Chris Hoffman
Contributing since August, 2010
-
2888articles
Page 16
About Chris Hoffman
Chris Hoffman is the former Editor-in-Chief of How-To Geek. Chris has personally written over 2,000 articles that have been read more than one billion times---and that's just here at How-To Geek.
With over a decade of writing experience in the field of technology, Chris has written for a variety of publications including The New York Times, Reader's Digest, IDG's PCWorld, Digital Trends, and MakeUseOf. Beyond the web, his work has appeared in the print edition of The New York Times (September 9, 2019) and in PCWorld's print magazines, specifically in the August 2013 and July 2013 editions, where his story was on the cover. He also wrote the USA's most-saved article of 2021, according to Pocket.
Chris was a PCWorld columnist for two years. He founded PCWorld's "World Beyond Windows" column, which covered the latest developments in open-source operating systems like Linux and Chrome OS. Beyond the column, he wrote about everything from Windows to tech travel tips.
The news he's broken has been covered by outlets like the BBC, The Verge, Slate, Gizmodo, Engadget, TechCrunch, Digital Trends, ZDNet, The Next Web, and Techmeme. Instructional tutorials he's written have been linked to by organizations like The New York Times, Wirecutter, Lifehacker, the BBC, CNET, Ars Technica, and John Gruber's Daring Fireball. His roundups of new features in Windows 10 updates have been called "the most detailed, useful Windows version previews of anyone on the web" and covered by prominent Windows journalists like Paul Thurrott and Mary Jo Foley on TWiT's Windows Weekly. His work has even appeared on the front page of Reddit.
Articles he's written have been used as a source for everything from books like Team Human by Douglas Rushkoff, media theory professor at the City University of New York's Queens College and CNN contributor, to university textbooks and even late-night TV shows like Comedy Central's @midnight with Chris Hardwick.
Starting in 2015, Chris attended the Computer Electronics Show (CES) in Las Vegas for five years running. At CES 2018, he broke the news about Kodak's "KashMiner" Bitcoin mining scheme with a viral tweet. A wave of negative publicity ensued, with coverage on BuzzFeed News, CNBC, the BBC, and TechCrunch. The company's project was later reportedly shut down by the U.S. Securities and Exchange Commission.
In addition to his extensive writing experience, Chris has been interviewed as a technology expert on TV news and radio shows. He gave advice on dark web scans on Miami's NBC 6, discussed Windows XP's demise on WGN-TV's Midday News in Chicago, and shared his CES experiences on WJR-AM's Guy Gordon Show in Detroit.
Chris also ran MakeUseOf's email newsletter for two years. Nearly 400,000 subscribers received the newsletter complete with a handwritten tip every day.
Latest Articles

How to Unblock "Potentially Sensitive Content" on Twitter
Tired of seeing the "Sensitive Content" warning on Twitter? Here's how to get rid of it.

Apple's Third-Generation AirPods Boast AirPods Pro Features
Apple just added a lot of AirPods Pro features to the standard AirPods.
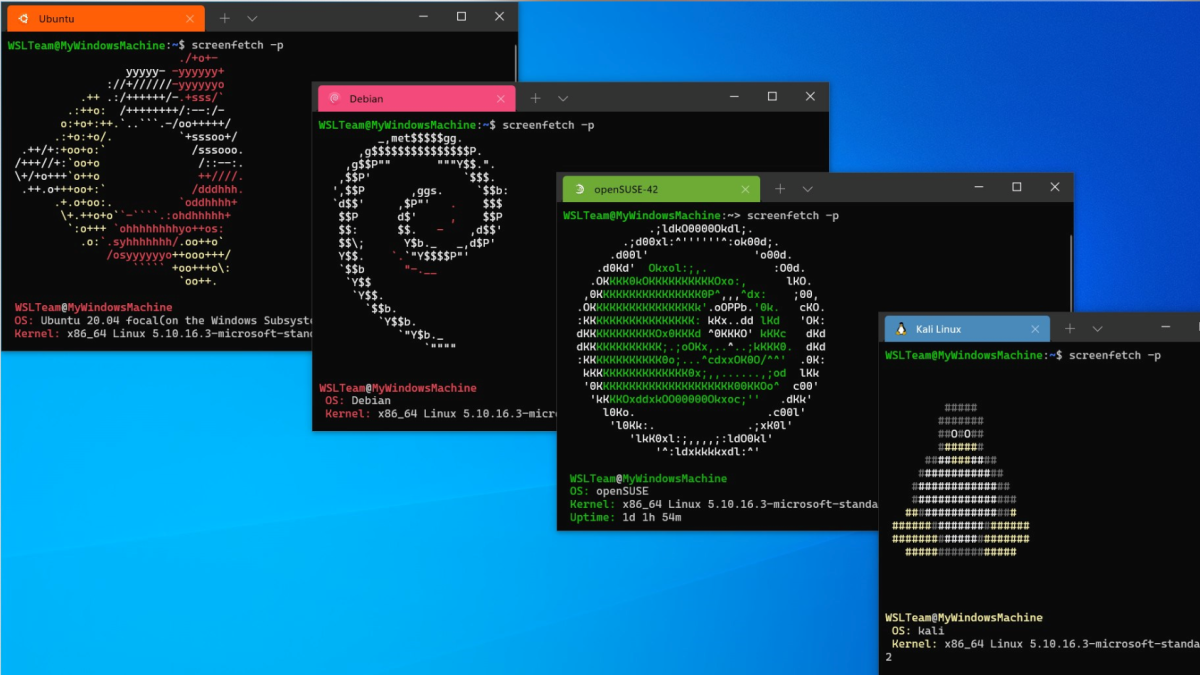
Windows 11's Windows Subsystem for Linux Gets Faster Updates
Want faster updates for Windows 11's Linux environment?

