Quick Links
In this installation of Geek School, we take a look at Folder Virtualization, SIDs and Permission, as well as the Encrypting File System.
Be sure to check out the previous articles in this Geek School series on Windows 7:
- Introducing How-To Geek School
- Upgrades and Migrations
- Configuring Devices
- Managing Disks
- Managing Applications
- Managing Internet Explorer
- IP Addressing Fundamentals
- Networking
- Wireless Networking
- Windows Firewall
- Remote Administration
- Remote Access
- Monitoring, Performance and Keeping Windows Up To Date
And stay tuned for the rest of the series all this week.
Folder Virtualization
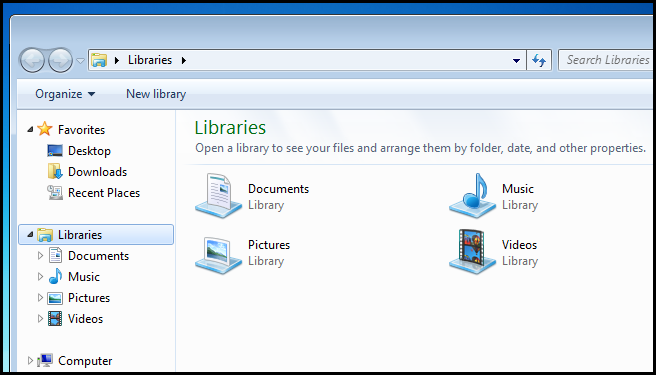
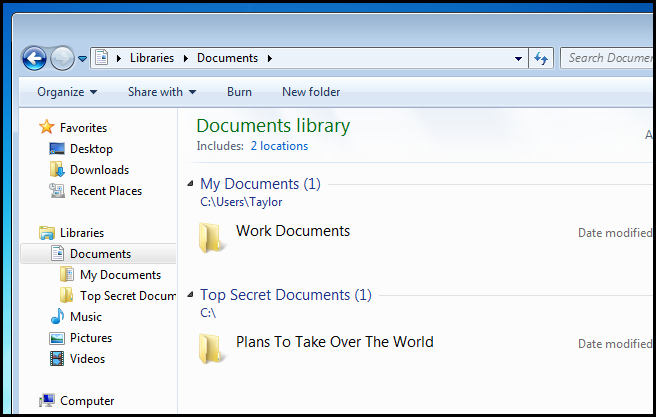
Windows 7 introduced the notion of libraries which allowed you to have a centralized location from which you could view resources located elsewhere on your computer. More specifically, the libraries feature allowed you to add folders from anywhere on your computer to one of four default libraries, Documents, Music, Videos and Pictures, which are easily accessible from the navigation pane of Windows Explorer.
There are two important things to note about the library feature:
- When you add a folder to a library the folder itself does not move, rather a link is created to the location of the folder.
- In order to add a network share to your libraries it must be available offline, though you could also use a work around using symbolic links.
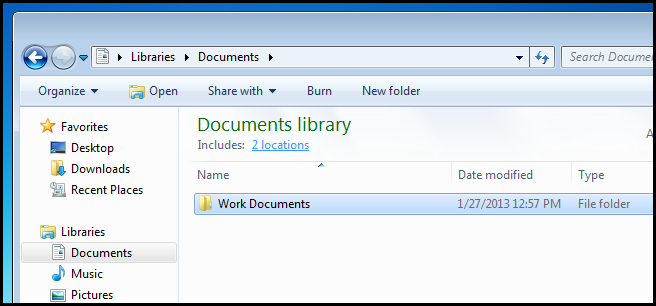
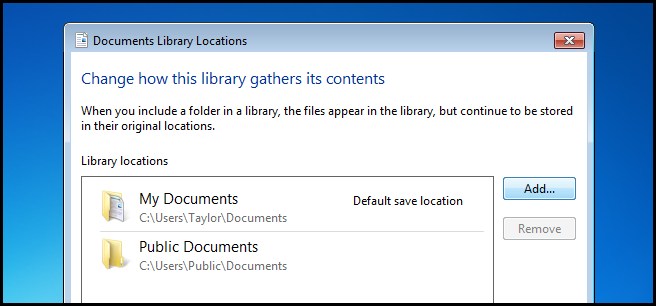
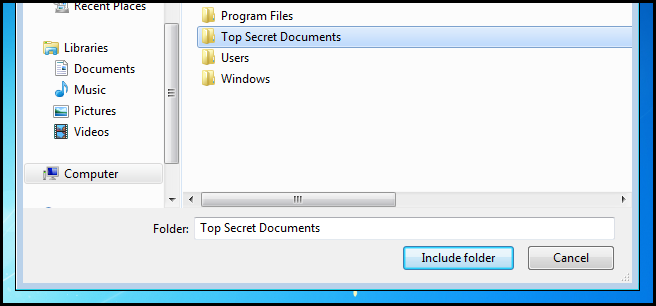
To add a folder to a library, simply head into the library and click on the locations link.
