Quick Links
Ubuntu’s Grub boot loader lets anyone edit boot entries or use its command-line mode by default. Secure Grub with a password and no one can edit them — you can even require a password before booting operating systems.
Grub 2’s configuration options are split across multiple files instead of the single menu.lst file Grub 1 used, so setting a password has become more complicated. These steps apply to Grub 1.99, used in Ubuntu 11.10. The process may be different in future versions.
Generating a Password Hash
First, we’ll fire up a terminal from Ubuntu’s applications menu.
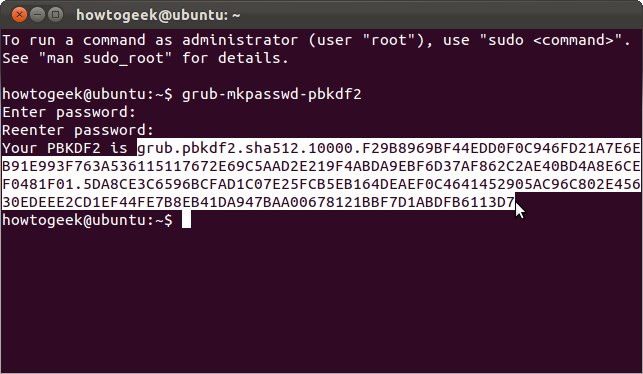
Now we’ll generate an obfuscated password for Grub’s configuration files. Just type grub-mkpasswd-pbkdf2 and press Enter. It’ll prompt you for a password and give you a long string. Select the string with your mouse, right-click it and select Copy to copy it to your clipboard for later.
This step is technically optional — we can enter our password in plain text in Grub’s configuration files, but this command obfuscates it and provides additional security.
Setting a Password
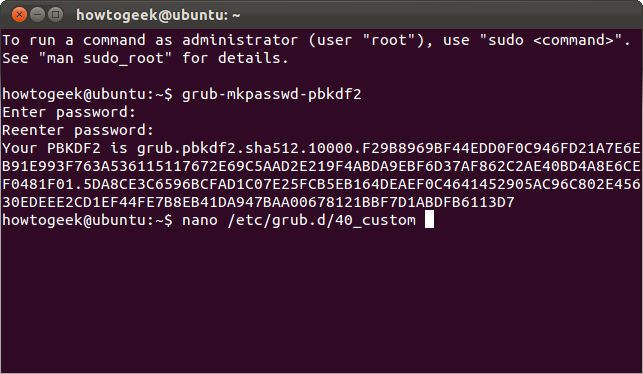
Type sudo nano /etc/grub.d/40_custom to open the 40_custom file in the Nano text editor. This is the place where you should put your own custom settings. They may be overwritten by newer versions of Grub if you add them elsewhere.
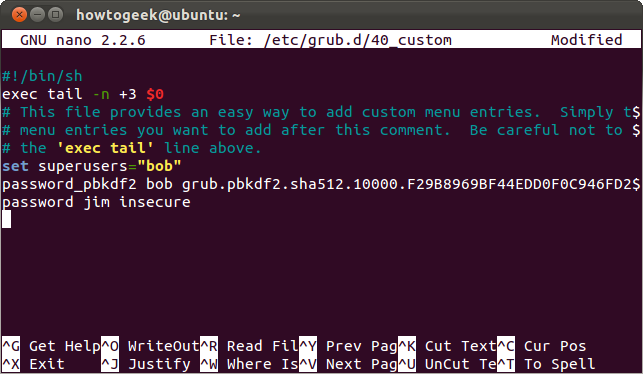
Scroll down to the bottom of the file and add a password entry in the following format:
set superusers=”name”
password_pbkdf2 name [long string from earlier]
Here we’ve added a superuser named “bob” with our password from earlier. We’ve also added a user named jim with an insecure password in plain text.
Note that Bob is a superuser while Jim isn’t. What’s the difference? Superusers can edit boot entries and access the Grub command line, while normal users can’t. You can assign specific boot entries to normal users to give them access.
Save the file by pressing Ctrl-O and Enter, then press Ctrl-X to exit. Your changes won’t take effect until you run the sudo update-grub command; see the Activating Your Changes section for more details.
Password Protecting Boot Entries
Creating a superuser gets us most of the way. With a superuser configured, Grub automatically prevents people from editing boot entries or accessing the Grub command line without a password.
Want to password protect a specific boot entry so that no one can boot it without providing a password? We can do that too, although it’s a bit more complicated at the moment.
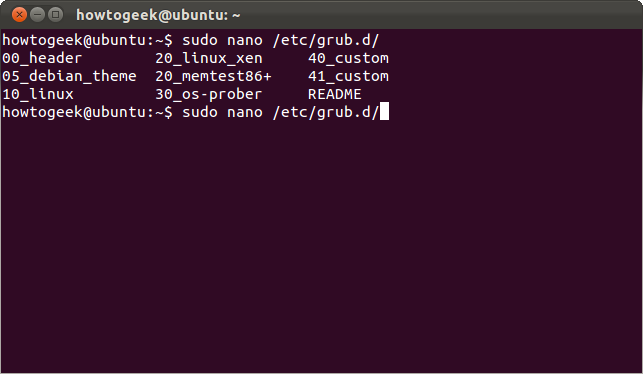
First, we’ll need to determine the file that contains the boot entry you want to modify. Type sudo nano /etc/grub.d/ and press Tab to view a list of the available files.
