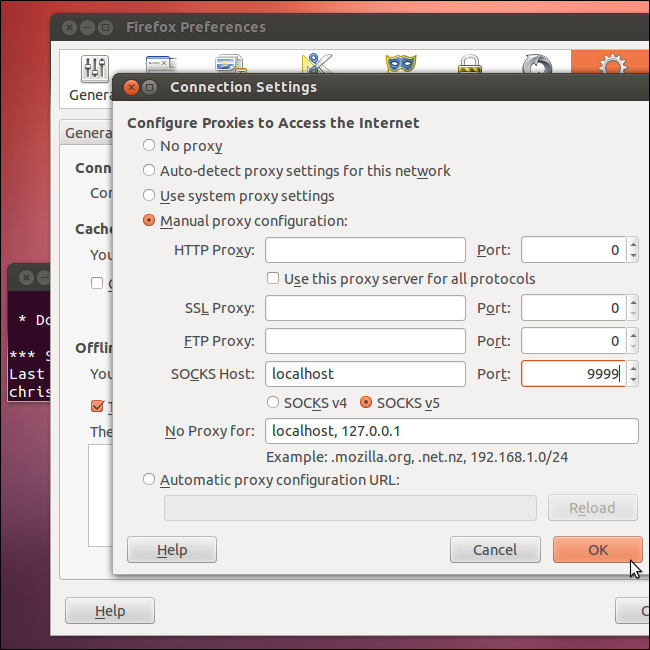
Open your web browser (or other application) and set the SOCKS proxy to port 9999 and localhost. Use localhost because the tunnel entrance is running on your local system.
We've also covered using PuTTY to set up an SSH tunnel on Windows.
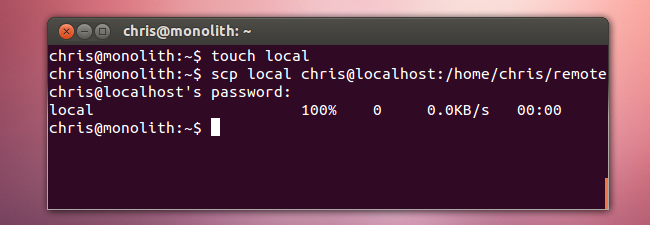
SCP File Transfers
The scp, or secure copy, command allows you to transfer files between a remote system running an SSH server and your local system.
For example, to copy a local file to a remote system, use the following syntax:
scp /path/to/local/file user@host:/path/to/destination/file
To copy a file on a remote SSH server to the local system, use this syntax instead:
scp -r user@host:/path/to/remote/file /path/to/destination/file
You can also set up passwordless scp access and use scp to transfer files from within scripts.
Mounting Remote Directories
You can mount a remote folder over SSH and access it like any other directory on your system, skipping the tedious scp process for file transfers.
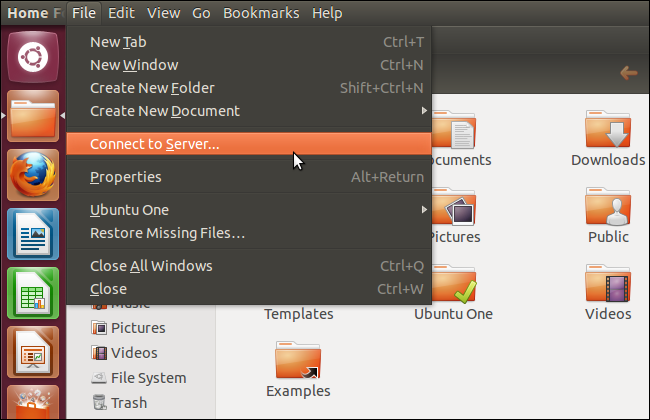
If you're using Ubuntu or another GNOME-based desktop environment with the Nautilus file manager, launch the file manager, click the File menu and select Connect to Server.
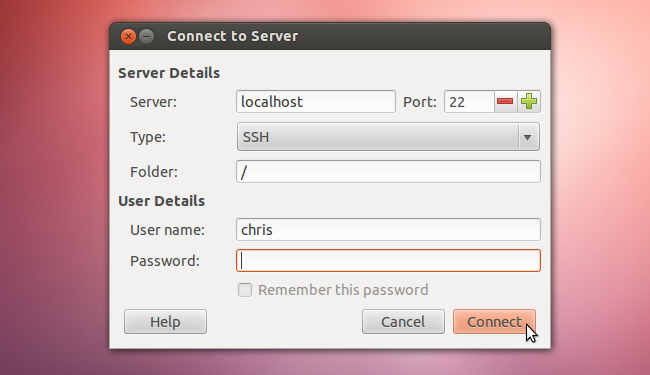
You'll be prompted to enter the SSH server's details and your credentials.