Then click the add button.
Now locate the folder you want to include in the library and click the Include folder button.
That’s all there is to it.
The Security Identifier
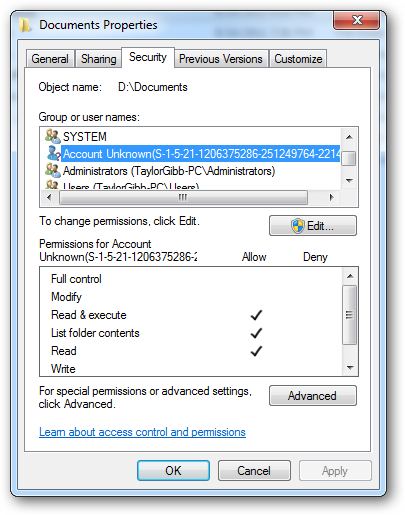
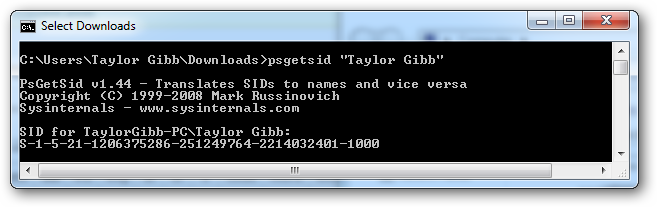
The Windows Operating system use SIDs to represent all security principles. SIDs are just variable length strings of alphanumeric characters that represent machines, users and groups. SIDs are added to ACLs(Access Control Lists) every time you grant a user or group permission to a file or folder. Behind the scenes, SIDs are stored the same way all other data objects are: in binary. However, when you see a SID in Windows, it will be displayed using a more readable syntax. It is not often that you will see any form of SID in Windows; the most common scenario is when you grant someone permission to a resource, then delete their user account. The SID will then show up in the ACL. So lets take a look at the typical format in which you will see SIDs in Windows.
The notation that you will see takes a certain syntax. Below are the different parts of a SID.
- An ‘S’ prefix
- Structure revision number
- A 48-bit identifier authority value
- A variable number of 32-bit sub-authority or relative identifier (RID) values
Using my SID in the image below we will break up the different sections to get a better understanding.
The SID Structure:
‘S’ – The first component of a SID is always an ‘S’. This is prefixed to all SIDs and is there to inform Windows that what follows is a SID.
’1′ – The second component of a SID is the revision number of the SID specification. If the SID specification was to change it would provide backwards compatibility. As of Windows 7 and Server 2008 R2, the SID specification is still in the first revision.
’5′ – The third section of a SID is called the Identifier Authority. This defines in what scope the SID was generated. Possible values for this sections of the SID can be:
- 0 – Null Authority
- 1 – World Authority
- 2 – Local Authority
- 3 – Creator Authority
- 4 – Non-unique Authority
- 5 – NT Authority
’21′ – The fourth component is sub-authority 1. The value ’21′ is used in the fourth field to specify that the sub-authorities that follow identify the Local Machine or the Domain.
’1206375286-251249764-2214032401′ – These are called sub-authority 2,3 and 4 respectively. In our example this is used to identify the local machine, but could also be the the identifier for a Domain.