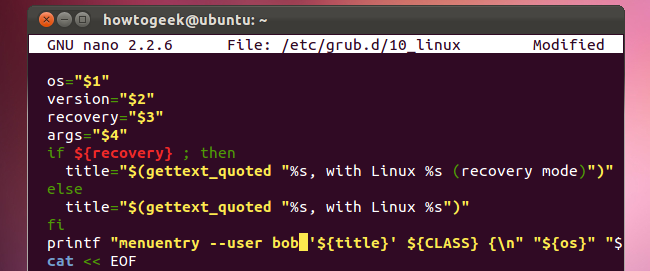
Let’s say we want to password protect our Linux systems. Linux boot entries are generated by the 10_linux file, so we’ll use the sudo nano /etc/grub.d/10_linux command to open it. Be careful when editing this file! If you forget your password or enter an incorrect one, you won't be able to boot into Linux unless you boot from a live CD and modify your Grub setup first.
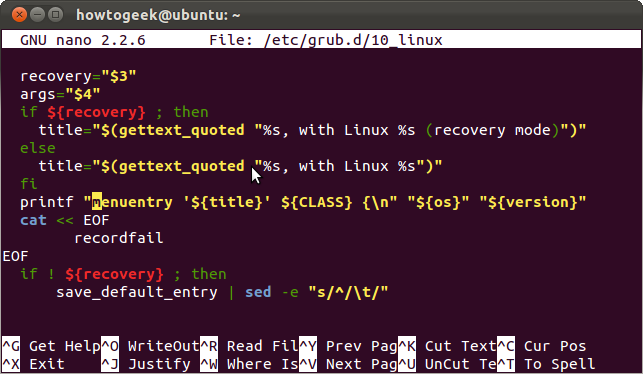
This is a long file with a lot of stuff going on, so we’ll hit Ctrl-W to search for the line we want. Type menuentry at the search prompt and press Enter. You’ll see a line starting with printf.
Just change the
printf “menuentry '${title}'
bit at the start of the line to:
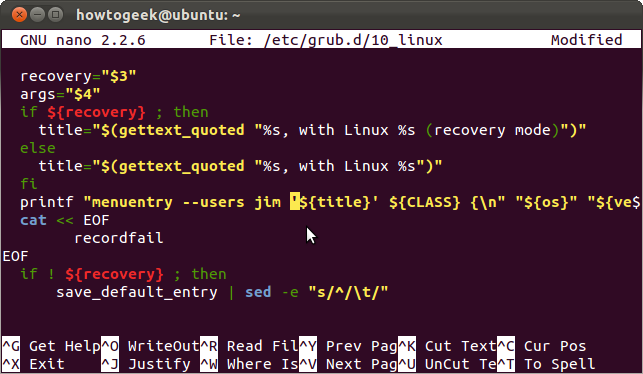
printf “menuentry --users name ‘${title}”
Here we’ve given Jim access to our Linux boot entries. Bob also has access, since he’s a super user. If we specified “bob” instead of “jim,” Jim wouldn’t have any access at all.
Press Ctrl-O and Enter, then Ctrl-X to save and close the file after modifying it.
This should get easier over time as Grub’s developers add more options to the grub-mkconfig command.
Activating Your Changes
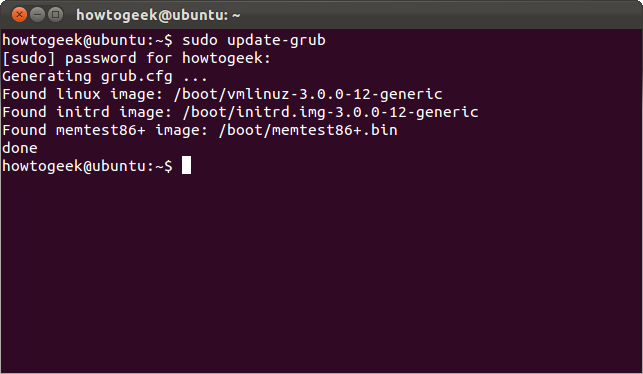
Your changes won’t take effect until you run the sudo update-grub command. This command generates a new Grub configuration file.
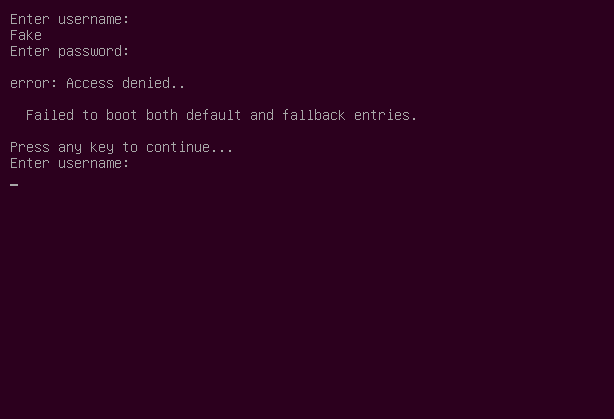
If you password protected the default boot entry, you'll see a login prompt when you start your computer.
If Grub is set to display a boot menu, you won’t be able to edit a boot entry or use command-line mode without entering a superuser's password.