Quick Links
AppArmor locks down programs on your Ubuntu system, allowing them only the permissions they require in normal use – particularly useful for server software that may become compromised. AppArmor includes simple tools you can use to lock down other applications.
AppArmor is included by default in Ubuntu and some other Linux distributions. Ubuntu ships AppArmor with several profiles, but you can also create your own AppArmor profiles. AppArmor’s utilities can monitor a program’s execution and help you create a profile.
Before creating your own profile for an application, you may want to check the apparmor-profiles package in Ubuntu’s repositories to see if a profile for the application you want to confine already exists.
Create & Running a Test Plan
You’ll need to run the program while AppArmor is watching it and walk through all its normal functions. Basically, you should use the program as it would be used in normal use: start the program, stop it, reload it, and use all its features. You should design a test plan that goes through the functions the program needs to perform.
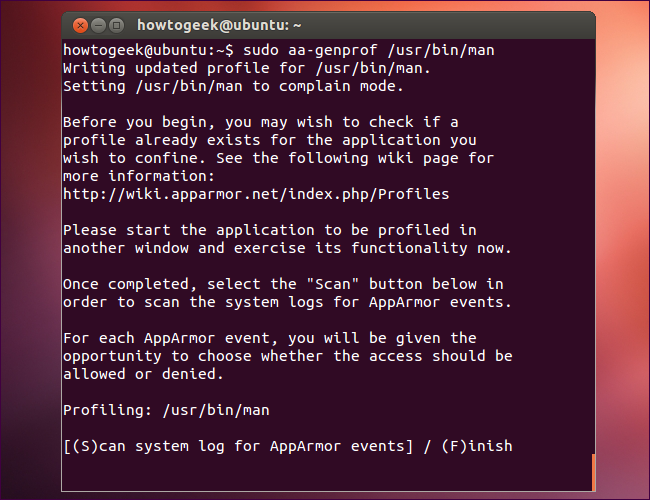
Before running through your test plan, launch a terminal and run the following commands to install and run aa-genprof:
sudo apt-get install apparmor-utils
sudo aa-genprof /path/to/binary
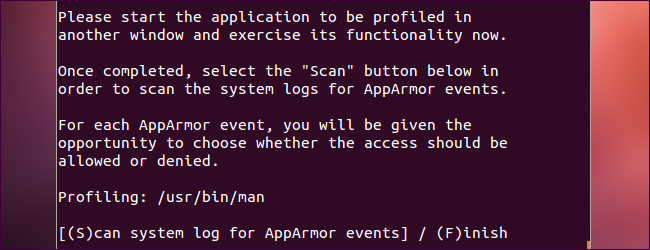
Leave aa-genprof running in the terminal, start the program, and run through the test plan you designed above. The more comprehensive your test plan, the less problems you’ll run into later.
After you’re done executing your test plan, return to the terminal and press the S key to scan the system log for AppArmor events.
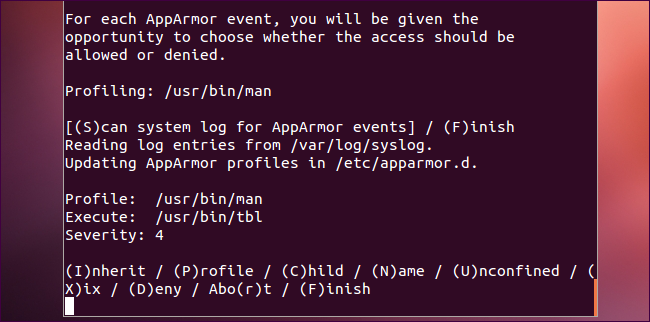
For each event, you’ll be prompted to choose an action. For example, below we can see that /usr/bin/man, which we profiled, executed /usr/bin/tbl. We can select whether /usr/bin/tbl should inherit /usr/bin/man’s security settings, whether it should run with its own AppArmor profile, or whether it should run in unconfined mode.
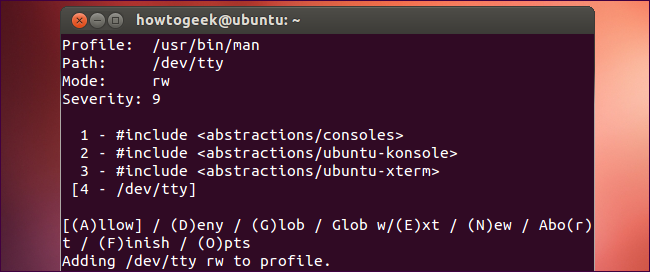
For some other actions, you’ll see different prompts – here we’re allowing access to /dev/tty, a device that represents the terminal
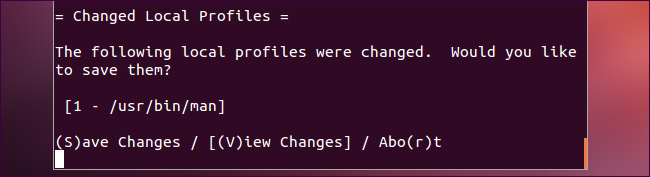
At the end of the process, you’ll be prompted to save your new AppArmor profile.
Enabling Complain Mode & Tweaking the Profile
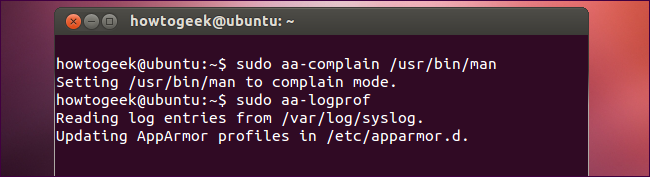
After creating the profile, put it into “complain mode,” where AppArmor doesn’t restrict the actions it can take but instead logs any restrictions that would otherwise occur:
sudo aa-complain /path/to/binary
Use the program normally for a while. After using it normally in complain mode, run the following command to scan your system logs for errors and update the profile:
sudo aa-logprof
Using Enforce Mode to Lock Down the Application
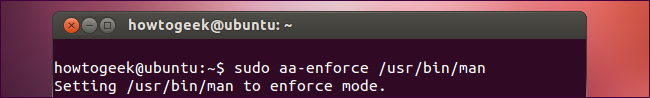
After you’re done fine-tuning your AppArmor profile, enable “enforce mode” to lock down the application:
sudo aa-enforce /path/to/binary
You may want to run the sudo aa-logprof command in the future to tweak your profile.
AppArmor profiles are plain-text files, so you can open them in a text editor and tweak them by hand. However, the utilities above guide you through the process.