’1000′ – Sub-authority 5 is the last component in our SID and is called the RID (Relative Identifier). The RID is relative to each security principle: please note that any user defined objects, the ones that are not shipped by Microsoft, will have a RID of 1000 or greater.
Security Principles
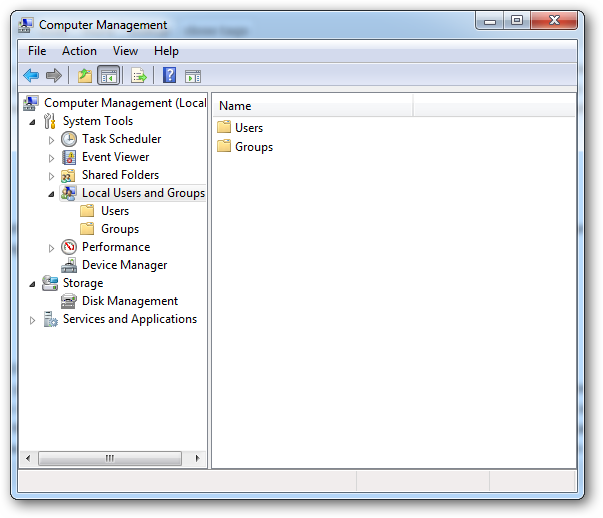
A security principle is anything that has a SID attached to it. These can be users, computers and even groups. Security principles can be local or be in the domain context. You manage local security principles through the Local Users and Groups snap-in, under computer management. To get there, right click on the computer shortcut in the start menu and choose manage.
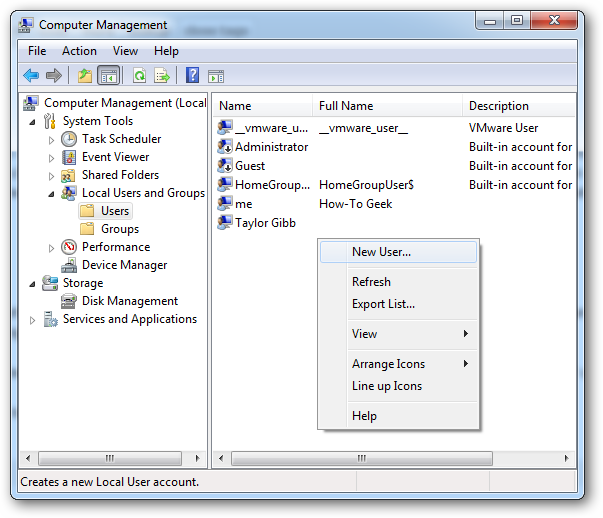
To add a new user security principle, you can go to the Users folder and right click and choose New User.
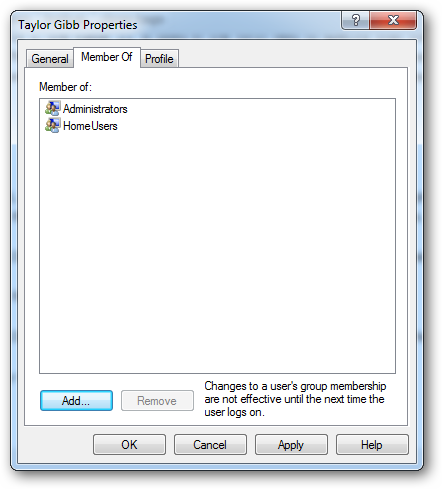
If you double click on a user you can add them to a Security Group on the Member Of tab.
