Quick Links
Phones get stolen or lost everyday. With a plethora of data ripe for identity-theft on it, a lost phone can easily make your blood run cold. Take a deep breath, How-To Geek will talk you through this.
It happened to me just last week. My iPhone 4 hadn’t left my sight in the year that I had it, but one tiny 5-second window of opportunity was all it took for a thief to snatch it up. Luckily for me, I was prepared enough to not worry about someone stealing my private information, but I knew I wasn’t seeing that phone ever again. If this happens to you, or you’re just prone to losing your phone, taking some precautionary steps will do you a world of good, but even if you weren’t entirely prepared, there may still be something you can do. Let’s look at the process step by step.
(Images by AndWat and davestone)
Step 1: Precautions to Take & First Resort Actions
Keeping Your Data Safe
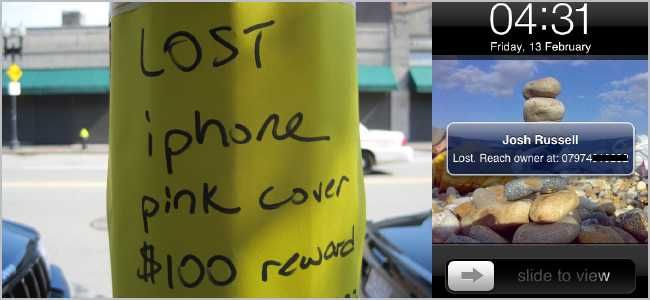
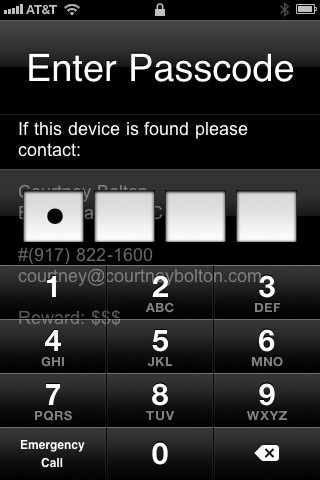
I have a few friends who lose their phones a lot. A simple step you can take is to make your lock-screen wallpaper your contact information – like your name, work info, an alternate phone number, and email – so if an honest person finds your phone they know how to get it back to you. Depending on where you are, this may be more or less likely to happen, but it definitely won’t hurt as long as you don’t leave extremely sensitive information (like your home address) available for those without good intentions.
(Image by courtneyBolton)
A little bit of precaution can go a long way towards safety, however. Android and iOS both have options for passcode-locking, and you can enable automatic wiping of your phone after several failed attempts. Even without this last option on, most thieves aren’t savvy enough to figure out how to bypass the locking mechanisms and access your data, so they’ll probably try to restore/reset your phone to factory defaults. This is a pretty solid measure you can take to prevent someone from getting into your phone and stealing data right away, but it also decreases the likelihood of you getting your phone back.
Locating Your iOS or Android Device
If you have a newer Apple device and you’re updated to iOS 4.2.1 or later, then you can use the Find My iPhone feature for free without a MobileMe subscription. Once you have it installed, you can log in online and see where your phone is via its GPS coordinates. GadgetTrak is a $3.99 solution that can take photos of your thief and email them back to you in addition to the Find My iPhone features.
(Image by bizmac)
Jailbroken iOS products have Cylay, which does the same stuff as Find My iPhone and GadgetTrak, but can utilize commands received by text message (which are cloaked and hidden from the thief). iGotYa originally made a lot of waves in the jailbreak community because it had two unique features: the ability to take and send pictures of the thief, and a “fake-out” mode. This latter mode allowed the thief access to the device so that they’d be less likely to wipe or restore it right away, thus giving you more time to track and find him or her. It’s a bit of a gamble, considering they may be able to get your personal information, but you can also combine this with other recovery methods if your paranoia gets the better of you later on.
