Quick Links
If you’ve been using Linux for some time (and even OS X) you’ll probably have come across a “permissions” error. But what exactly are they, and why are they necessary or useful? Let’s take an inside look.
User Permissions
Back in the day, computers were massive machines that were incredibly expensive. To make the most out of them, multiple computer terminals were hooked up which allowed many users to go about their business simultaneously. Data processing and storage was done on the machine, while the terminals themselves were little more than a means of viewing and inputting data. If you think about it, it’s pretty much how we access data on the “cloud”; look at Amazon’s Cloud MP3 system, Gmail, and Dropbox, and you’ll notice that while changes can be made locally, everything is stored remotely.
(Image: Zenith Z-19 “dumb” terminal; credit: ajmexico)
In order for this to work, individual users need to have accounts. They need to have a section of the storage area allotted to them, and they need to be allowed to run commands and programs. Everyone gets specific “user permissions,” which dictates what they can and cannot do, where on the system they do and do not have access, and whose files they can and cannot modify. Each user is also placed into various groups, which grant or restrict further access.
File Access
In this wacky multi-user world, we’ve already set up boundaries as to what users can do. But what about what they access? Well, every file has a set of permissions and an owner. The owner designation, typically bound when the file is created, declares which user it belongs to, and only that user can alter its access permissions.
In the world of Linux, permissions are broken down into three categories: read, write and execute. “Read” access allows one to view a file’s contents, “write” access allows one to modify a file’s contents, and “execute” allows one to run a set of instructions, like a script or a program. Each of these categories are applied to different classes: user, group, and world. “User” means the owner, “group” means any user who is in the same group as the owner, and “world” means anybody and everybody.
Folders can also be restricted with these permissions. You can, for example, allow other people in your group to view directories and files in your home folder, but not anyone outside of your group. You will probably want to limit “write” access to only yourself, unless you’re working on a shared project of some sort. You can also create a shared directory that allows anyone to view and modify files in that folder.
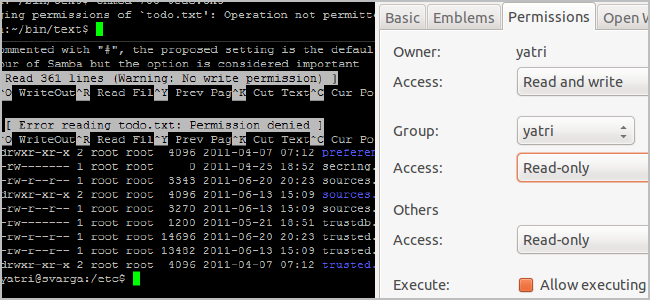
Changing Permissions in Ubuntu
GUI
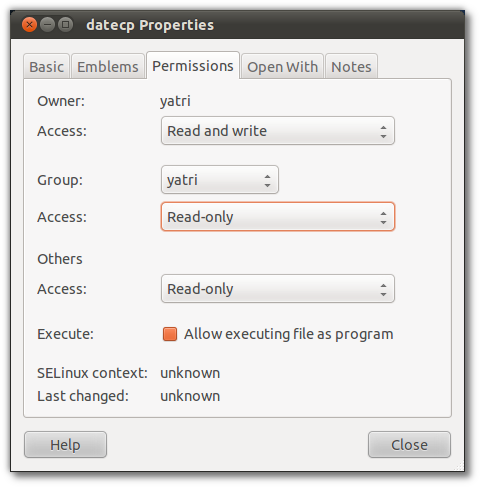
To change the permissions of a file you own in Ubuntu, just right-click the file and go to “Properties.”
You can change whether the Owner, Group, or Others can read and write, read only, or do nothing. You can also check a box to allow execution of the file, and this will enable it for the Owner, Group, and Others simultaneously.
Command-Line
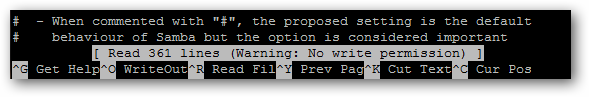
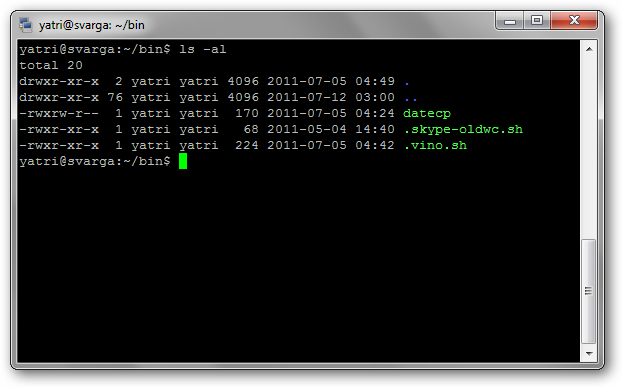
You can also do this via the command-line. Go to a directory that has files in it and type the following command to view all files in a list:
ls -al
Next to each file and directory, you’ll see a special section that outlines the permissions it has. It looks like this:
-rwxrw-r--
The r stands for “read,” the w stands for “write,” and the x stands for “execute.” Directories will be start with a “d” instead of a “-“. You’ll also notice that there are 10 spaces which hold value. You can ignore the first, and then there are 3 sets of 3. The first set is for the owner, the second set is for the group, and the last set is for the world.