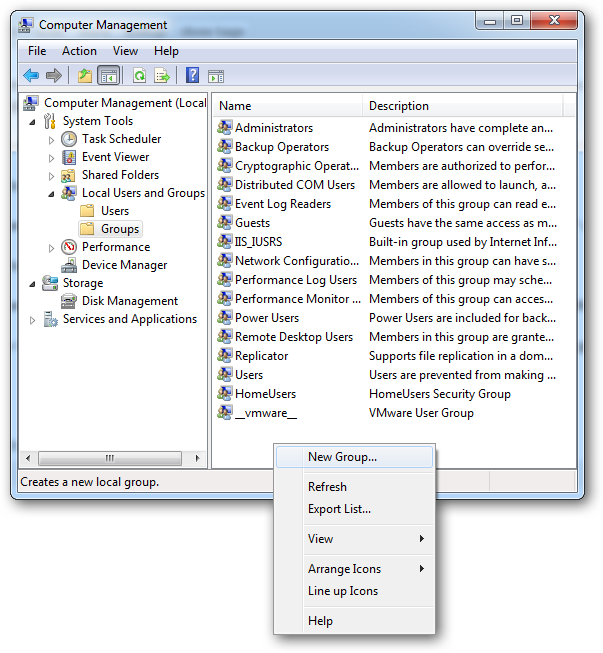
To create a new security group, navigate to the Groups folder on the right hand side. Right click on the white space and select New Group.
Share Permissions and NTFS Permission
In Windows there are two types of file and folder permissions. Firstly, there are the Share Permissions. Secondly, there are NTFS Permissions, which are also called Security Permissions. Securing shared folders is usually done with a combination of Share and NTFS Permissions. Since this is the case, it is essential to remember that the most restrictive permission always applies. For example, if the share permission gives the Everyone security principle read permission, but the NTFS permission allow users to make a change to the file, the share permission will take precedence, and the users will not be allowed to make changes. When you set the permissions, the LSASS(Local Security Authority) controls access to the resource. When you log on, you are given an access token with your SID on it. When you go to access the resource, the LSASS compares the SID that you added to the ACL (Access Control List). If the SID is on the ACL, it determines whether to allow or deny access. No matter what permissions you use, there are differences, so let's take a look to get a better understanding of when we should use what.
Share Permissions:
- Only apply to users who access the resource over the network. They don’t apply if you log on locally, for example through terminal services.
- It applies to all files and folders in the shared resource. If you want to provide a more granular sort of restriction scheme you should use NTFS Permission in addition to shared permissions
- If you have any FAT or FAT32 formatted volumes, this will be the only form of restriction available to you, as NTFS Permissions are not available on those file systems.
NTFS Permissions:
- The only restriction on NTFS Permissions is that they can only be set on a volume that is formatted to the NTFS file system
- Remember that NTFS Permissions are cumulative. That means that a user's effective permissions are the result of combining the user’s assigned permissions and the permissions of any groups the user belongs to.
The New Share Permissions
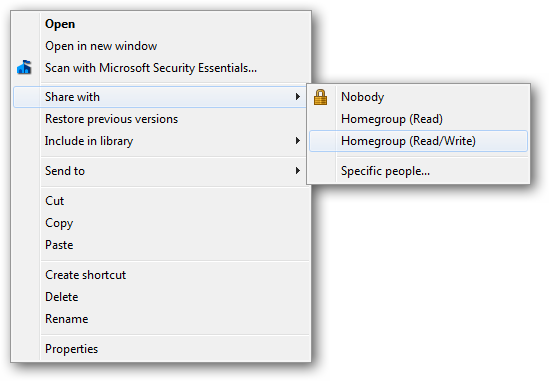
Windows 7 bought along a new “easy” share technique. The options changed from Read, Change and Full Control to Read and Read/Write. The idea was part of the whole Homegroup mentality and makes it easy share a folder for non-computer literate people. This is done via the context menu and shares with your homegroup easily.
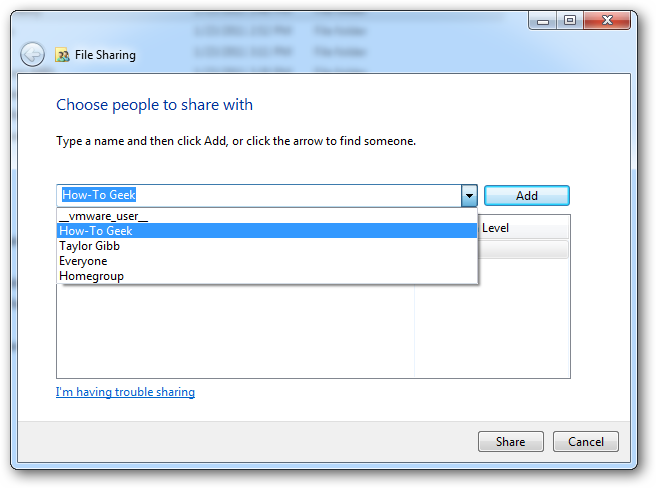
If you wanted to share with someone who is not in the home group, you could always choose the “Specific people…” option. Which would bring up a more “elaborate” dialog where you could specify a user or group.