[Update: Mozilla Fixes Its Documentation] Firefox Now Sends Your Address Bar Keystrokes to Mozilla
Firefox now sends your keystrokes and location to Mozilla as you type in your address bar. Here's what you need to know.

How to Check if Your Windows 10 PC Can Run Windows 11
Can your PC run Windows 11? Here's how to find out!
Will Your Credit Score Be Based on Your Web History?
Researchers have proposed using your online search history as part of your credit score.


How to Wipe (Securely Erase) Your Devices Before Disposing of or Selling Them
Time for a new device?

What Is an Apple ProMotion Display?
Apple slaps their "ProMotion" branding on certain models of iPad and iPhone Pro, but what exactly does this mean?

How to Connect Your Mac to Any VPN (and Automatically Reconnect)
Macs have built-in support for connecting to the most common types of VPNs.
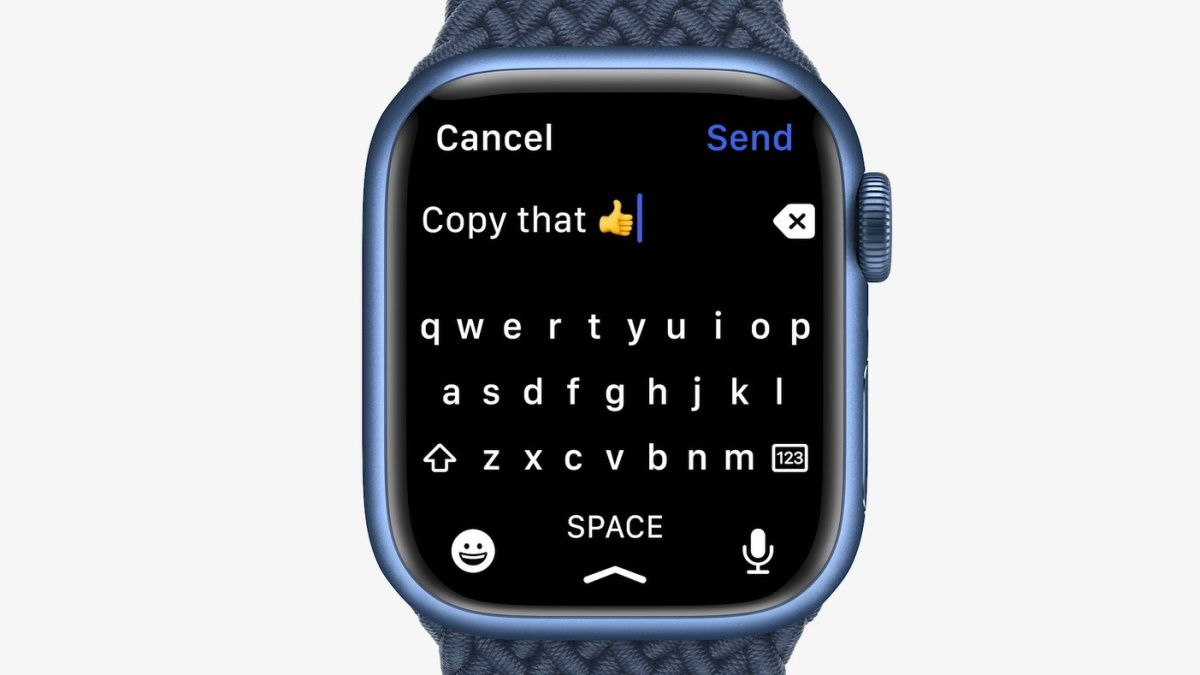
Apple Watch Series 7 Brings a Full Keyboard to Your Wrist
The new Apple Watch includes a full-size keyboard on its larger display.

How to Skip Back and Forward 10 Seconds in YouTube and Other Apps
The YouTube app has a hidden trick that lets you skip back and forward ten seconds. It works in Netflix and other apps, too.

How to Prepare a Computer, Tablet, or Phone Before Selling It
Everything you need to do before selling your electronics.
Do You Need to Update Your Computer's BIOS?
Just because there's an update for your BIOS doesn't mean you should install it.
How to Enable Dark Mode in YouTube
You don't have to enable system-wide dark mode on your device to enjoy the theme on YouTube.
How to Mute Individual Browser Tabs in Chrome, Safari, Firefox, and Edge
Do you regularly visit websites that play audio without your permission?

What Is "Antimalware Service Executable" and Why Is It Running on My PC?
Why is Microsoft Defender running a process in the background on my PC?

Why Windows 11's Best Feature Is New Emoji (Seriously)
Windows 11's best feature is new emoji. We'll show you why.