To change a file or directory’s permissions, let’s look at the basic form of the chmod command.
chmod [class][operator][permission] file
chmod [ugoa][+ or –] [rwx] file
This may seem complicated at first, but trust me, it’s pretty easy. First, let’s look at the classes:
- u: This is for the owner.
- g: This is for the group.
- o: This is for all others.
- a: This will change permissions for all of the above.
Next, the operators:
- +: The plus sign will add the permissions which follow.
- -: The minus sign will remove the permissions which follow.
Still with me? And the last section is the same as when we checked the permissions of a file:
- r: Allows read access.
- w: Allows write access.
- x: Allows execution.
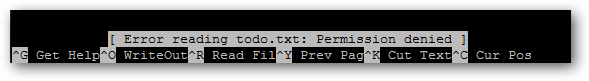
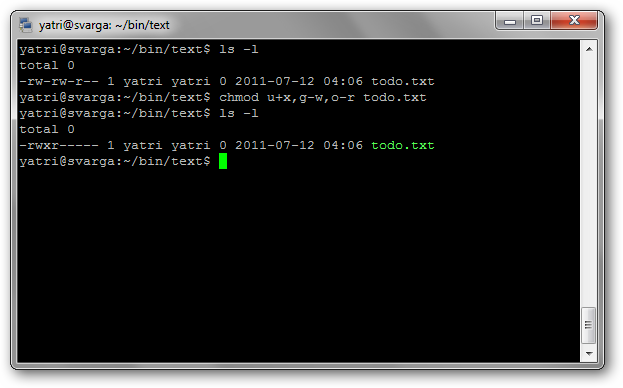
Now, let’s put it together. Let’s say we have a file named “todo.txt” that has the following permissions:
-rw-rw-r--
That is, the owner and group can read and write, and the world can only read. We want to change the permissions to these:
-rwxr-----
That is, the owner has full permissions, and the group can read. We can do this in 3 steps. First, we’ll add the execution permission for the user.
chmod u+x todo.txt
Then, we’ll remove the write permission for the group.
chmod g-w todo.txt
Lastly, we’ll remove the read permissions for all other users.
chmod o-r todo.txt
We can also combine these into one command, like so:
chmod u+x,g-w,o-r todo.txt
You can see that each section is separated by commas and there are no spaces.
Here are some useful permissions:
- -rwxr-xr-x : Owner has full permissions, group and other users can read file contents and execute.
- -rwxr--r-- : Owner has full permissions, group and other users can only read file (useful if you don’t mind others viewing your files.
- -rwx------ : Owner has full permissions, all others have none (useful for personal scripts).
- -rw-rw----: Owner and group can read and write (useful for collaboration with group members).
- -rw-r--r-- : Owner can read and write, group and other users can only read file (useful for storing personal files on a shared network).
- -rw------- : Owner can read and write, all others have none (useful for storing personal files).
There are a few other things you can do with chmod – like setuid and setgid – but they’re a little in-depth and most users won’t really need to use them anyway.
The Root or Super-User and System Files
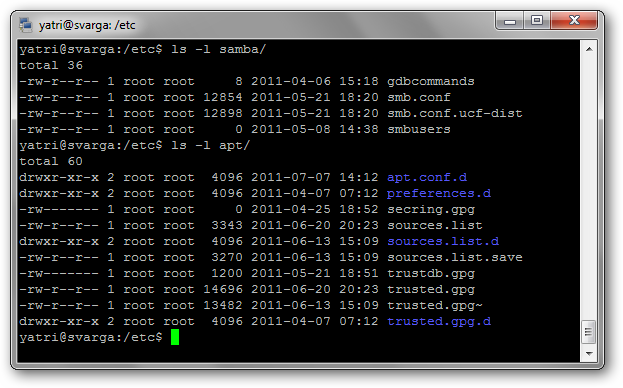
Nowadays, we don’t always run systems that have multiple users. Why should we still worry about permissions?
Well, Unix and its derivatives – Linux, OS X, among others – also distinguish between things run by the user, things run by an administrator or with admin privileges, and things run by the system itself. As such, things that are integral for the system need admin privileges to be changed or accessed. This way, you don’t mess up anything accidentally.
In Ubuntu, to make changes to system files you use “sudo” or “gksudo” to gain the equivalent of Administrator privileges. In other distros, you switch to “root” or the “super-user” which effectively does the same thing until you log out.
Be aware that in both of these circumstances, changing file permissions can lead to programs not working, unintentionally changing file ownership to the root user (instead of the owner), and making the system less secure (by granting more permissions). As such, it’s recommended you don’t change permissions for files – especially system files – unless it’s necessary or you know what you’re doing.
File permissions are in place to provide a basic system of security amongst users. Learning how they work can help you set up basic sharing in a multi-user environment, protect “public” files, and give you a clue as to when something goes wrong with system file ownership.
Think you can explain things easier? Have a correction? Want to reminisce about the old days? Take a break and put your thoughts down in the comments.