There are only two permissions, as previously mentioned. Together, they offer an all or nothing protection scheme for your folders and files.
- Read permission is the “look, don’t touch” option. Recipients can open, but not modify or delete a file.
- Read/Write is the “do anything” option. Recipients can open, modify, or delete a file.
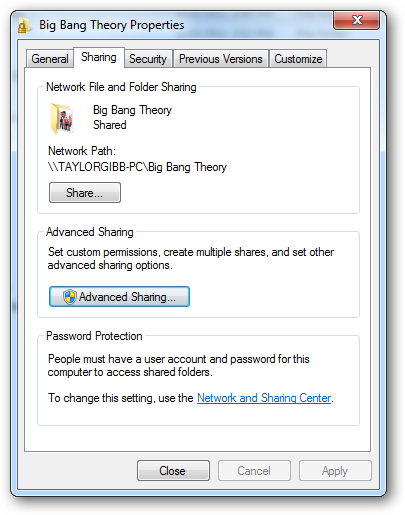
The Old School Permission
The old share dialog had more options, such as the option to share the folder under a different alias. It allowed us to limit the number of simultaneous connections as well as configure caching. None of this functionality is lost in Windows 7, but rather is hidden under an option called “Advanced Sharing”. If you right click on a folder and go to its properties you can find these “Advanced Sharing” settings under the sharing tab.
If you click on the “Advanced Sharing” button, which requires local administrator credentials, you can configure all the settings that you were familiar with in previous versions of Windows.
If you click on the permissions button, you’ll be presented with the 3 settings that we are all familiar with.
- Read permission allows you to view and open files and subdirectories as well as execute applications. However it doesn’t allow any changes to be made.
- Modify permission allows you to do anything that Read permission allows, and it also add the ability to add files and subdirectories, delete subfolders and change data in the files.
- Full Control is the “do anything” of the classic permissions, as it allows for you to do any and all of the previous permissions. In addition, it gives you the advanced changing NTFS Permission, but this only applies on NTFS Folders
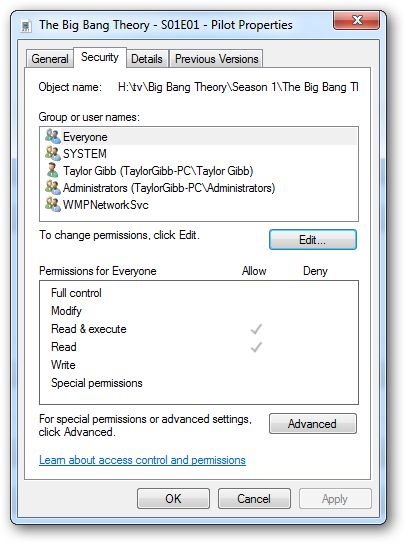
NTFS Permissions
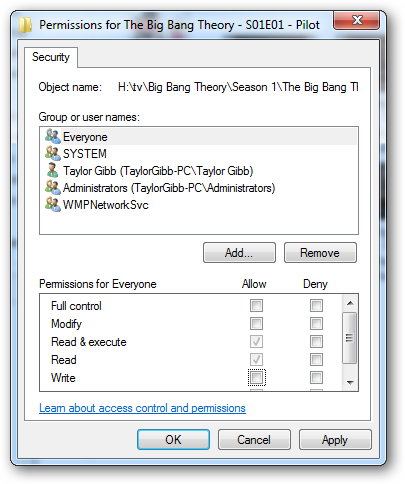
NTFS Permissions allow for very granular control over your files and folders. With that said, the amount of granularity can be daunting to a newcomer. You can also set NTFS permission on a per file basis as well as a per folder basis. To set NTFS Permission on a file, you should right click and go to the file's properties, then go to the security tab.
