With the use of smartphones, tablets, laptops, and netbooks, most of us do everyday tasks online, such as purchasing goods and banking. However, if we don't secure our personal data on our computers and online, we could be asking for serious trouble.
The following 10 articles are the top methods we've covered for securing files and personal information both online and off, securing your Wi-Fi network, protecting website login information and passwords and other offline data.
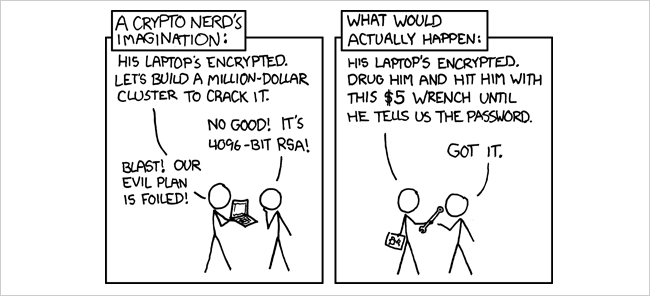
Image by xkcd, obviously.
Encrypt a Hard Drive or USB Flash Drive Using TrueCrypt
One of the best options for securing files on your computer and on external drives is a free open source disk encryption utility called TrueCrypt. It works with Windows, Linux, and Mac and allows you to encrypt an entire drive, partition, or flash drive or create an encrypted file store in which you can store sensitive data files and take them with you. The following articles show you how to use TrueCrypt in Windows and on the Mac and how to protect a flash drive using TrueCrypt.
Getting Started with TrueCrypt (to Secure Your Data)
Getting Started with TrueCrypt Drive Encryption on Mac OS X
How to Protect Your Flash Drive Data with TrueCrypt
Image via LadiesGadgets
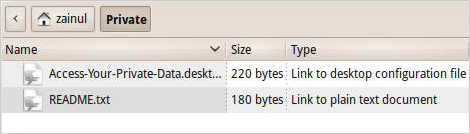
Securely Store Data on the Go
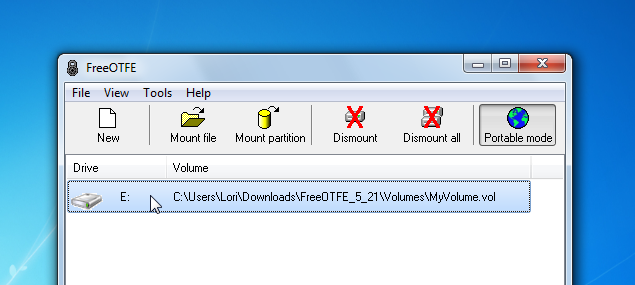
If you need to store files securely and take them with you, TrueCrypt allows you to do this with encrypted volumes. However, you must have administrator access on whatever computer you use to access your TrueCrypt encrypted volume. The following article describes another option, called FreeOTFE, that allows you to store files in an encrypted volume that can be accessed using a portable version of the program that can be used without administrative privileges.
Store Private Files Securely Using a Portable File Encryption Tool
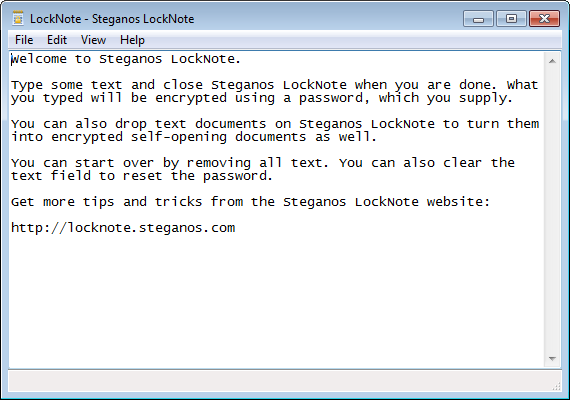
Encrypt Personal Information in a Simple Executable Text File
Steganos LockNote is a small, simple method for securely storing chunks of information in files. For example, if you purchase a download-only program, you can use LockNote to store the product key or serial number that goes with that program in the same folder, so you always know where to find it. The following article shows you how simple it is to use LockNote to easily and securely store bits of information and take it with you.
Encrypt Your Personal Information with Steganos LockNote
Hide Personal Information Inside an Image File
Another method of securing data is to hide it inside an image file. The following article shows you how to use a free tool, called Free File Camouflage, to hide a file inside an image file protected with a password. The image file is still an image file. The only thing that changes is the size of the file.
How to Encrypt and Hide Your Personal Files Inside of a Photo
Secure Your Linux PC
If you're using Ubuntu Linux on your PC, you can encrypt your Ubuntu installation partition to protect your data from hackers, nosy friends and family, or other intruders. The following article shows you how to encrypt a partition into which you can install Ubuntu, how to encrypt a folder, and how to create a hidden volume using TrueCrypt.