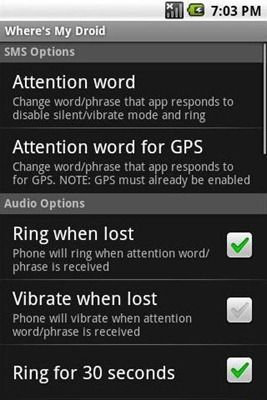
Android users have tons of options, too. Wheres My Droid is a good option. You can text your phone with a pre-arranged code-word and it will automatically turn on the GPS and send its coordinates and/or start the ringtone at full volume (regardless of volume/silent settings). Lookout is an antivirus and security app that offers a similar functionality to Wheres My Droid. The premium version lets you wipe your phone remotely, too. Some people have replicated these functions using Tasker instead of using apps or services. Actually, I recently found out that many Motorola devices like the Atrix use a version of MotoBlur that has a built-in “remote wipe” command, so you may not even need an extra app if your manufacturer has added this to your phone.
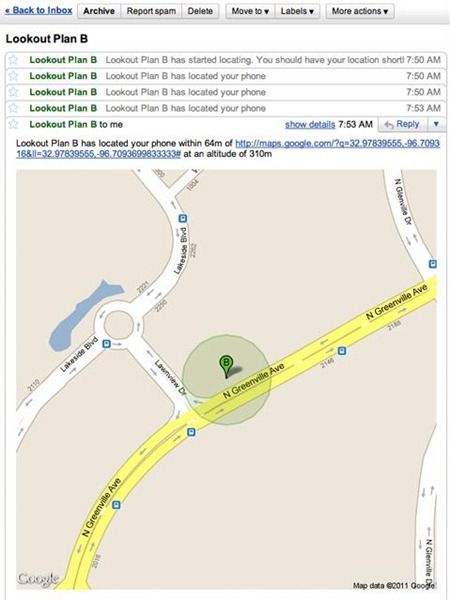
The makers of Lookout also make another app called Plan B. The beauty of Plan B is that you can install it even after your phone is gone and it will send you tracking updates with GPS coordinates by email. It’s also free, so there’s no reason not to try it.
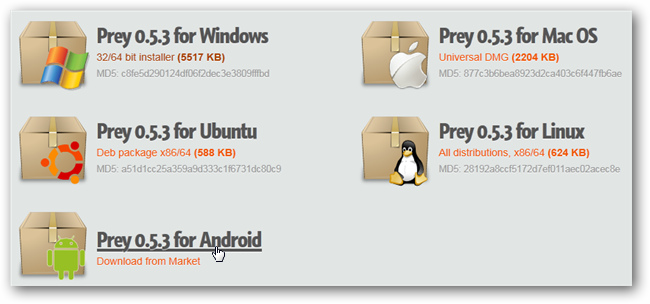
Lastly, there are services you can use. StuffBak (now ReturnMe) offers a way for someone who found your lost device to send it back to you safely and without a cost to them. You can even include a reward for the other person to sweeten the deal for them. Prey is an open-source project for Android phones and computers that will keep track of them for you, send you a picture of your thief, delete sensitive data, and more. There’s Linux compatibility, too, in case you run Ubuntu or Debian on your laptop. It’s definitely a great service and has a free option that works pretty well. Pro plans start at $5 a month (for up to 3 devices) and give you more features, like SSL encryption, and “Active” mode, and more reports per device.
These options give you a wide-range of flexibility in trying to locate and secure your lost or stolen phone. If you really need your phone back, though, you should hold off on wiping your data for now, as there are still things you can do.
Step 2: Round-about Methods
(Image by mrbill)
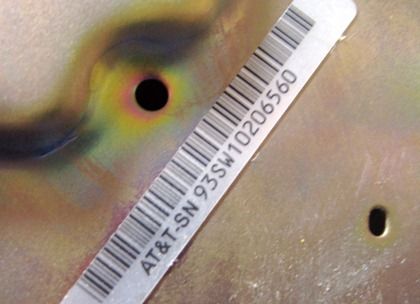
If you didn’t take proper preventative measures, you might be able to figure out how to locate or access your device in a different way. Latitude on both Android and iOS can be configured to update your location in the background, something you can lookup online. You can also log in to your carrier’s website and see if your thief made any phone calls or sent text messages to weird numbers. You can then record this as proof for the police if you ever find the perpetrator but get stuck in a “his-word-against yours” situation. If that happens, knowing your device’s IMEI/ESN/Serial number will also be very handy, all of which can be found on your device’s box.