To edit the NTFS Permissions for a User or Group, click on the edit button.
As you may see, there are quite a lot of NTFS Permissions, so let's break them down. First, we will have a look at the NTFS Permissions that you can set on a file.
- Full Control allows you to read, write, modify, execute, change attributes, permissions, and take ownership of the file.
- Modify allows you to read, write, modify, execute, and change the file’s attributes.
- Read & Execute will allow you to display the file’s data, attributes, owner, and permissions, and run the file if it's a program.
- Read will allow you to open the file, view its attributes, owner, and permissions.
- Write will allow you to write data to the file, append to the file, and read or change its attributes.
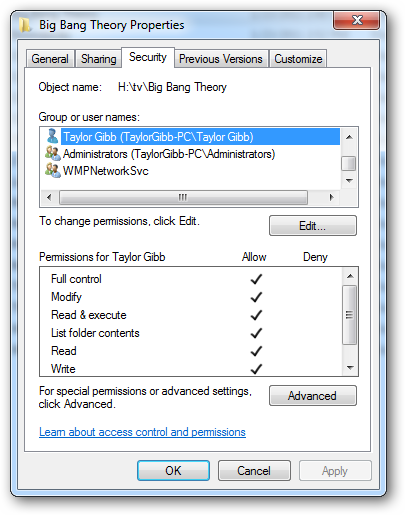
NTFS Permissions for folders have slightly different options, so lets take a look at them.
- Full Control will allow you to read, write, modify, and execute files in the folder, change attributes, permissions, and take ownership of the folder or files within.
- Modify will allow you to read, write, modify, and execute files in the folder, and change attributes of the folder or files within.
- Read & Execute will allow you to display the folder’s contents and display the data, attributes, owner, and permissions for files within the folder, and run files within the folder.
- List Folder Contents will allow you to display the folder’s contents and display the data, attributes, owner, and permissions for files within the folder, and run files within the folder
- Read will allow you to display the file’s data, attributes, owner, and permissions.
- Write will allow you to write data to the file, append to the file, and read or change its attributes.
Summary
In summary, user names and groups are representations of an alphanumeric string called a SID (Security Identifier). Share and NTFS Permissions are tied to these SIDs. Share Permissions are checked by the LSSAS only when being accessed over the network, while NTFS Permissions are combined with Share Permissions to allow a more granular level of security for resources being accessed over the network as well as locally.
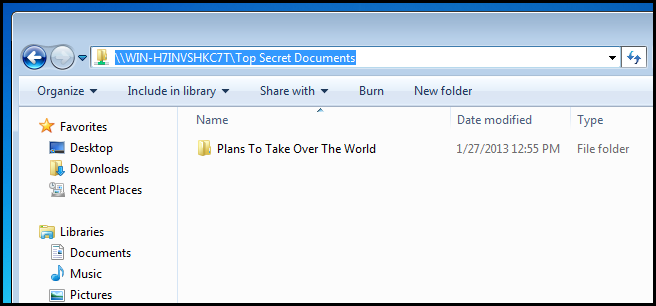
Accessing a Shared Resource
So now that we have learned about the two methods we can use to share content on our PCs, how do you actually go about accessing it over the network? It is very simple. Just type the following into the navigation bar.
\\computername\sharename
Note: Obviously you will need to substitute computername for the name of the PC hosting the share and sharename for the name of the share.