How to Secure Your Linux PC by Encrypting Your Hard Drive
Securely Sync Your Files Using Dropbox and SecretSync
Have you wanted to use cloud storage, but have been hesitant to because of the security risks? Dropbox is a leading option for cloud storage. It's simple to use and affordably priced. However, Dropbox users do not have access to the encryption keys for their accounts. Dropbox can decrypt your information and, for example, hand the files over to the government, if asked. You can manually encrypt your files using TrueCrypt before uploading them to Dropbox, but SecretSync provides an automated process. SecretSync locally encrypts your files before they are synced to your Dropbox account. The following article shows you how to set up Dropbox and SecretSync.
Sync Encrypted Files with Dropbox and SecretSync
Securely Delete Your Data
Part of keeping your data secure is making sure deleted data is permanently gone. You might think that once you delete a file it's gone. However, deleting a file only removes the reference to the file in the file system table. The file still exists on disk and can potentially be recovered. To permanently delete a file, you must overwrite it with other data, making it unreadable. The following article describes several tools available out there that provide methods of securely deleting files. Some of the tools are portable, allowing you to stay safe when using files on public computers.
Learn How to Securely Delete Files in Windows
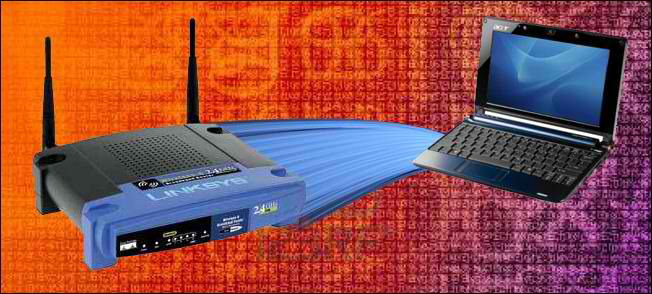
Securing Your Wi-Fi Network
Securing your Wi-Fi network is an important part of keeping your data secure. If your network is not secure, people can access your network and get to the files on your computer, as well as hijack your internet connection and possibly use it to do illegal things. The following articles show you how to secure your home Wi-Fi network against intrusion and also how to configure your router to support a secure, encrypted tunnel between your laptop and your home router so you can safely surf the internet from public Wi-Fi spots.
How To Secure Your Wi-Fi Network Against Intrusion
Setup SSH on Your Router for Secure Web Access from Anywhere
Protecting Login Information Using LastPass
Most of us have many user names and passwords for the various sites we regularly log into. How do you remember all of them? LastPass is a great option for securely storing your login information for websites, as well as other personal information. You can also use LastPass to enter your login information on websites automatically. The following articles show you how to use LastPass to store and use your private information, how to download and view information stored in your LastPass account offline, and how to install LastPass into the Opera browser.
The How-To Geek Guide to Getting Started with LastPass
Keep Those Hard to Remember Card Numbers Available and Secure with LastPass
Use a Free, Portable Tool to View your Passwords from Your LastPass Account Offline
Protecting Passwords and Other Data Offline Using KeePass
Storing private data in LastPass is useful, especially for logging into websites automatically and securely. However, if you want to be able to store many kinds of private information securely and take it with you offline, KeePass is a great option. It is portable and allows you to securely store different types of private information. The LastPass Portable tool mentioned in the previous tip, only allows you to view your information. If you change anything, the changes are lost once you exit LastPass Portable and you can't upload any changes to your LastPass account. KeePass allows you to add, remove, and change your private information and keep it secure offline.
Securely Store Your Passwords with KeePass
How To Import Your Saved Browser Passwords Into KeePass
Install KeePass Password Safe on Your Ubuntu or Debian-Based Linux System
Now that we showed you how to keep your private data secure, here are some tips about creating secure passwords for your online accounts, home Wi-Fi network, and other places where a secure password is crucial.
10 Ways to Generate a Random Password from the Command Line
There are also password generation tools on the Gibson Research Corporation website (www.grc.com), run by Steve Gibson, security guru and privacy expert. His Perfect Passwords page generates long, high-quality random passwords using three different sets of characters. Passwords generated on this page are completely unique and will never be produced again. If you need a one-time password, Steve's Perfect Paper Passwords page provides a free, simple, safe, and secure method of generating a convenient card of passcodes each of which is meant to be used one time only.
Steve also publishes a podcast called Security Now with Leo Laporte from TWiT TV (www.twit.tv). Archives of all the Security Now podcasts, back to the first one in August 2005, can be found at http://www.grc.com/securitynow.htm.