In this day and age, it is not a bad idea to be leery of untrusted executable files, but is there a safe way to run one on your Linux system if you really need to do so? Today's SuperUser Q&A post has some helpful advice in response to a worried reader's query.
Today’s Question & Answer session comes to us courtesy of SuperUser—a subdivision of Stack Exchange, a community-driven grouping of Q&A web sites.
The Question
SuperUser reader Emanuele wants to know how to safely run an untrusted executable file on Linux:
I have downloaded an executable file compiled by a third party and I need to run it on my system (Ubuntu Linux 16.04, x64) with full access to HW resources such as the CPU and GPU (through the NVIDIA drivers).
Suppose this executable file contains a virus or backdoor, how should I run it? Should I create a new user profile, run it, then delete the user profile?
How do you safely run an untrusted executable file on Linux?
The Answer
SuperUser contributors Shiki and Emanuele have the answer for us. First up, Shiki:
First and foremost, if it is a very high risk binary file, you would have to set up an isolated physical machine, run the binary file, then physically destroy the hard drive, the motherboard, and basically all the rest because in this day and age, even your robot vacuum can spread malware. And what if the program already infected your microwave through the computer's speakers using high-frequency data transmitting?!
But let's take off that tinfoil hat and jump back to reality for a bit.
No Virtualization - Quick to Use
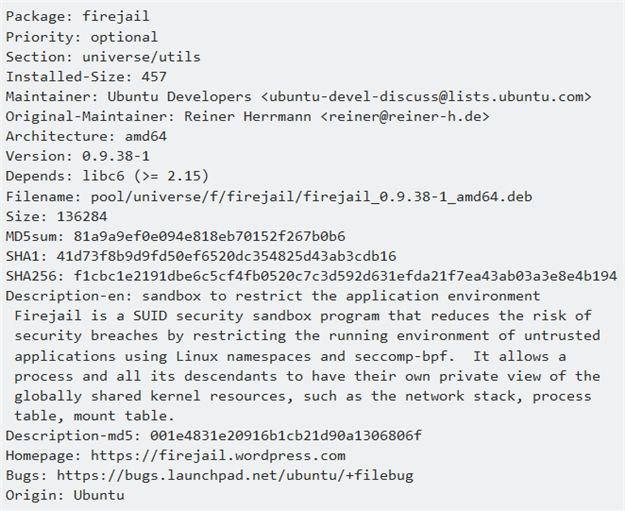
I had to run a similar untrusted binary file just a few days ago and my search led to this very cool small program. It is already packaged for Ubuntu, very small, and has virtually no dependencies. You can install it on Ubuntu using: sudo apt-get install firejail
Package info:
Virtualization
KVM or Virtualbox
This is the safest bet depending on the binary, but hey, see above. If it has been sent by "Mr. Hacker" who is a black belt, black hat programmer, there is a chance that the binary can escape a virtualized environment.
Malware Binary - Cost Saver Method
Rent a virtual machine! For example, virtual server providers like Amazon (AWS), Microsoft (Azure), DigitalOcean, Linode, Vultr, and Ramnode. You rent the machine, run whatever you need, then they will wipe it out. Most of the bigger providers bill by the hour, so it really is cheap.
Followed by the answer from Emanuele:
A word of caution. Firejail is OK, but one has to be extremely careful in specifying all the options in terms of the blacklist and whitelist. By default, it does not do what is cited in this Linux Magazine article. Firejail's author has also left some comments about known issues at Github.
Be extremely careful when you use it, it might give you a false sense of security without the right options.
Have something to add to the explanation? Sound off in the comments. Want to read more answers from other tech-savvy Stack Exchange users? Check out the full discussion thread here.
Image Credit: Prison Cell Clip Art (Clker.com)