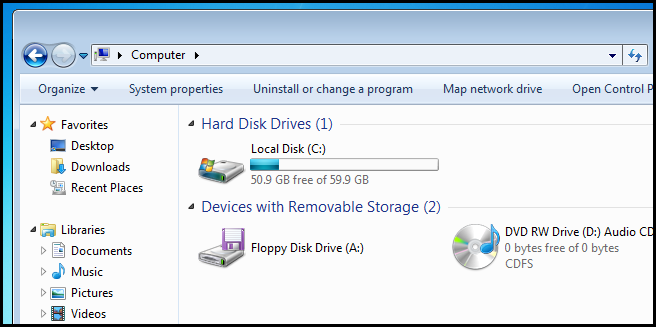
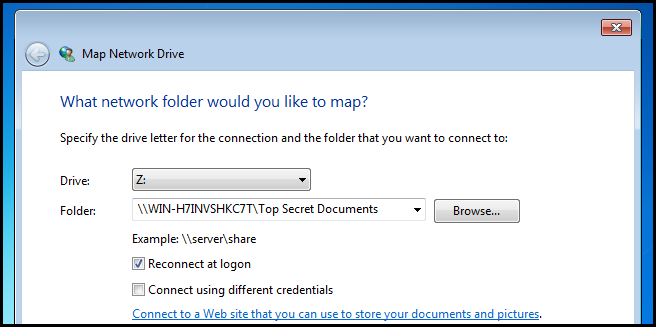
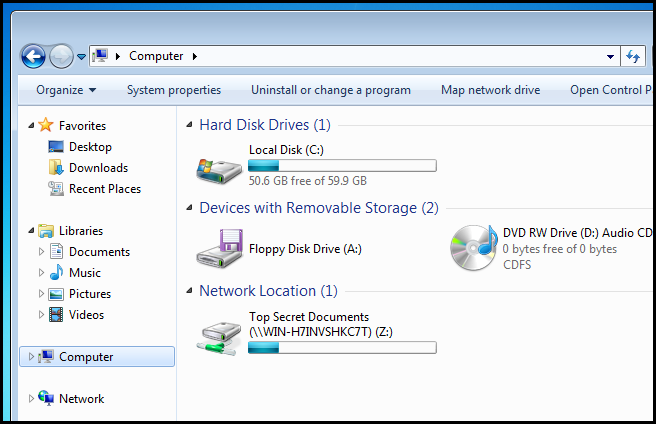
This is great for once off connections, but what about in a larger corporate environment? Surely you don’t have to teach your users how to connect to a network resource using this method. To get around this, you will want to map a network drive for each user, this way you can advise them to store their documents on the “H” drive, rather than trying to explain how to connect to a share. To map a drive, open Computer and click on the “Map network drive” button.
Then simply type in the UNC path of the share.
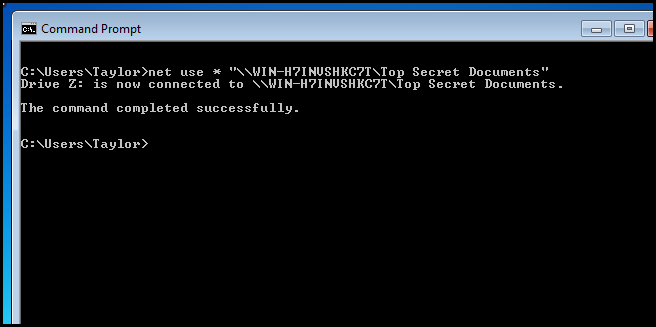
Your probably wondering if you have to do that on every PC, and luckily the answer is no. Rather, you can write a batch script to automatically map the drives for your users at logon and deploy it via Group Policy.
If we dissect the command:
- We are using the net use command to map the drive.
- We use the * to denote that we want to use the next available drive letter.
- Finally we specify the share we want to map the drive to. Notice that we used quotes because the UNC path contains spaces.
