
Taylor Gibb
Contributing since August, 2011
-
257articles
Page 3
About Taylor Gibb
Taylor Gibb is a Microsoft MVP and all round geek, he loves everything from Windows 8 to Windows Server 2012 and even C# and PowerShell. You can also follow him on Google+
Latest Articles

How to Enable Two-Step Authentication For Increased Security on Windows 8 and the Web
Microsoft recently rolled out two-factor authentication for Windows Live accounts, and here’s how to enable it.

How to Save Time by Using Snapshots in VirtualBox
Snapshots are a massive time saver when you are testing settings and configuration for your Geek School testing.

How to Create a Test Lab So That You Can Follow the Geek School (Without Breaking Your PC)
Our Geek School articles can get pretty complicated, and there's no reason to do a ton of crazy stuff on your own desktop PC.

How to Change Outlook 2013's Default Save Location on Windows
By default, when you use the save as… option to save e-mail messages and attachments in Outlook the items are saved in your My Documents folder.
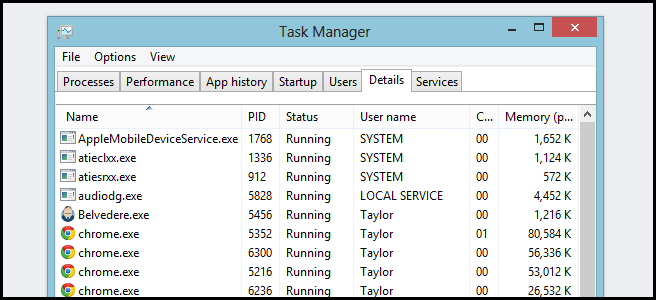
How to Kill a Process From the CLI in Windows
Sure, anybody can end a process from the Task Manager, but did you know you can also do it from the command line?How to Kill a Process From the CLI in WindowsIf the command prompt is your flavor of tea, you will need to know to know the name of the process you are trying to kill beforehand.
Geek School: Writing Your First Full PowerShell Script
A few weeks ago, The Geek showed you how you can use the command prompt to find when your computer was started up last.
Geek School: Learning PowerShell Variables, Input and Output
As we move away from simply running commands and move into writing full blown scripts, you will need a temporary place to store data.
Geek School: Learn How to Use Jobs in PowerShell
PowerShell has four types of jobs - Background Jobs, Remote Jobs,WMI Jobs and Scheduled Jobs.
How to Use PowerShell to Detect Logins and Alert Through Email
The Windows Task Scheduler can automatically send email at a specific time or in response to a specific event, but its integrated email feature won’t work very well for most users.
Geek School: Using PowerShell to Get Computer Information
WMI and its newer brother CIM can both be used to manage the Windows machines in your environment.
Geek School: Learn to Use Remoting in PowerShell
One of the best features PowerShell offers is the ability to remotely manage your Servers.
Geek School: Learning Formatting, Filtering and Comparing in PowerShell
In this edition of Geek School, we look at formatting, filtering and comparing objects in the Pipeline.
Geek School: Learning How to Use Objects in PowerShell
Understanding objects is one of the fundamental concepts to “getting” PowerShell.
Geek School: Learning to Use Cmdlets in PowerShell
If you have used ipconfig or ping through the command prompt, you’re halfway to becoming a PowerShell ninja.

How to Import Your Google Reader RSS Feeds into Outlook
There are plenty of articles about Google Reader alternatives, but did you know you can use your favorite email client to read your RSS feeds as well?How to Import Your Google Reader RSS Feeds into OutlookThe first thing you will need to do is export your feeds.
Geek School: Learn How to Automate Windows with PowerShell
In this edition of Geek School, we will be helping you understand the powerful PowerShell scripting language that is built right into Windows, and is extremely useful to know in an IT environment.
Geek School: Learning Windows 7 - Backup and Recovery
In this installation of Geek School we take a look at our options for Backup and Recovery.
Geek School: Learning Windows 7 - Resource Access
In this installation of Geek School, we take a look at Folder Virtualization, SIDs and Permission, as well as the Encrypting File System.
