
Chris Hoffman
Contributing since August, 2010
-
2888articles
Page 23
About Chris Hoffman
Chris Hoffman is the former Editor-in-Chief of How-To Geek. Chris has personally written over 2,000 articles that have been read more than one billion times---and that's just here at How-To Geek.
With over a decade of writing experience in the field of technology, Chris has written for a variety of publications including The New York Times, Reader's Digest, IDG's PCWorld, Digital Trends, and MakeUseOf. Beyond the web, his work has appeared in the print edition of The New York Times (September 9, 2019) and in PCWorld's print magazines, specifically in the August 2013 and July 2013 editions, where his story was on the cover. He also wrote the USA's most-saved article of 2021, according to Pocket.
Chris was a PCWorld columnist for two years. He founded PCWorld's "World Beyond Windows" column, which covered the latest developments in open-source operating systems like Linux and Chrome OS. Beyond the column, he wrote about everything from Windows to tech travel tips.
The news he's broken has been covered by outlets like the BBC, The Verge, Slate, Gizmodo, Engadget, TechCrunch, Digital Trends, ZDNet, The Next Web, and Techmeme. Instructional tutorials he's written have been linked to by organizations like The New York Times, Wirecutter, Lifehacker, the BBC, CNET, Ars Technica, and John Gruber's Daring Fireball. His roundups of new features in Windows 10 updates have been called "the most detailed, useful Windows version previews of anyone on the web" and covered by prominent Windows journalists like Paul Thurrott and Mary Jo Foley on TWiT's Windows Weekly. His work has even appeared on the front page of Reddit.
Articles he's written have been used as a source for everything from books like Team Human by Douglas Rushkoff, media theory professor at the City University of New York's Queens College and CNN contributor, to university textbooks and even late-night TV shows like Comedy Central's @midnight with Chris Hardwick.
Starting in 2015, Chris attended the Computer Electronics Show (CES) in Las Vegas for five years running. At CES 2018, he broke the news about Kodak's "KashMiner" Bitcoin mining scheme with a viral tweet. A wave of negative publicity ensued, with coverage on BuzzFeed News, CNBC, the BBC, and TechCrunch. The company's project was later reportedly shut down by the U.S. Securities and Exchange Commission.
In addition to his extensive writing experience, Chris has been interviewed as a technology expert on TV news and radio shows. He gave advice on dark web scans on Miami's NBC 6, discussed Windows XP's demise on WGN-TV's Midday News in Chicago, and shared his CES experiences on WJR-AM's Guy Gordon Show in Detroit.
Chris also ran MakeUseOf's email newsletter for two years. Nearly 400,000 subscribers received the newsletter complete with a handwritten tip every day.
Latest Articles

USB Type A Connector: Everything You Need to Know
USB Type-A is still the most common type of USB connection you'll see in the real world. Here's what you need to know---and what the future holds.
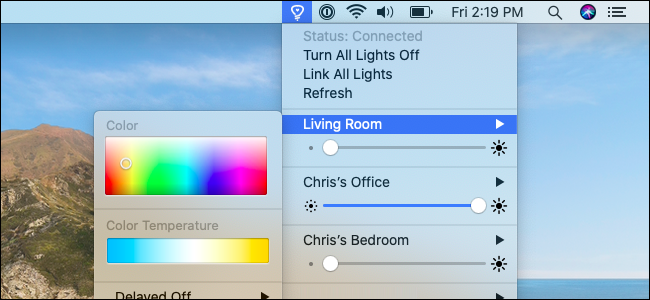
How to Control Philips Hue Lights From Your Mac
Do you have Hue lights and a Mac? Here's how to control your lights right from your Mac's desktop.
Windows Me, 20 Years Later: Was It Really That Bad?
Twenty years ago, Microsoft released Windows Me. Here's why it's remembered as one of the worst Windows releases of all time.

Windows 10's Settings App Is Really Pushing Microsoft Edge
Microsoft really, really wants you to switch to Microsoft Edge. Windows 10's Settings app is about to start pushing it hard.
How to Insert Emoji in Microsoft Word Documents 📝
Want to use emoji in any Word document? It's easy---here's how.

42+ Text-Editing Keyboard Shortcuts That Work Almost Everywhere
Whether you’re typing an email in your browser or writing in a word processor, there are convenient keyboard shortcuts usable in almost every application.

How to Manage Startup Programs on Ubuntu Linux
Many programs set themselves to automatically start with your Ubuntu desktop. Here's how to take control---and how to add your own custom programs.
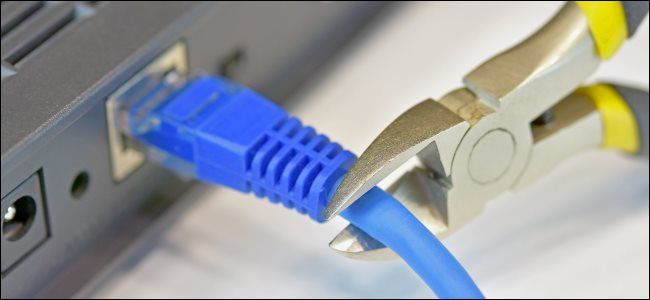
The Ultimate Defense: What Is an Air Gapped Computer?
"Air gapped" computers have almost complete protection from all networked threats... because they're not connected to a network.