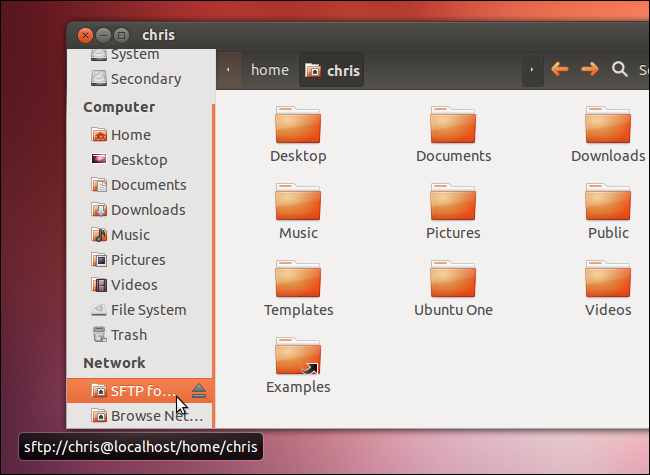
The files on the remote system will appear in your file manager.
Other Linux desktop environments may have similar options to easily mount a directory over SSH.
If you don't have access to a GUI or would rather use a terminal utility, you can use sshfs to mount the remote SSH system as a file system on your computer.
Preserving Terminal Sessions
Every time you log in with SSH, you'll be presented with a new terminal session. When you log out, your session will be closed. If you'd rather preserve a terminal session between SSH sessions, use GNU Screen or an alternative utility.
After logging into the remote system, run the screen command to launch a screen session. Run commands within the screen session, and then press Ctrl-a and then d to detach from the screen session.
The screen session and the commands running inside it continue to run in the background. To reattach to the screen session later, run the screen -r command.
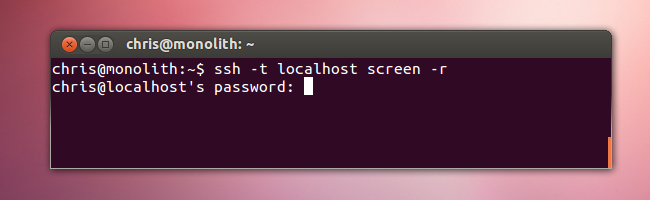
SSH can accept commands to run when you log in, so you can connect to an SSH server and reconnect to a screen session with a single command:
ssh -t user@host screen -r
If you have local access to the system running the SSH server, you can move between accessing the screen session locally and remotely.
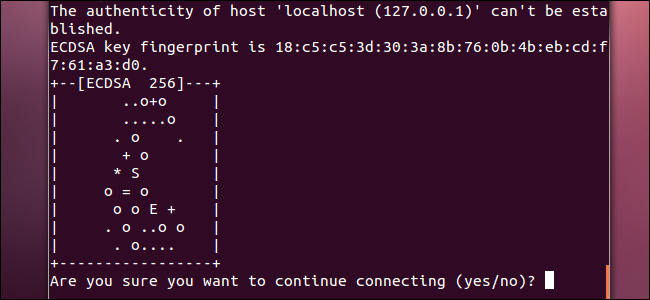
Visualizing Key Fingerprints
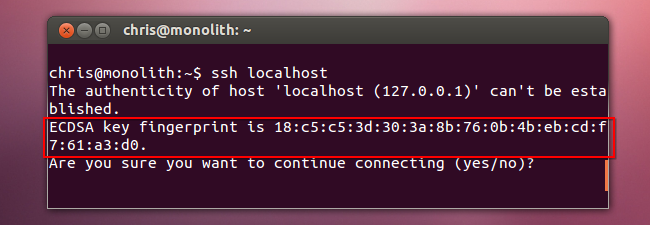
When you connect to your SSH server from another system, you'll see a warning message if the system doesn't already know its key. This message helps you ensure the remote system isn't being impersonated by another system.
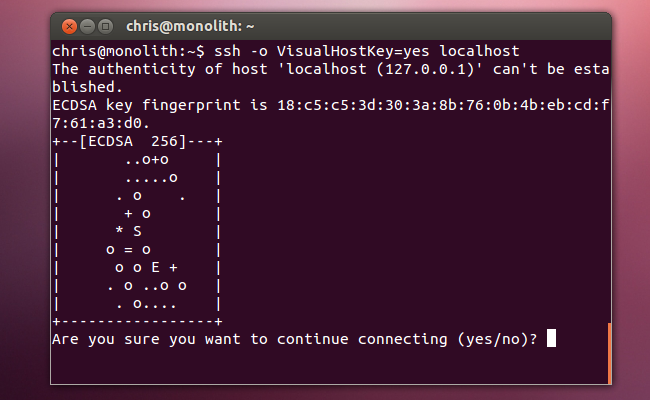
However, you may have trouble remembering the long string that identifies the remote system's public key. To make the key's fingerprint easier to remember, enable the "visual host key" feature.
You can enable this in your SSH config file or just specify it as an option while running the SSH command. For example, run the following command to connect to an SSH server with VisualHostKey enabled:
ssh -o VisualHostKey=yes user@host
Now you'll only have to remember the picture, not a long string.
Do you have any other tips to share? Leave a comment and let us know.