Encrypting Files Using the Encrypting File System
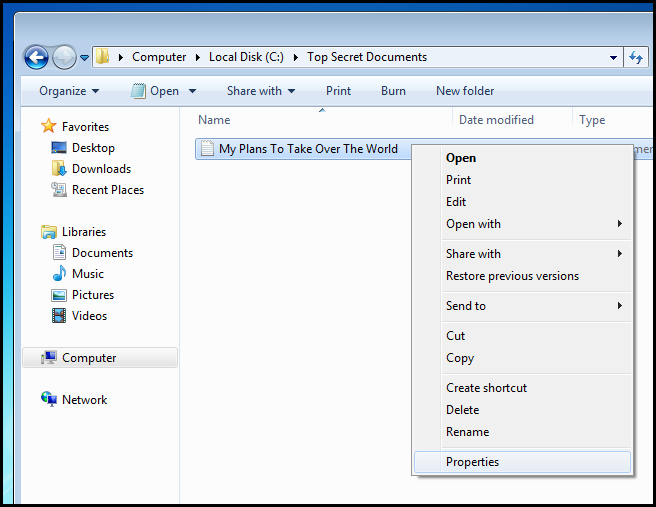
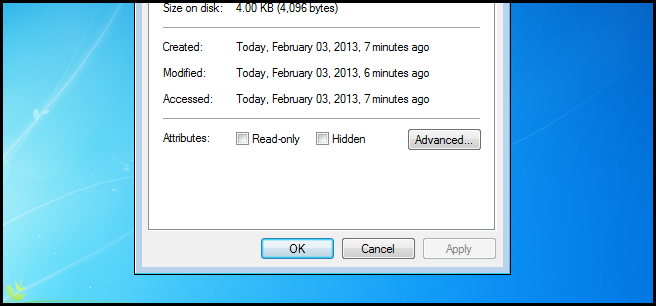
Windows includes the ability to encrypt files on an NTFS volume. This means that only you will be able to decrypt the files and view them. In order to encrypt a file, simply right-click on it and select properties from the context menu.
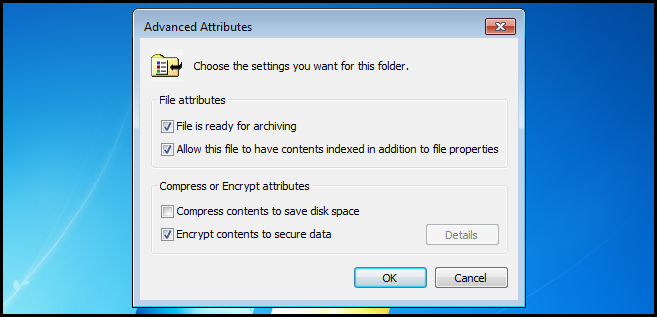
Then click on advanced.
Now check the Encrypt contents to secure data checkbox, then click OK.
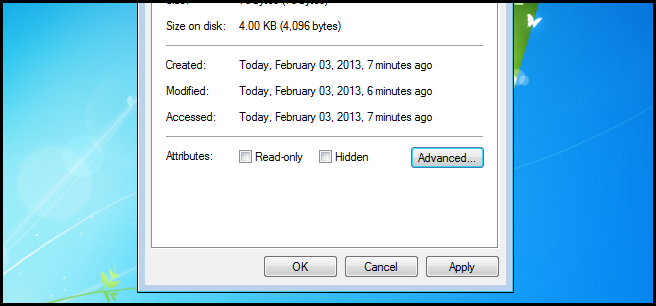
Now go ahead and apply the settings.
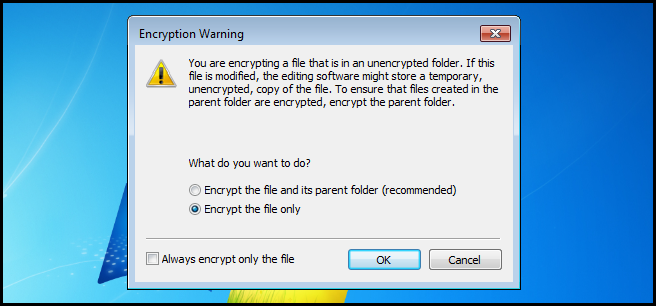
We only need to encrypt the file, but you do have the option of encrypting the parent folder as well.
Take note that once the file is encrypted it turns green.
You will now notice that only you will be able to to open the file and that other users on the same PC will not be able to. The encryption process uses public key encryption, so keep your encryption keys safe. If you lose them, your file is gone and there is no way of recovering it.
Homework
- Learn about permission inheritance and effective permissions.
- Read this Microsoft document.
- Learn why you would want to use BranchCache.
- Learn how to share printers and why you would want to.