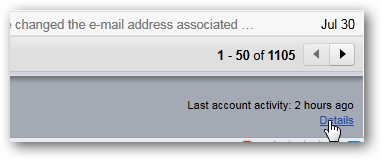
Gmail and some other online services record a list of IP addresses used to access your account. You may be able to use this to access your phone via another means, like SSH, and you can grab important data and/or wipe your phone clean that way. I was lucky enough to do this, though I had a DDNS client on my iPhone for a project I was working on, so that made finding my IP address much easier. If you sit and think about what kinds of services you have running and how you can track them from the web, you might be surprised to find out how easy it is to track your phone down.
Step 3: Damage Control
Legally speaking, if all you have is an IP address, there’s not much you can do to get your phone back. It normally takes time and more proof to get a subpoena for the IP from the ISP, and even then, there’s no guarantee that you’ll be able to nab your thief. To make matters worse, he or she probably will have sold your phone by then even if you can establish proof. Having a picture emailed to you and having records from your carrier’s website can really help speed up the process, but it may not be enough.
Phone thieves are usually clever enough to shut your phone off and switch out the SIM card before trying to use it again, which negates many of the protective measures we’ve discussed so far. If you have the ability to wipe your data and there’s no way to recover your phone, now is the time to do it.
If there is any doubt at all about your personal data, you should go ahead and change your passwords immediately. In fact, you should do it anyway because, hey, you never know. Change all passwords to any service that is connected to your phone automatically, like Gmail, PayPal, and your online banking account. Deny access to your device by services like Facebook, Twitter, etc. Lastly, once you have determined that your phone is definitely gone, you should report your phone as lost or stolen to your carrier so you can avoid being responsible for any charges that were racked up.
(Image by WIlliam Hook)
Verizon flags lost or stolen phones with “bad” ESNs, so they can’t be activated on their network again, though other carriers don’t necessarily do this (AT&T definitely doesn’t). You should also get a police report completed with your device’s serial number if you have insurance. Even if you don’t, it’s not a bad thing to do just in case something else comes up.
Step 4: Replacing Your Phone
Lastly, you’ll need to replace your device. Many carriers offer insurance on their devices, so if you have a police report and pay a deductible, you can get a replacement. I’ve also heard anecdotal stories of people getting discounts at Apple stores with sob stories and the like, but it hasn’t happened to me. When you report your phone as lost or stolen, your number is suspended so no one can use it. You’re still charged for it, though, per the contract you signed. If you walk-in to your carrier’s store, you might be surprised to find that you have an upgrade waiting for you. Some carriers allow partial discounts for upgrades due to customer loyalty or “annual” discounts, despite you still being on contract. You can also talk to a sales rep and see if you can “borrow” a family member’s upgrade option if you’re on a family plan.
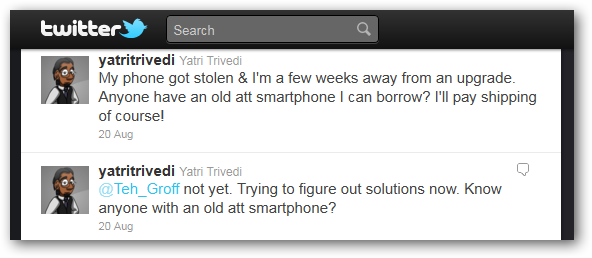
Phones off-contract are not cheap in the slightest, but be wary of buying used ones online. Many lost and stolen phones end up here, and there’s usually no guarantee that the phone you paid for will work (see previous section about Verizon flagging “bad” ESNs). Often, if you put out notice in your social circle that you need an older phone, someone will notice they have one laying around that you can use. It may not be the same as your awesome phone, but it’ll get you by until the next upgrade.
Losing your phone is tough, but we hope you’ll take the proper precautions to keep your data safe and possibly get your phone back easily. If not, it’s good to know that you have options and what steps you need to take to safeguard your personal accounts.
Have a favorite app or service we didn’t mention? Have a crazy “I lost my phone” or “I caught the thief who stole it” story? Share in the comments!