How to Stop Skype From Starting Automatically on Windows 10
You can't close it like a traditional app, but you can hide or uninstall it.

How to Disable Store App Update Notifications on Windows 10
Are you tired of Windows 10's app update notifications? Here's how to turn them off.
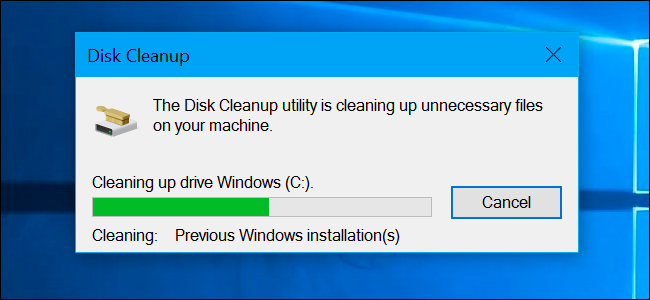
Is It Safe to Delete Everything in Windows' Disk Cleanup?
The Disk Cleanup tool included with Windows can quickly erase various system files and free up disk space.

Why You Should Update All Your Software
Updates may sometimes be painful, but they're necessary to keep your devices and data secure on a dangerous internet.

Can Zoom Hosts Really See All Your Private Messages?
Zoom meeting hosts can't see the private messages you send during meetings... but there are some ways your private messages could leak out. Here's what you need to know.
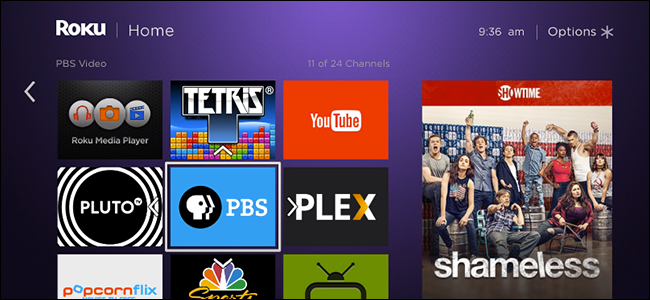
Can You Disable Ads on the Roku Home Screen?
Wondering if there's a way to disable the ads on your Roku? Well, no... but also yes. Here's what you need to know.
How to See How Much Money You've Spent on Steam Games
How much have you spent on Steam games over your lifetime? Valve tracks every penny. Here's how you can see the running tally.
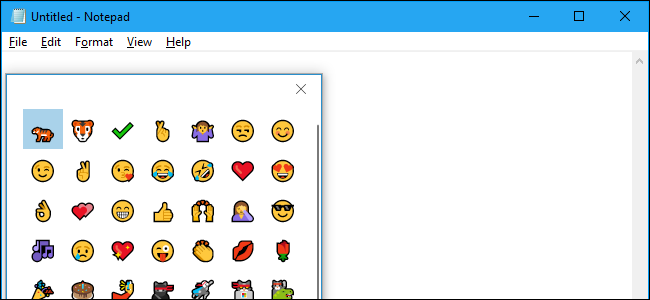
Secret Hotkey Opens Windows 10's New Emoji Picker in Any App
Windows 10 has a hidden emoji picker you can use to type emoji in any application, even desktop programs like Google Chrome.
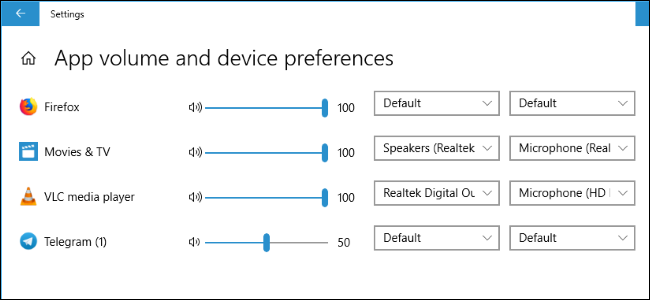
How to Set Per-App Sound Outputs in Windows 10
Windows 10 now lets you choose which sound output and input devices individual apps use.

How to Keep the Task Manager's CPU Stats In Your System Tray
Windows 10 has a CPU usage meter you can see in your system tray. It's part of the Task Manager---here's how to set it up.

How to Lock Your Windows PC After Signing In Automatically
Want to sign into your PC automatically so programs start when you boot up---while also requiring a password? Here's how to do it.

How to Troubleshoot the Windows Search Indexer on Windows 10
Microsoft's new Indexer Diagnostics tool provides insights into the inner workings of Windows 10's search function. It can help you troubleshoot high CPU usage and other search problems, too.
