
Chris Hoffman
Contributing since August, 2010
-
2888articles
Page 17
About Chris Hoffman
Chris Hoffman is the former Editor-in-Chief of How-To Geek. Chris has personally written over 2,000 articles that have been read more than one billion times---and that's just here at How-To Geek.
With over a decade of writing experience in the field of technology, Chris has written for a variety of publications including The New York Times, Reader's Digest, IDG's PCWorld, Digital Trends, and MakeUseOf. Beyond the web, his work has appeared in the print edition of The New York Times (September 9, 2019) and in PCWorld's print magazines, specifically in the August 2013 and July 2013 editions, where his story was on the cover. He also wrote the USA's most-saved article of 2021, according to Pocket.
Chris was a PCWorld columnist for two years. He founded PCWorld's "World Beyond Windows" column, which covered the latest developments in open-source operating systems like Linux and Chrome OS. Beyond the column, he wrote about everything from Windows to tech travel tips.
The news he's broken has been covered by outlets like the BBC, The Verge, Slate, Gizmodo, Engadget, TechCrunch, Digital Trends, ZDNet, The Next Web, and Techmeme. Instructional tutorials he's written have been linked to by organizations like The New York Times, Wirecutter, Lifehacker, the BBC, CNET, Ars Technica, and John Gruber's Daring Fireball. His roundups of new features in Windows 10 updates have been called "the most detailed, useful Windows version previews of anyone on the web" and covered by prominent Windows journalists like Paul Thurrott and Mary Jo Foley on TWiT's Windows Weekly. His work has even appeared on the front page of Reddit.
Articles he's written have been used as a source for everything from books like Team Human by Douglas Rushkoff, media theory professor at the City University of New York's Queens College and CNN contributor, to university textbooks and even late-night TV shows like Comedy Central's @midnight with Chris Hardwick.
Starting in 2015, Chris attended the Computer Electronics Show (CES) in Las Vegas for five years running. At CES 2018, he broke the news about Kodak's "KashMiner" Bitcoin mining scheme with a viral tweet. A wave of negative publicity ensued, with coverage on BuzzFeed News, CNBC, the BBC, and TechCrunch. The company's project was later reportedly shut down by the U.S. Securities and Exchange Commission.
In addition to his extensive writing experience, Chris has been interviewed as a technology expert on TV news and radio shows. He gave advice on dark web scans on Miami's NBC 6, discussed Windows XP's demise on WGN-TV's Midday News in Chicago, and shared his CES experiences on WJR-AM's Guy Gordon Show in Detroit.
Chris also ran MakeUseOf's email newsletter for two years. Nearly 400,000 subscribers received the newsletter complete with a handwritten tip every day.
Latest Articles

What Is "Antimalware Service Executable" and Why Is It Running on My PC?
Why is Microsoft Defender running a process in the background on my PC?

Why Windows 11's Best Feature Is New Emoji (Seriously)
Windows 11's best feature is new emoji. We'll show you why.
Windows 11's Tiny Context Menu Buttons Will Confuse People
Take it from us: Windows 11's context menu buttons are going to confuse people.

Why You Should Use Multiple Web Browsers
Are you just using one web browser? Adding another browser can make your online life better.

How to Stop Apple from Scanning Your iPhone Photos
Are you uncomfortable with the privacy implications of Apple's new iPhone photo-scanning feature? There's one way to opt out.

Apple Discusses "Screeching Voices of the Minority" in Internal Memos
Are we screeching loud enough for you to hear us yet, Apple?

Windows 11 Makes It Hard to Change Your Default Web Browser
Want to change Windows 11's default web browser? Microsoft makes the process long and confusing.

Did You Know? Windows Has Never Had a "System Tray"
Windows has never had a "system tray." For 25 years, we've all been calling it the wrong name. So where did the term "system tray" came from? And why does Windows 10 call it the "system tray"---but only once? Let's talk Windows.

What Is the Steam Deck, and Should You Buy One?
Valve just announced the Steam Deck. Picture the Nintendo Switch.... as a PC.
What Is Windows 365, and Is It Secure?
With Windows 365, Microsoft will offer Windows desktop PCs in the cloud.

Go Like This Tweet So Microsoft Will Resurrect Clippy
Clippy could be making a comeback--with your help.
Microsoft Announces Windows 365: a Desktop PC in the Cloud
Introducing Windows 365: Now you can run Windows without actually running Windows.

Why Wi-Fi Channels 12, 13, and 14 Are Illegal in the USA
Wireless routers have fourteen different channels they can use for 2.

Tell Your Relatives: No, Microsoft Won't Call You About Your Computer
"Hi, I'm from Microsoft and we've noticed your computer has a lot of viruses.

Windows 11 Finally Fixes File Explorer's Slow Context Menus
With File Explorer's new context menus, Windows 11 is fixing the mistakes of the past.

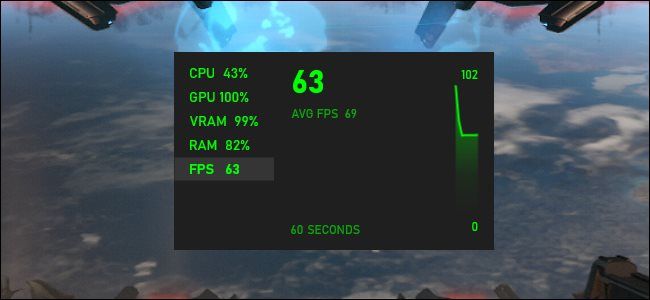
How to See FPS in Any Windows 10 Game (Without Extra Software)
Windows 10 has a built-in FPS meter for your PC games. Here's how to enable it.


