
Chris Hoffman
Contributing since August, 2010
-
2888articles
Page 34
About Chris Hoffman
Chris Hoffman is the former Editor-in-Chief of How-To Geek. Chris has personally written over 2,000 articles that have been read more than one billion times---and that's just here at How-To Geek.
With over a decade of writing experience in the field of technology, Chris has written for a variety of publications including The New York Times, Reader's Digest, IDG's PCWorld, Digital Trends, and MakeUseOf. Beyond the web, his work has appeared in the print edition of The New York Times (September 9, 2019) and in PCWorld's print magazines, specifically in the August 2013 and July 2013 editions, where his story was on the cover. He also wrote the USA's most-saved article of 2021, according to Pocket.
Chris was a PCWorld columnist for two years. He founded PCWorld's "World Beyond Windows" column, which covered the latest developments in open-source operating systems like Linux and Chrome OS. Beyond the column, he wrote about everything from Windows to tech travel tips.
The news he's broken has been covered by outlets like the BBC, The Verge, Slate, Gizmodo, Engadget, TechCrunch, Digital Trends, ZDNet, The Next Web, and Techmeme. Instructional tutorials he's written have been linked to by organizations like The New York Times, Wirecutter, Lifehacker, the BBC, CNET, Ars Technica, and John Gruber's Daring Fireball. His roundups of new features in Windows 10 updates have been called "the most detailed, useful Windows version previews of anyone on the web" and covered by prominent Windows journalists like Paul Thurrott and Mary Jo Foley on TWiT's Windows Weekly. His work has even appeared on the front page of Reddit.
Articles he's written have been used as a source for everything from books like Team Human by Douglas Rushkoff, media theory professor at the City University of New York's Queens College and CNN contributor, to university textbooks and even late-night TV shows like Comedy Central's @midnight with Chris Hardwick.
Starting in 2015, Chris attended the Computer Electronics Show (CES) in Las Vegas for five years running. At CES 2018, he broke the news about Kodak's "KashMiner" Bitcoin mining scheme with a viral tweet. A wave of negative publicity ensued, with coverage on BuzzFeed News, CNBC, the BBC, and TechCrunch. The company's project was later reportedly shut down by the U.S. Securities and Exchange Commission.
In addition to his extensive writing experience, Chris has been interviewed as a technology expert on TV news and radio shows. He gave advice on dark web scans on Miami's NBC 6, discussed Windows XP's demise on WGN-TV's Midday News in Chicago, and shared his CES experiences on WJR-AM's Guy Gordon Show in Detroit.
Chris also ran MakeUseOf's email newsletter for two years. Nearly 400,000 subscribers received the newsletter complete with a handwritten tip every day.
Latest Articles
Windows 10 Will Let You Load a Custom Linux Kernel
Microsoft already added a Linux kernel to Windows. Now, you can load your own custom Linux kernel in Windows 10's WSL environment.

What’s New in Chrome 76, Available Now
Chrome 76 arrives next week. Some big changes: Flash is now disabled by default. And websites won't be able to detect and block incognito mode anymore.

Free Download: Remove PC Bloatware With Malwarebytes AdwCleaner
The latest version of AdwCleaner now removes PC bloatware in addition to adware and PUPs. (As always, this Malwarebytes tool is still completely free.)

How to Print Web Pages Without Ads and Other Clutter
Ever wanted to print a web page without all the ads and other clutter? You can do it with a feature built into your web browser.
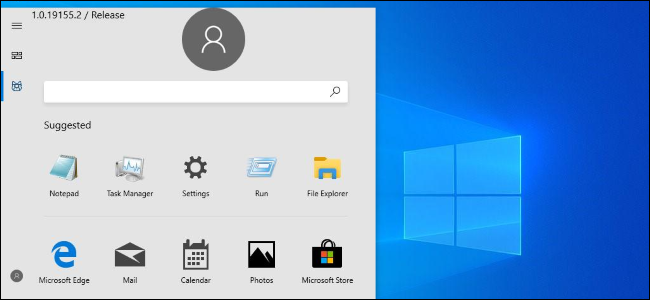
Microsoft Just Leaked a New Start Menu. Which Do You Prefer?
Microsoft accidentally leaked a new Start menu design. Do you like it better than the current one?
No, You Don't Need to Uninstall VLC
The VLC flaw isn't reproducible according to VLC's developers. VLC is fine.
Windows 10 Now Lets You Reply to Your Android Notifications
Windows 10 will let you reply directly to your Android phone's notifications.

How to Enable Text Prediction for a Hardware Keyboard on Windows 10
Windows 10 supports predictive text (or text suggestions)---even for hardware keyboards! Here's how to enable it.

How to Reboot Your Router and Modem
Rebooting your router and modem is a critical troubleshooting step when you have network problems. Here's how to do it.

How to Mirror and Control Your Android Phone on Any Windows PC
With just a USB cable and this free program, you can mirror any Android phone's screen to your PC---and remote-control it, too!
How to Disable Twitter's "News For You" Notifications
Here's how to stop Twitter from sending "News for You" notifications to your phone.

How to Fix a Frozen Windows PC
Windows PCs can freeze for many reasons. Here's how to recover a frozen PC---and how to stop future freezes.

Update Your Logitech Wireless Dongle Right Now
If you use a Logitech wireless mouse or keyboard, you need to update your USB dongle (unifying receiver) to keep your PC or Mac safe. Here's how.
Alexa Could Come to Windows 10's Lock Screen
Move over, Cortana: Windows 10 will enable Alexa and other voice assistants on the lock screen.
Windows 7's July 2019 Security Patch Includes Telemetry
Windows 7's July 2019 "security-only" patch includes telemetry---the "Compatibility Appraiser." Microsoft won't say why.

How to Disable Touch Screen Feedback Circles on Windows 10
Windows 10 shows transparent circles whenever you tap your PC's touch screen. Here's how to disable the touch feedback option, if you'd rather not see those circles.

Why Does Windows Still Use Letters for Drives?
Why does Windows still use drive letters? After all, macOS and Linux don't. (And yes, you can even mount drives at directory locations---Unix style---on modern versions of Windows.)

How to See if Zoom Is Running a Secret Web Server on Your Mac (and Remove It)
If you've ever installed Zoom, it's running a secret web server in the background on your Mac---even if you've uninstalled it! Here's how to check---and remove it.
How to Disable Dynamic Emails in Gmail
Gmail enabled "Dynamic Email" for everyone on July 2. If you just want traditional non-dynamic emails, here's how to disable it.
How to See the Applications Using Your Network on Windows 10
Here's how to see which applications are using your Windows PC's network connection right now---or at any time in the last 30 days.
